固定されたツイート
CryingHacker
20 posts


CryingHacker
@CryingHacker
WannaCry over your Bug bounty/cyber security career? Join me while i cry too!😶Trying to share as much information as i can to help people with bug bounty
💀󠄬󠅑󠄐󠅘󠅢󠅕󠅖󠄭󠄒󠄸󠄵󠅂󠄵󠄒 参加日 Haziran 2025
31 フォロー中1 フォロワー
CryingHacker がリツイート

recox.hackerz.space is outperforming most recon
tools 🔥🚀:
🔴waybackurls → 10,184
✅recox → 53,030 🔥
🔴subfinder → 896
🔴subd...c99nl → 896
✅recox → 901 ⚡
check it out : recox.hackerz.space
#bugbounty #bugbountytips

English
CryingHacker がリツイート

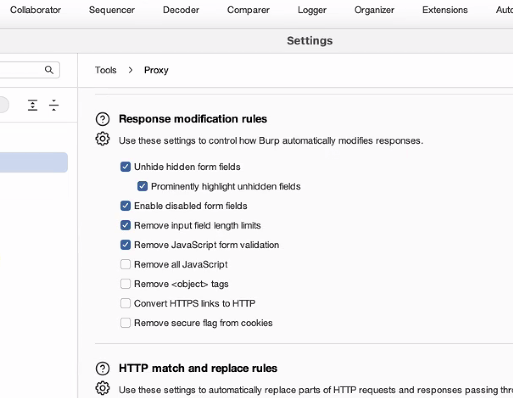
ALWAYS add this to your burp settings before testing
these are just "front end protection against user stupidity" - @theXSSrat
English

CryingHacker がリツイート

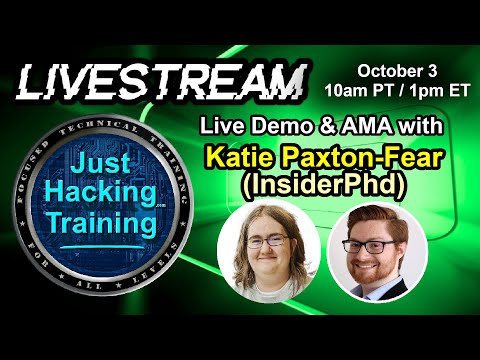
Just watched @_JohnHammond x @InsiderPhD whole live stream there is always so much information with these too!
really good live stream learned so much maybe ill do some key points i noted from that live in the future
youtube.com/watch?v=rE3gN9…
YouTube
English

API Basics: A Hacker's Starter Guide by
@medusa_0xf really cool explanation! + she has extra sources inside
medusa0xf.com/posts/api-basi…
English

@NahamSec @Hacker0x01 Crazy how such a simple xss can get you so much congrats 😲
(and your shirt is diabolical)
English

I found really interesting XSS at a @hacker0x01 LHE that required a few bypasses. Do you think it was worth $15,000? youtu.be/oJM8GxyWs20

YouTube

English

Today I learned:
about cookie sandwich
portswigger.net/research/steal…
TL;DR The cookie sandwich is a trick that lets attackers leak HttpOnly cookies by abusing how some servers parse cookies.
English

Some Recon tools hackers ACTUALLY USE:
subdomains ON THE WEB🌐:
subdomainfinder.c99.nl
securitytrails.com
dnsdumpster.com - visualizes mind map
viewdns.info
chaos.projectdiscovery.io
censys.io
hackertarget.com
shodan.io
English
CryingHacker がリツイート

@Burp_Suite 3. Send OAuth token to controlled server
4. Send to bug bounty program
5. Gets marked as duplicate
6. Cycle repeats.
English
CryingHacker がリツイート

I spent three days breaking this PDF renderer on the same target just to be sent the following user agent:
Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) HeadlessChrome/145.0.0.0 Safari/537.36 - /
Ben Sadeghipour@NahamSec
I'm one XSS filter bypass away from being able to entirely own this AI chatbot 🫠 but I actually can't bypass this pos.
English