Tweet Disematkan

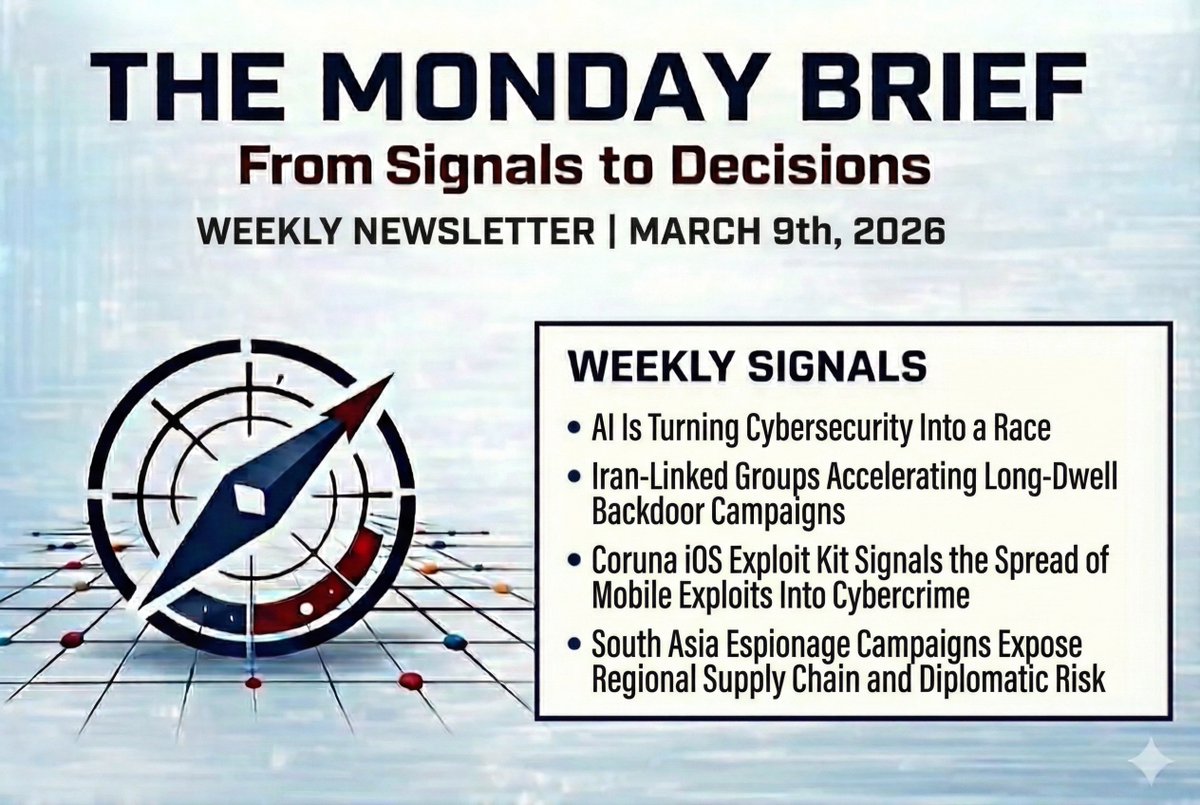
New issue of @TheMondayBrief is live.
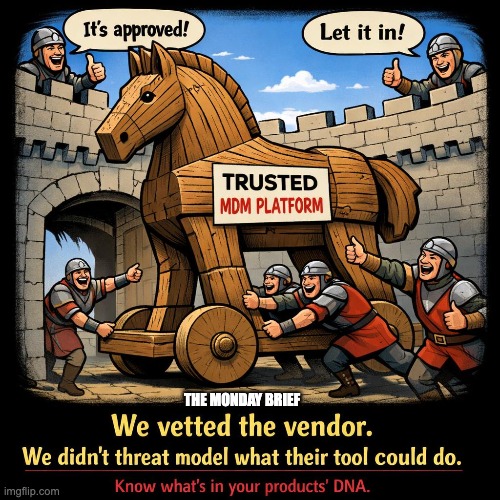
Three Threat Actors, One Blindspot 👇
🔴 44.5% of initial access now comes from third-party software vulns, not credentials - via @GoogleCloudSec
🔴 Handala wiped 200K devices using Intune. One session. No custom malware - via @briankrebs
🔴 Russia is mirroring your Signal chats. They didn't break the encryption. They linked a device - via @AIVD
The common thread: too much implicit trust in infrastructure defenders stopped questioning.
Full breakdown + role-based takeaways, from @fulmetalpackets and I: themondaybrief.substack.com/p/three-threat…
#TheMondayBrief #CyberSecurity #ThreatIntelligence #ZeroTrust #Ransomware #CISO #SecurityOperations #InfoSec #CyberThreats #ThinkRedActBlue
English