Raymo
16.6K posts

Raymo
@Filterdog1
Just looking for the truth. David Baldacci fan

Melania Trump's new project is a beehive shaped like the White House. 🐝 tmz.me/TwqNe7u




LIVE AT 7PM ET rumble.com/v78y8xm-thinki…











The Iranian foreign minister will not hold any negotiations with the Trump regime in Islamabad and will merely convey Iran’s considerations and views regarding the end of the war to the Pakistani side. This meeting is a response to General Asim Munir’s trip to Tehran, and I have been informed that no negotiations with any Americans are planned during this visit.

*LEAVITT: IRANIANS REACHED OUT, ASKED FOR IN-PERSON TALKS *LEAVITT: WITKOFF, KUSHNER TO DEPART TOMORROW MORNING *LEAVITT: VANCE TO BE STANDING BY IN US ALONG W/ TRUMP, RUBIO *LEAVITT: IRAN TALKS HOPEFULLY PRODUCTIVE


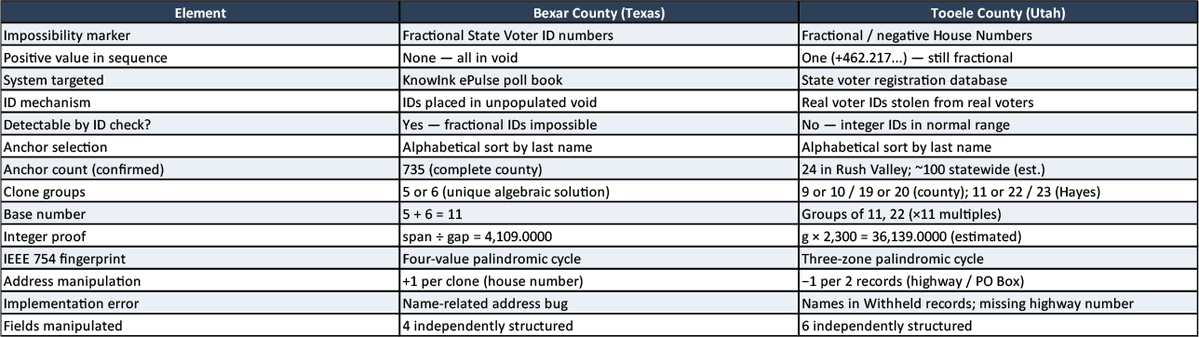
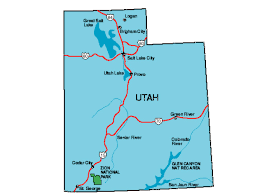
Two months ago I found mathematically proven election fraud in Bexar County, Texas. Fake voter records, generated by an algorithm, injected into the official poll book. Not suspected. Not alleged. Proven — arithmetically, irreducibly, in the file the county was legally required to hand over. Criminal intent visible in the structure of the data itself. Last night I found the same algorithm in Utah. I need to be precise about what "same algorithm" means because this is not a pattern-matching claim or an inference. Same alphabetical anchor selection from the complete voter file. Same uniform arithmetic spacing with a perfect integer closure proof. Same IEEE 754 floating-point fingerprint — the machine-level signature of the same arithmetic loop executing in the same alternating forward-and-reverse pass architecture. Same base-11 clone group structure. Same class of implementation failures at edge cases that expose the underlying code. The only differences between the two are which fields were targeted and the parameter values. Everything underneath is identical. Utah is actually worse than Texas in one critical respect. In Texas, the fake records carried fractional voter ID numbers — impossible values placed in an empty void in ID space. Detectable if you knew to look. In Utah, the fake records carry real voter ID numbers. Numbers stolen from real, named, registered voters, camouflaged inside the normal populated ID range. And when you cross-reference those IDs against the voter history sheet — the official government record of who voted and when — 78% of them show up. Attached to completely different names. Ballots were cast under these IDs. This is not a registration anomaly. It is a voting record. So here is the question. Texas and Utah. Different counties. Different databases. Different fields targeted. Same algorithm running underneath both. What do they have in common? In Bexar County, Texas, KnowInk poll pads were used, and those poll pads connect to the ePulse server. That is a confirmed, documented fact. As for Utah: @wdaugherity confirmed to me today that while a small number of Utah counties do not use e-pollbooks, and Kane County uses ES&S ExpressPoll, all the remaining Utah counties do use KnowInk. ePulse is a server-based system — not software isolated on a county computer. If malicious code were running on that server, it would not need a conspiracy between Texas and Utah to appear in both places. It would just need to run. That is not an assertion that such code is running there. It is a statement about what the architecture makes possible, and why the common infrastructure is the right place to look. ePulse operates across 29 states. I want to be careful about one further point. My earlier peer-reviewed research documented a structural preference for repunit numbers — 1, 11, 111, 1,111 — in New York voter roll algorithms, and the same base-11 architecture appears in both Texas and Utah. That recurrence across three states is notable and warrants investigation, but New York is a stylistic similarity, not an identical forensic signature. Texas and Utah share the same algorithm. New York shares a mathematical preference that may reflect the same design philosophy or the same hand. The distinction matters. When identical fraud appears across multiple independent client systems, you do not start by looking for a conspiracy among the clients. You start with the common infrastructure. That is not a conclusion. It is the correct first question.