D Mitch me-retweet
D Mitch
936 posts


D Mitch me-retweet
D Mitch me-retweet

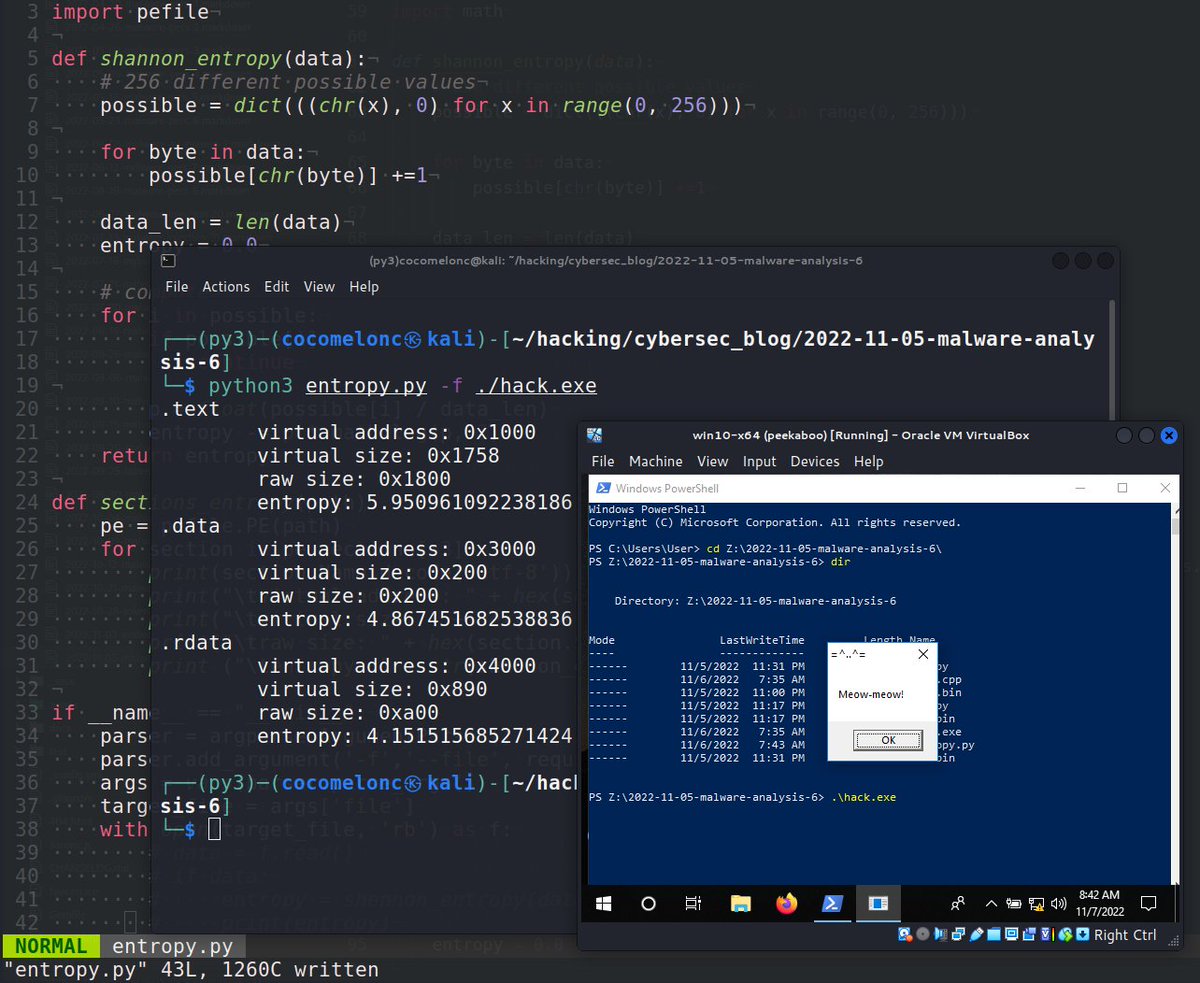
🦟 Malware Analysis: Writing a simple Python Script to achieve Shannon Entropy.
Blog: cocomelonc.github.io/malware/2022/1…
#malware #infosec
English
D Mitch me-retweet

🚨PoC Code to Exploit the IngressNightmare Vulnerabilities (CVE-2025-1097, CVE-2025-1098, CVE-2025-24514, and CVE-2025-1974)
darkwebinformer.com/poc-code-to-ex…
English
D Mitch me-retweet

Berkeley's Number Theory
by Richard E Borcherds, 1998 Fields Medalist
youtube.com/playlist?list=…

English
D Mitch me-retweet

I'm excited to introduce my FREE AI Pandas Data Analyst Copilot which created a data analysis report with dozens of charts from my questions in under 30 seconds.
Today, I'll share with you how to automate data analysis with my Pandas AI Agent + Copilot, which is available on GitHub.
I'll guide you through setting up the Copilot app, creating dozens of data analysis charts from any CSV or Excel file, and interacting with your data live.
This AI is a BIG help!
Table of Contents:
00:00 Introduction to the App
02:24 Setting Up the App
04:25 Using the App
08:58 Understanding the Python Code
Github to AI Data Science Team (app is in the apps folder): github.com/business-scien…
Get the Code and Future Updates by Joining my Python AI/ML Tips Newsletter: learn.business-science.io/free-ai-tips
===
Want to learn how to build AI projects companies actually want? (live Python Code)
On Wednesday, April 9th, I'm sharing one of my best AI Projects: Time Series Forecasting with AI
Register here (500 Seats): learn.business-science.io/ai-register
English
D Mitch me-retweet
D Mitch me-retweet

MIT's "Statistics for Applications"
Lecture Videos: youtube.com/playlist?list=…
Lecture Slides: ocw.mit.edu/courses/18-650…

English
D Mitch me-retweet

multi-agent-orchestrator - Flexible and powerful framework for managing multiple AI agents and handling complex conversations github.com/awslabs/multi-…
English
D Mitch me-retweet

#Red_Team_Tactics
1. Dumping lsass without mimikatz with the exfiltration of the data using FAKE ntp packets
github.com/Aur3ns/lsassSt…
2. Bypassing Windows Defender Application Control with Loki C2
securityintelligence.com/x-force/bypass…
3. Exploiting CVE-2024-0402 in GitLab
blog.doyensec.com/index.html
English

Excellent book. One of the first to really open my eyes decades ago…
TheSecMaster@TheSecMaster1
Reversing: Secrets of Reverse Engineering!! Download now!! 👇 drive.google.com/file/d/1LbTCD-…
English
D Mitch me-retweet
D Mitch me-retweet

7 must-know runtime complexities for coding interviews:
1. 𝐎(1) - 𝐂𝐨𝐧𝐬𝐭𝐚𝐧𝐭 𝐭𝐢𝐦𝐞
- The runtime doesn't change regardless of the input size.
- Example: Accessing an element in an array by its index.
2. 𝐎(𝐥𝐨𝐠 𝐧) - 𝐋𝐨𝐠𝐚𝐫𝐢𝐭𝐡𝐦𝐢𝐜 𝐭𝐢𝐦𝐞
- The runtime grows slowly as the input size increases. Typically seen in algorithms that divide the problem in half with each step.
- Example: Binary search in a sorted array.
3. 𝐎(𝐧) - 𝐋𝐢𝐧𝐞𝐚𝐫 𝐭𝐢𝐦𝐞
- The runtime grows linearly with the input size.
- Example: Finding an element in an array by iterating through each element.
4. 𝐎(𝐧 𝐥𝐨𝐠 𝐧) - 𝐋𝐢𝐧𝐞𝐚𝐫𝐢𝐭𝐡𝐦𝐢𝐜 𝐭𝐢𝐦𝐞
- The runtime grows slightly faster than linear time. It involves a logarithmic number of operations for each element in the input.
- Example: Sorting an array using quick sort or merge sort.
5. 𝐎(𝐧^2) - 𝐐𝐮𝐚𝐝𝐫𝐚𝐭𝐢𝐜 𝐭𝐢𝐦𝐞
- The runtime grows proportionally to the square of the input size.
- Example: Bubble sort algorithm which compares and potentially swaps every pair of elements.
6. 𝐎(2^𝐧) - 𝐄𝐱𝐩𝐨𝐧𝐞𝐧𝐭𝐢𝐚𝐥 𝐭𝐢𝐦𝐞
- The runtime doubles with each addition to the input. These algorithms become impractical for larger input sizes.
- Example: Generating all subsets of a set.
7. 𝐎(𝐧!) - 𝐅𝐚𝐜𝐭𝐨𝐫𝐢𝐚𝐥 𝐭𝐢𝐦𝐞
- Runtime is proportional to the factorial of the input size.
- Example: Generating all permutations of a set.
♻️ Repost to help others in your network.

English
D Mitch me-retweet

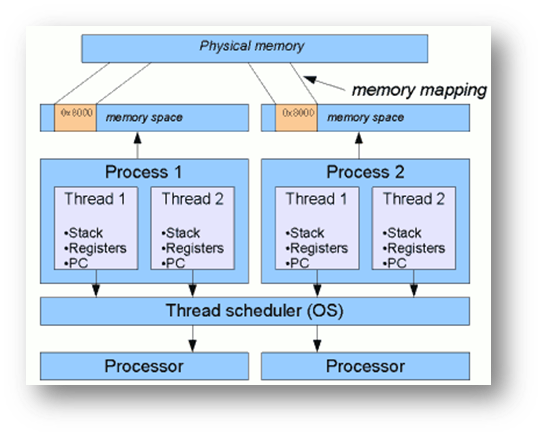
🧵 Pointers - CPU/Memory View
Used the wonderful CPU state-machine animation and recorded a lecture on what pointers are and how one should imagine them to be...
Here is a snap from the lecture.
Here are some points to remember about pointers -
✅ A Pointer is a Number.
✅The number is interpreted as an address.
Dereferencing a Pointer:
✅ If that number is put on the Data Bus - It is a data pointer.
✅ If that number is put in the PC - It is a function pointer.
✅ If there is no information about the datatype of the content at the address, it is a void pointer! Just plain address...
The lecture goes into more details. I never understood why pointer became a dreaded concept/topic. To me it just looks very logical.
Full lecture is part of the course (link below).

Piyush Itankar@_streetdogg
What does the CPU internally do? Check out the animation... The dance goes like - 1. Fetch 2. Decode 3. Execute 4. Memory Access 5. Write Back See it in action here: eseo-tech.github.io/emulsiV/
English
D Mitch me-retweet
D Mitch me-retweet
D Mitch me-retweet

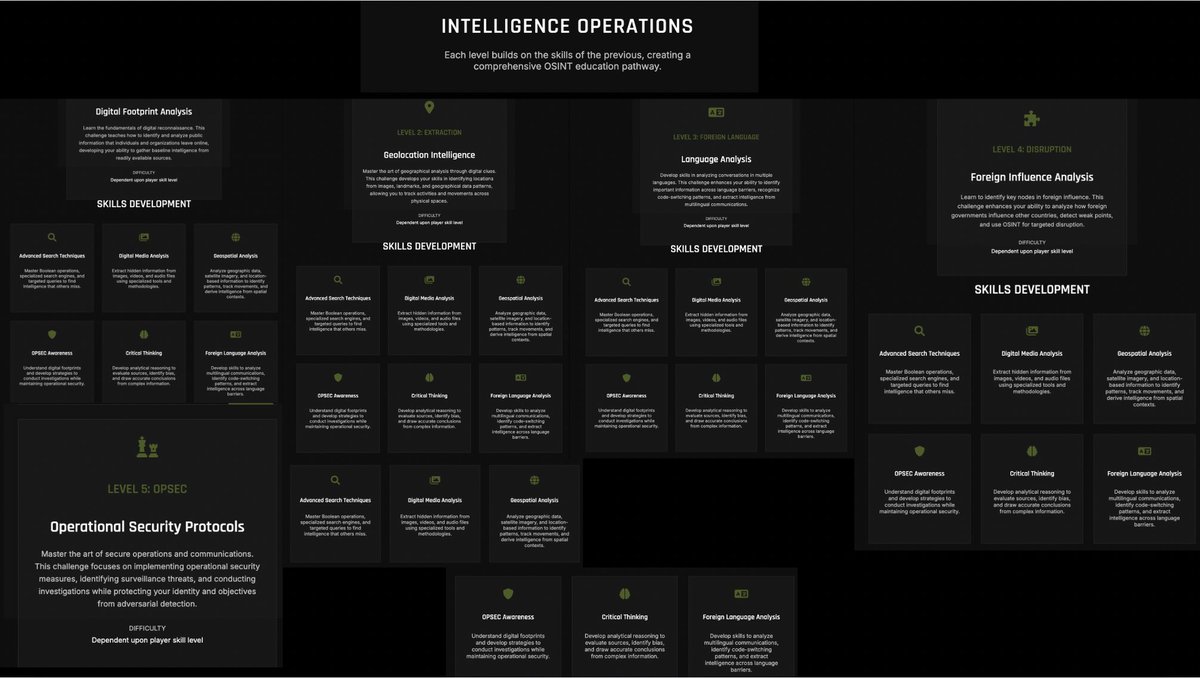
Online platform for skill testing in OSINT and cyber intelligence:
1: Digital Footprint Analysis
2: Geolocation Intelligence
3: Language Analysis
4: Foreign Influence Analysis
5: Operational Security Protocols
limitless-osint.com/challenges
Creator @UnShelledSec
#osint #socmint
English
D Mitch me-retweet
D Mitch me-retweet
D Mitch me-retweet