

Rajnish
5.5K posts

@Digits3c
Mostly Cyber and i forgot what else.. #ADHD











Marcus Hutchins, the guy famous for stopping the WannaCry Ransomware, probably has the best take on Mythos doing vulnerability research

JUST IN: Goldman Sachs is reportedly ramping up its cyber defenses in preparation for Claude Mythos.

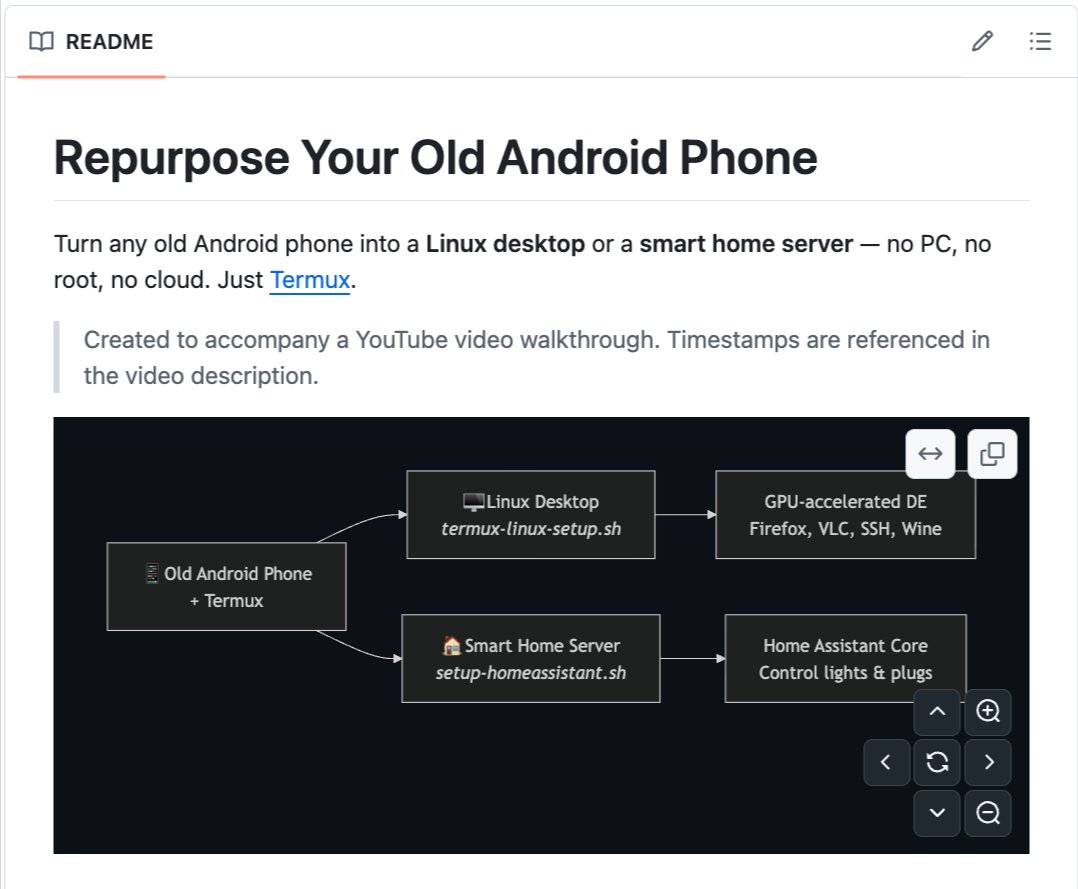
An Expedited Strategy Briefing on Mythos, Glasswing, and building a security program for what comes next, by 250 CISOs, and the wider community. It is still a draft, with some design incomplete, but we felt it was imperative to release. Link: labs.cloudsecurityalliance.org/mythos-ciso/




Respected sir maybe there was a communication issue but the way I remmeber the last 3 questions of my cross examination this evening - Do you feel remorse - No Are you sorry about what you said- No If you tender an unconditional apology this matter will be looked at differently - No I can’t as the apology would not be sincere. Also it would set a terrible precedent for other artists & their freedom.