Noah McDonald
71 posts

Noah McDonald
@TheIceRoot
GCP Consultant @googlecloud | Ex-Unit42 | Cloud Security | @[email protected]
Bergabung Mart 2022
144 Mengikuti78 Pengikut
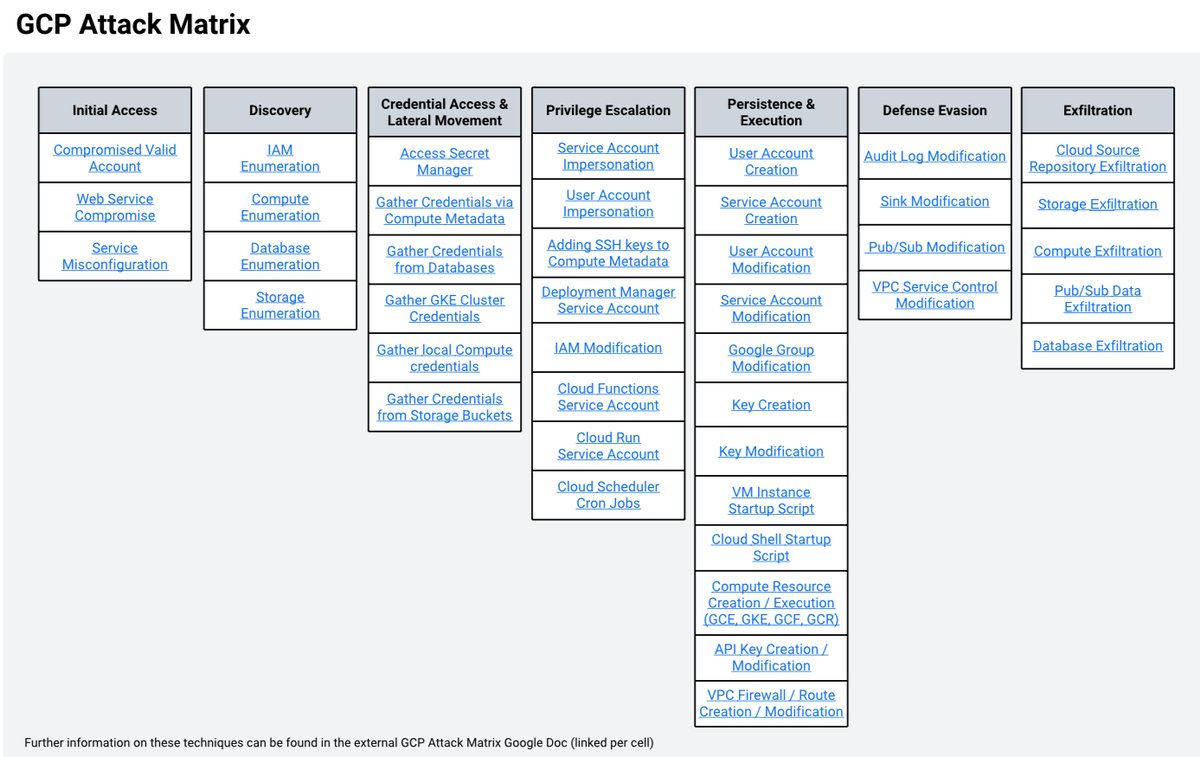
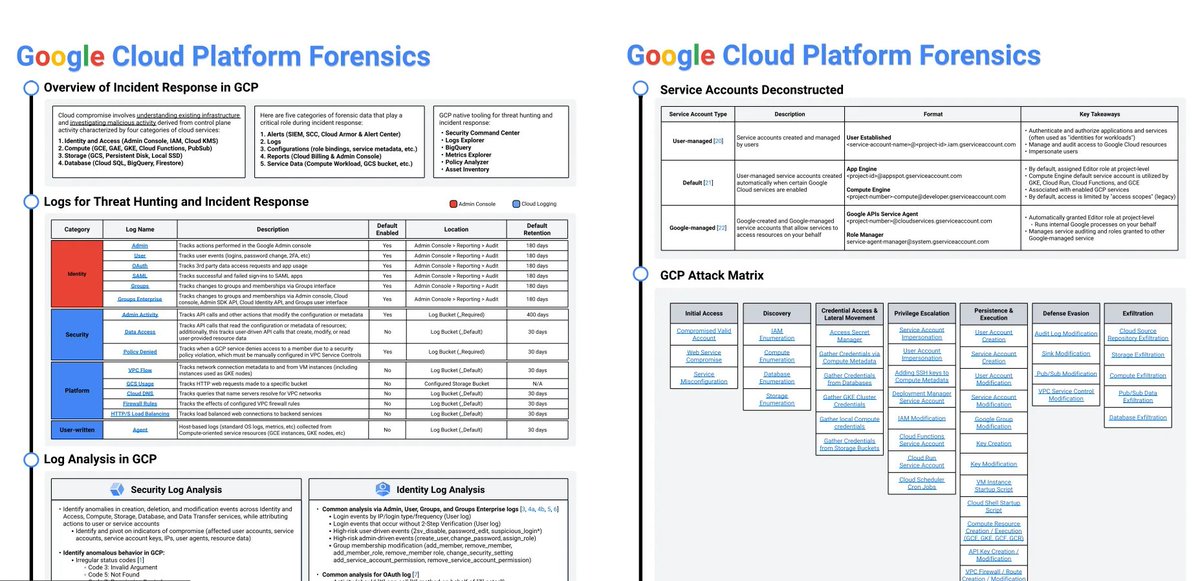
🚨 Boost your #cybersecurity skills! 💻 Check out the ultimate #GoogleCloud Incident Response Cheat Sheet by @TheIceRoot!
☁️ Get the lowdown on:
➡️ IR in GCP
➡️ Threat hunting logs
➡️ Log analysis
➡️ Service accounts
➡️ GCP attack matrix
Read now and level up your incident response game! medium.com/google-cloud/g…
#cloudsecurity #gcp #infosec

English

@anton_chuvakin Hot take, we need to train our users before we train the AI
English

Some org: "We want to use AI to solve this hard security problem X" Also, SAME org: "What's event correlation? How do we enable it in our SIEM?" #facepalm #overheard
English
Noah McDonald me-retweet

I was recently pointed to some #fresh GCP documentation from @TheIceRoot
For your reading pleasure is a complete list of P4SAs (per-project-per-product) Service Accounts and their default roles 📯
cloud.google.com/iam/docs/servi…
English

Google Cloud Incident Response Cheat Sheet by Noah McDonald link.medium.com/kv2T2wgPxGb
English

Google Cloud Incident Response Cheat Sheet by Noah McDonald link.medium.com/8DzDbkiyAGb
English
Noah McDonald me-retweet

#Google #GCP attack matrix
#TrustEverybodyButCutTheCards
Courtesy of: Noah McDonald medium.com/google-cloud/g…
English
Noah McDonald me-retweet

☁️ Google Cloud Incident Response Cheat Sheet
* Overview of IR in GCP
* Logs for threat hunting and incident response
* Log analysis
* Service accounts
* GCP attack matrix
By @TheIceRoot
#cybersecurity #infosec
medium.com/google-cloud/g…
English
Noah McDonald me-retweet
We've lined up a venue for fwd:cloudsec 2024! Mark your calendars for June 17-18 in Arlington, VA. Ticket sales and CFP will open in early January. For those interested in sponsoring, we'll have a prospectus in the next few weeks. Email sponsorship@fwdcloudsec.org if interested.
English
Noah McDonald me-retweet

Ever wonder how attackers breach the cloud? Jay Chen and Noah McDonald will walk through common cloud attack vectors and a real breach incident in this #sectorca presentation, starting at 2:45 in 714AB. buff.ly/3tuDMxt


English
Noah McDonald me-retweet

85% of organizations have hard-coded credentials in VMs, say Jay Chen and Noah MacDonald. Their talk on cloud oversight is ongoing at #sectorca in 714AB. buff.ly/3tuDMxt


English
Noah McDonald me-retweet

We just heard all about how upset gamers compromised the cloud with SIM-Swap, thanks to Jay Chen and Noah McDonald at #sectorca. They're wrapping up now in 714AB. buff.ly/3tuDMxt


English

@NightmareJS Agreed, but people can easily do a better job of locking down their service accounts. It’s up to us to educate them :)
English

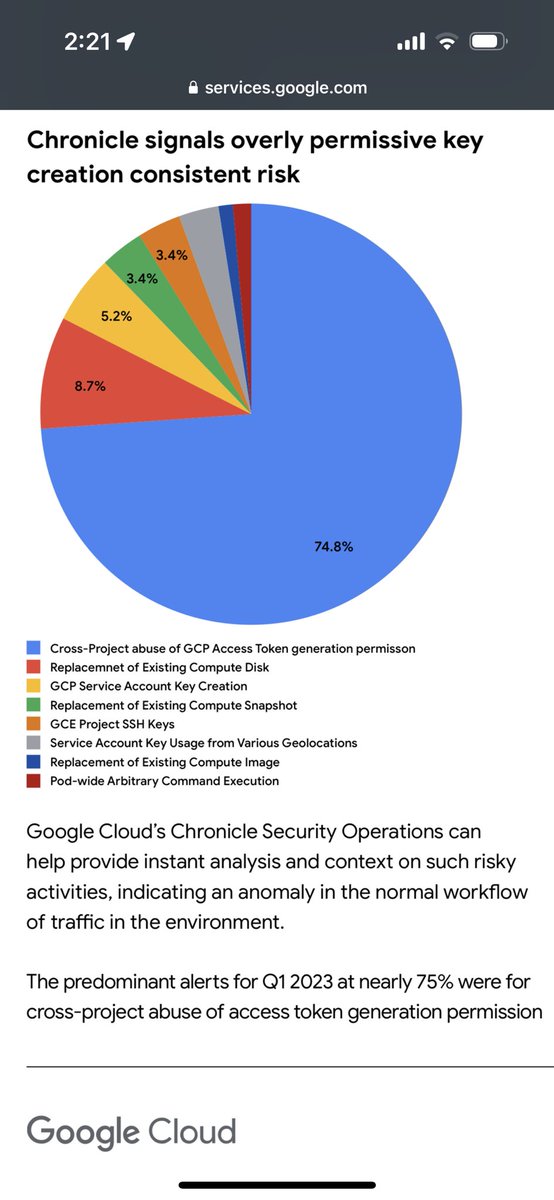
@TheIceRoot This one is so hard because cross-project SA assumption is also a feature of good architecture 🖤
English

Google’s Threat Horizon report, out now! services.google.com/fh/files/blogs…
English

I am excited to announce that my colleague Jay Chen and I got accepted to @BlackHatEvents SecTor!! #when-the-external-threats-and-internal-risks-meet-a-story-of-cloud-breach-34088" target="_blank" rel="nofollow noopener">blackhat.com/sector/2023/br…
English
Noah McDonald me-retweet

Unfortunately @orcasec got their terminology wrong in their report by calling the cloud build SA , a ‘Default SA’, then I PERPETUATED it! - apologies. There are only 2 default SAs. The compute and app engine SA. The Cloud Build SA is not a default SA, it is a P4 SA. 1/3
kat traxler@NightmareJS
The "bad.build" in question is the Default Cloud Build Service Account (SA), so what is it? It runs build for you, pulls images, injects secrets and "actsas" the SA which any resulting resource (i.e. Cloud Run) ultimately runs as. They are unique per project. 2/8
English

@cloudvillage_dc @defcon How long until the submitters should hear back? I haven’t received an approval or denial email yet
English
Just wrapped up the exhilarating task of reviewing all the impressive entries for @defcon this year 🎉📚 Massive kudos to all of you who submitted their work. We will be reaching out to the speakers soon ☎️
Stay tuned for an epic lineup coming your way! 👀
#cloudsecurity #dc31
GIF
English

Spotify released how they analyze volatile memory in Google Kubernetes Engine. Love the details! #secops #containers #forensics engineering.atspotify.com/2023/06/analyz…
English