0 day exploit
355 posts


0 day exploit
@0day_exploit_
Security Researcher | Crypto auditor and malware analyst 🥰
शामिल हुए Mayıs 2022
746 फ़ॉलोइंग2.6K फ़ॉलोवर्स
पिन किया गया ट्वीट

Top google Dorking
Thread 🧵:👇 Here is how to find sensitive data issues:
1) publicly exposed documents :- site:target.com ext:doc | ext:docx | ext:odt | ext:rtf | ext:sxw | ext:psw | ext:ppt | ext:pptx | ext:pps | ext:csv
#BugBounty #bugbountytips #infosec
English

Huge congratulations for the great achievement sir 💐 making the web3 more secured day by day 🫡
Dmytro Matviiv 🇺🇦@DmytroMatviiv
Thank you, @thedaofund! It’s an honor to be among the ETHSecurity badge holders! And thank you, @d0rsky and the @HackenProof team, for your daily engagement and support! More security ideas and work are coming!
English

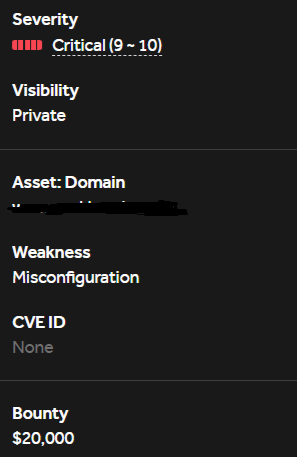
How I found a Critical ($100k) bug that could allow an attacker to drain the entire pool in under an hour and end on an information already known issue🥲
Read full article at ;-@0day_exploit/critical-100k-bug-that-could-allow-an-attacker-to-drain-the-entire-pool-in-under-an-hour-962b7e4e2ba4" target="_blank" rel="nofollow noopener">medium.com/@0day_exploit/…

English

@adeolRxxxx This is the original report you got a duplicate of. Read my story about how I argued and ended up on information rather than paying 100k$ 😰
English


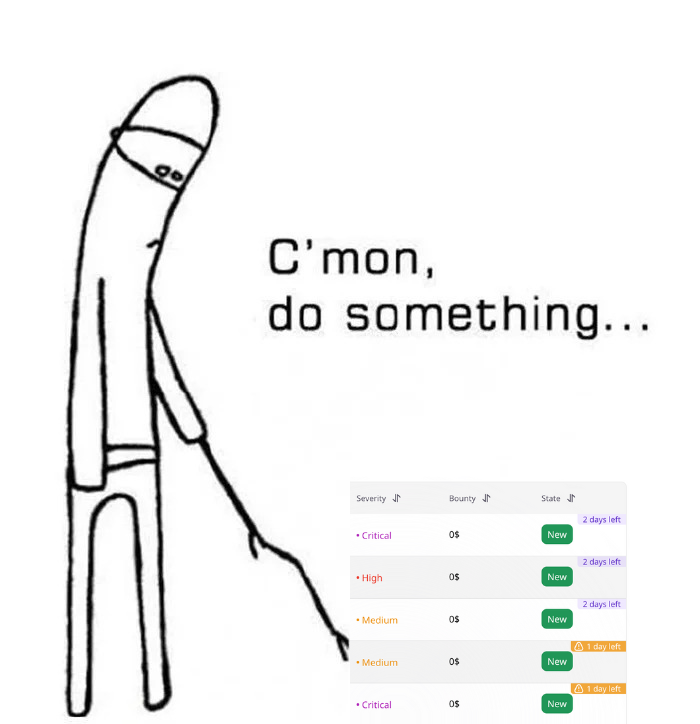
So basically, I have not been resting as I am currently competing in contests and also consistent in bug bounties.
> So I think it would be nice to share my dups with the public for those who wanna learn.
> But bug bounties have been a hell hole, or maybe let me say crazy.
A bounty dropped last week in the heat of the day. I was asleep when I got pinged by my tool.
I quickly woke up, checked, and saw it was in DLT. I have been preparing all my life for this.
4 hours just after this dropped on @HackenProof , I was able to find a critical that could allow an attacker to drain the entire pool in a single transaction by forging a block.
I quickly wired an end-to-end POC to prove this issue, even estimating the time it would take the attacker.
But unfortunately, I was met with "this issue has been found by another whitehat", bro, 4 hours??
Here, if you wanna learn:
github.com/blessingblockc…
English

@nisedo_ Bro your just reported I am waiting for 15 days 2 report is form 2025 😮💨 more than 4 month 🫣
English

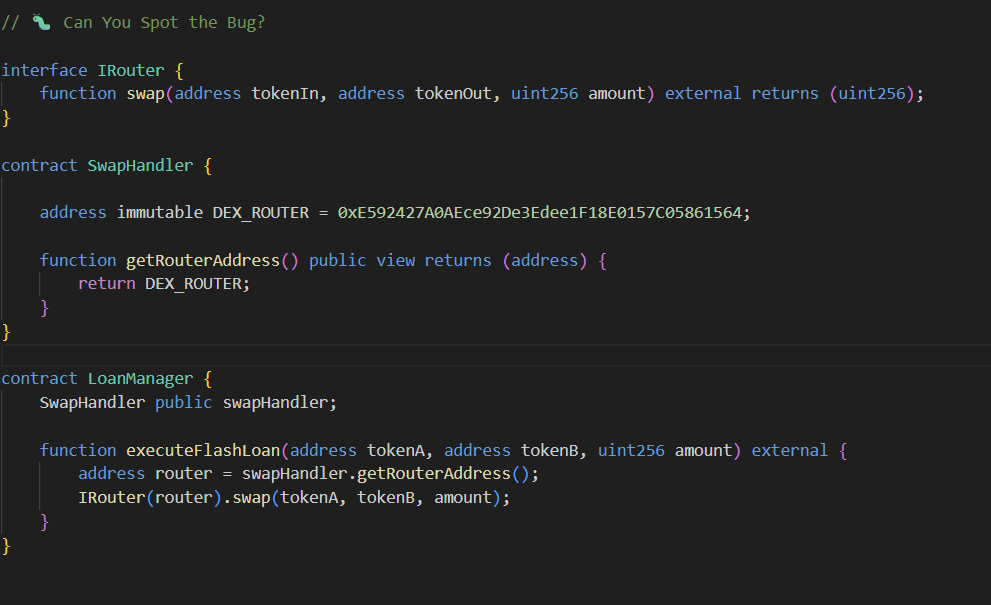
@HackenProof swapHandler is never initialized, so executeFlashLoan calls getRouterAddress() on the zero address (no code there) and always reverts
English

@HackenProof Permanent Withdrawal DoS via Liquidity Hostage Attack
English

@GodfatherOrwa @Bugcrowd Congratulations brother, many many happy returns of the day 🥳 🎉 🎆
English

Just submitted my birthday P1 😍 on @Bugcrowd
for admin full access via GitHub leak
#bugbounty
English
0 day exploit रीट्वीट किया

Thread 🧵:📷 Here is how I Do my Recon fast automated bug bounty
1) we are not using any kind of paid service to do automation 🔥
2) We use shell.cloud.google.com for hacking open terminal
#infosec #bugbountytips #Hacking #cybersecurity
English

Findsomething extension
it’s give more than amazing results just in 1 press
Keep it running and I assure you , it will save a lot of work for you / find some sensitive keys so quick
chromewebstore.google.com/detail/findsom…
#bugbounty #bugbountytip #bugbountytips
English

@encrypt3dpoison @redbull I had forgot thanks for reminding though it's already 2 year 😵 😵💫
English

@0day_exploit_ @redbull Ask intigriti to connect with them, there team helps a lot
English

Thanks @0day_exploit_ Found critical misconfiguration to whole 0 click ATO #BugBounty #bugbountytips #infosecurity
English

5) exploit using jsleak
cat test.txt | jsleaks -s -l -k
github.com/byt3hx/jsleak
6) expoit by nuclei
cat test.txt | nuclei -t credentials-disclosure-all.yaml -c 30
English

Top JS Bugs
Thread 🧵:👇 Here is how to find Exposed :
1) collect all the js endpoint by lazyegg
github.com/schooldropout1…
- using automatic tools find sensitive data
chromewebstore.google.com/detail/endpoin…
#BugBounty #bugbountytips #infosec
English