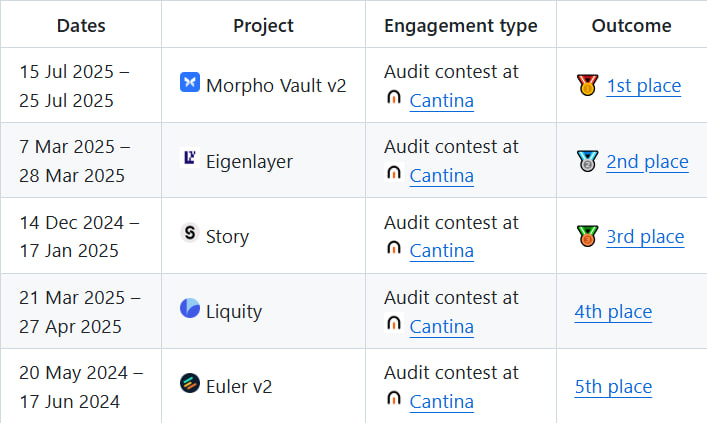
The $40,000 SukukFi Audit Competition results are officially in! 🏆 Huge congrats to everyone who submitted valid findings! And a special shoutout to @Audittens for for earning a spot on the Top 10 leaderboard for the last 90 days Shoutout to @sukukfi for their commitment to security, full list of winners in thread!👇