voydstack
678 posts


voydstack
@voydstack
VR @Synacktiv | CTF with @RMUBYGG, @Hexagonctf, @ECSC_TeamFrance 20/21/22/23/24



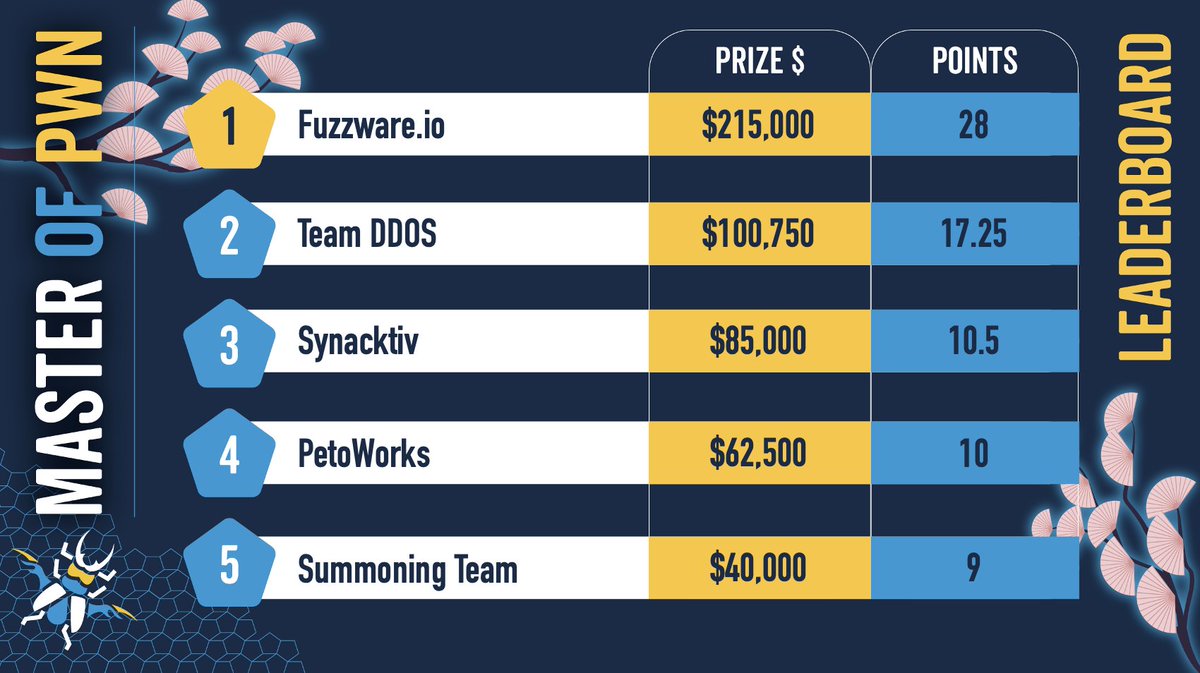
$1,047,000 USD - 76 unique 0-day vulnerabilities - three days of incredible research on display. #Pwn2Own Automotive 2026 had it all: bold exploits, clever techniques, and collisions. Congrats to Fuzzware.io (@ScepticCtf, @diff_fusion, @SeTcbPrivilege), Master of Pwn with $215,500 and 28 points! #P2OAuto

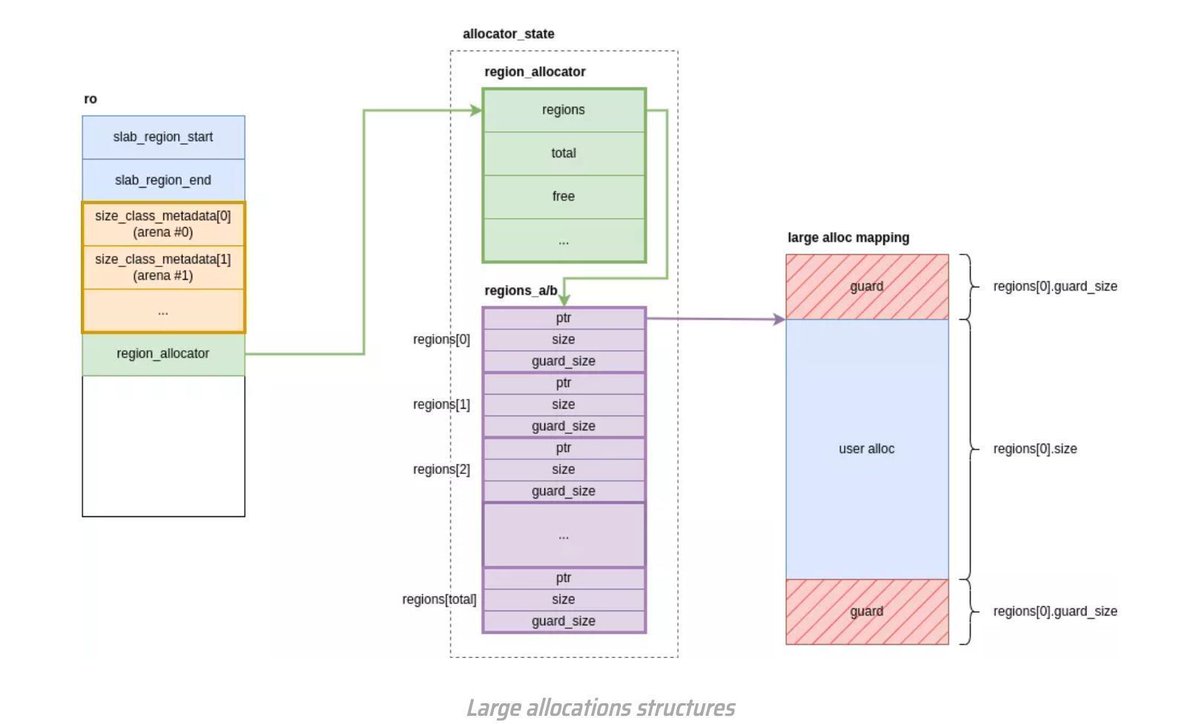
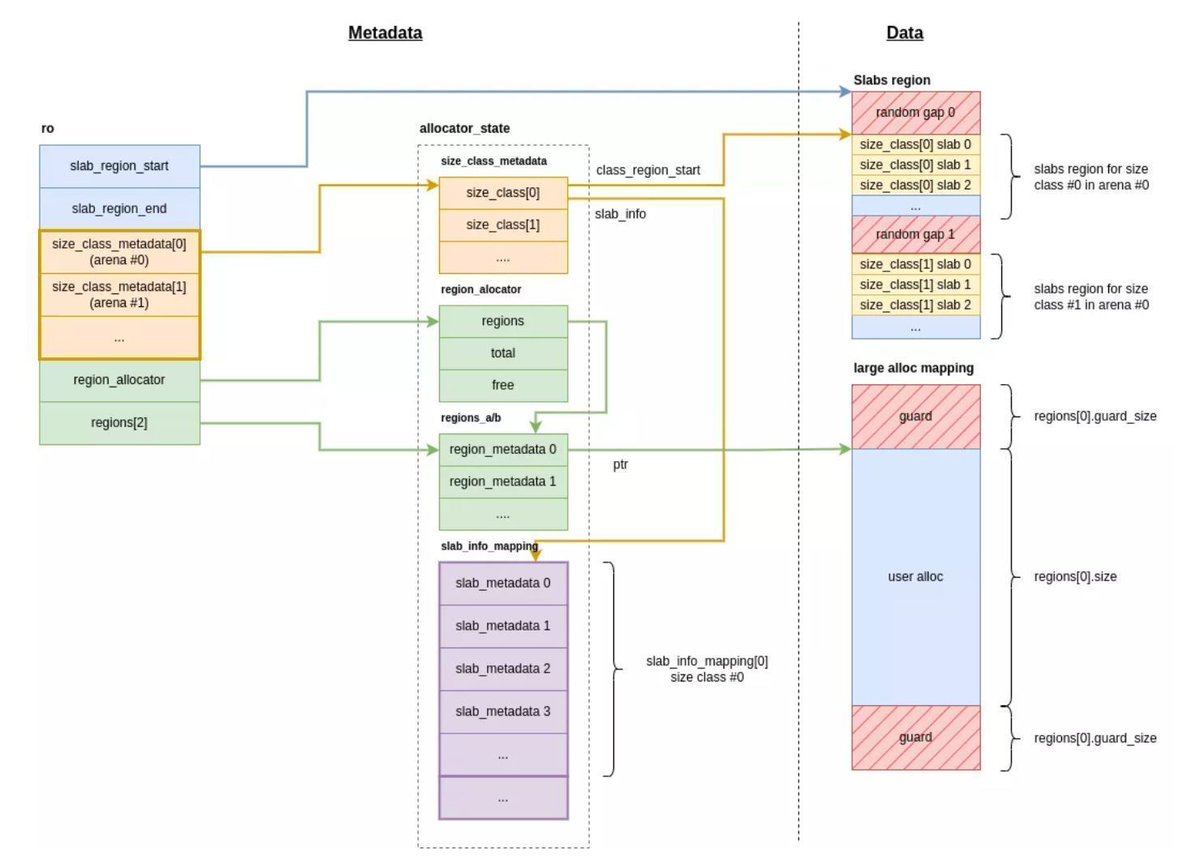
At #Pwn2Own Berlin 2025, a full exploit chain against VMware Workstation was demonstrated via a heap overflow in the PVSCSI controller. Despite Windows 11 LFH mitigations, advanced heap shaping and side-channel techniques enabled a reliable exploit. 🔍 Full technical write-up 👇 synacktiv.com/en/publication…





Verified! @synacktiv targeted the Autel MaxiCharger AC Elite Home 40A with the Charging Connector Protocol/Signal Manipulation add‑on. In Round 2, they exploited one stack‑based buffer overflow, earning $30,000 USD and 5 Master of Pwn points. #Pwn2Own #P2OAuto