Tweet Disematkan
🖤ֆǟʍǟɛʟ🐼
154.7K posts


🖤ֆǟʍǟɛʟ🐼
@FragmentedSoul5
#OreoSec 🎭 the #Truth is well HïÐÐêñ ïñ þlåïñ §ïgh†. #OpSec ł₦₣Ø₴Ɇ₵ It's easier to fool people than to convince them that they have been fooled.#INFP #xuᴎi⅃ 🐧
🕍🦉 ֆօʟօʍօռ'ֆ ₮Ɇ₥₱ⱠɆ 🦉🕍 Bergabung Ocak 2017
722 Mengikuti2.7K Pengikut
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet

Two guys ran an entire hacking operation in a PRISON for months
In 2015, two prisoners in Ohio were assigned to a recycling program where they dismantled old computers
Instead of scrapping the parts, they started stealing them
Carried components over 1,100 feet past guards, metal detectors, and multiple security checkpoints
Then built two working PCs and hid them behind a plywood board in the ceiling of a training room closet
They ran cables from the ceiling into the prison's own network
Stole login credentials from an employee by watching him type his password
Set up Bitcoin wallets, Stripe accounts, bank accounts and credit card applications using another inmate's stolen identity
Downloaded VPNs, the Tor browser, password cracking tools and what investigators called "a large hacker's toolkit"
Created fake security passes to access restricted areas of the prison
This entire operation ran for months
They only got caught because one of the computers used so much bandwidth it triggered an automatic alert
The Inspector General said it was "almost as if it's an episode of Hogan's Heroes"
Two guys with recycled computer parts and a ceiling tile built a cybercrime operation inside a state prison




English
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet

🚨 Hackers Using Google Cloud Storage to Bypass Email Filters and Deliver Remcos RAT
Source: cybersecuritynews.com/hackers-using-…
Cybercriminals are always looking for smarter ways to bypass security, and their latest method is both simple and effective.
The campaign starts with phishing emails linking to pages hosted on storage.googleapis[.]com, a legitimate Google domain.
These pages mimic Google Drive login screens with branded logos and file icons for PDF, DOC, SHEET, and SLIDE documents.
Victims are prompted to sign in to “view a document in Google Drive,” unaware that the page is built to harvest their email address, password, and one-time passcode. After the fake login, the victim is tricked into downloading a JavaScript file named Bid-P-INV-Document.js.
#cybersecuritynews #cyberattacknews

English
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet

process where event.type == "start" and process.name :"SnippingTool.exe" and process.args: ("ms-screensketch:edit?&filePath=%5C%5C*", "ms-screensketch:edit?&filePath=http*", "ms-screensketch:edit?&filePath=\\\\*")
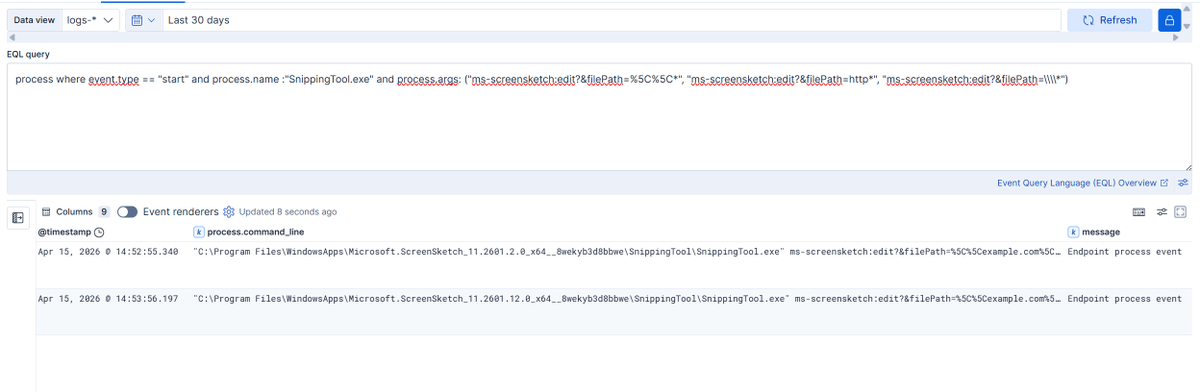
BlackArrow@BlackArrowSec
Microsoft has addressed a one-click NTLM leak vulnerability affecting Windows Snipping Tool (CVE-2026-33829), discovered by our researcher Marcos Díaz (@Calvaruga). ➡️ Read the write-up: github.com/blackarrowsec/… ➡️ Microsoft bulletin: msrc.microsoft.com/update-guide/v…
English
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet

Wars are never about to save or protect the people
Its about Profit, Money and Control.
The rich get richer
The poor gets poorer
Peace is oppression
Freedom is prison.
The world will never know Peace.
#Anonymous for #Justice
English
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet
🖤ֆǟʍǟɛʟ🐼 me-retweet

GitHub - zeroc00I/LLM-anonymization: Reverse proxy for Claude Code that anonymizes sensitive pentest data (IPs, hashes, credentials, hostnames, PII) before it reaches Anthropic. Dual-layer detection: local Ollama LLM + regex safety net, with per-engageme github.com/zeroc00I/LLM-a…
English