Wolpertwo 📯
4.6K posts


Wolpertwo 📯
@Wolpertwo
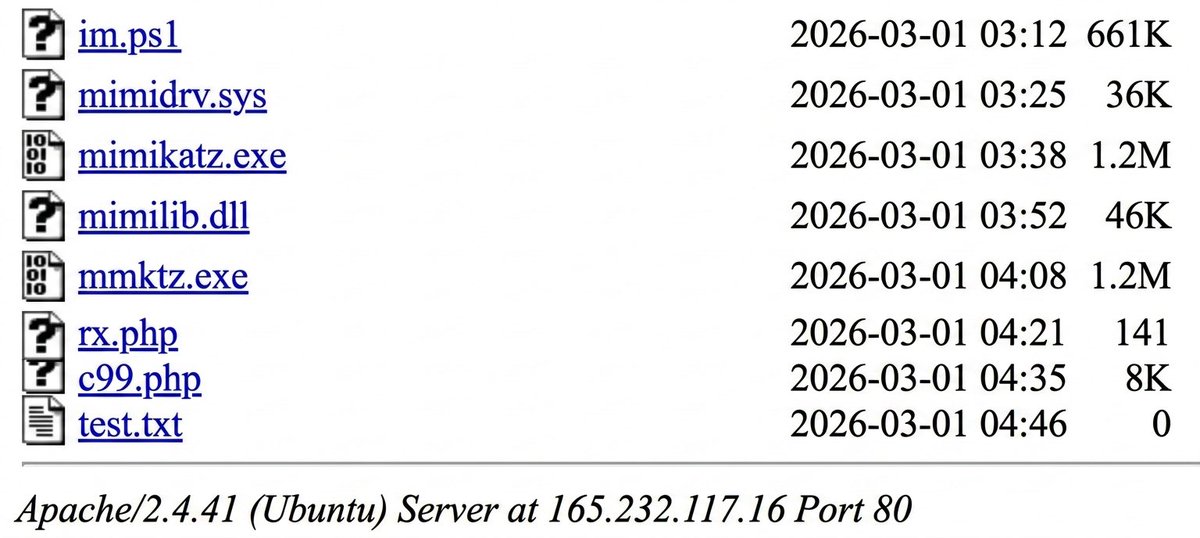
„Westoid Cyberhawk“ Remember to talk to your CISO about activating EventID 4688 with commandline logging via GPO. Забирайся звідси, Сталкер









Why hasn't this caught on in the US? They've been eating self-heating food in Japan (Bento) for several years now. They are popular in train stations and convenience stores and run between $3-$13 USD. You pull a string on the side of the box. This mixes water with a chemical (usually calcium oxide/quicklime) in a bottom compartment, triggering an exothermic reaction that produces steam and heats the meal in 5–10 minutes. Popular varieties include beef tongue, curry rice, beef bowl, steak and seafood options. Who needs a microwave when you have Bento! Source: lumadeline (IG)






Custom-built "Cyberpack" backpack designed for portable computing and Wi-Fi network analysis. Created to study, command, and control Wi-Fi networks. Using Windows 11 PC or Raspberry Pi integrated into the backpack, along with a custom controller interface.







French anthem “La Marseillaise” sung , next to the 'Le Temeraire' SLBM at the nuclear submarines 🇨🇵 Navy base Ile Longue in Crozon, following President Emmanuel Macron’s major speech on French nuclear deterrence and European security.