PeckShield Inc.
1.6K posts


@peckshield
A blockchain security and data analytics company (telegram: https://t.co/x72dANZur3)




It seems the 0x1f4c_Kelp DAO Exploiter on ethereum is being liquidated (w/ ~$123m debt) in @aave Here is the related tx: etherscan.io/tx/0xe2391ea41… The arbitrum position is also liquidated: arbiscan.io/tx/0x78b41623c…

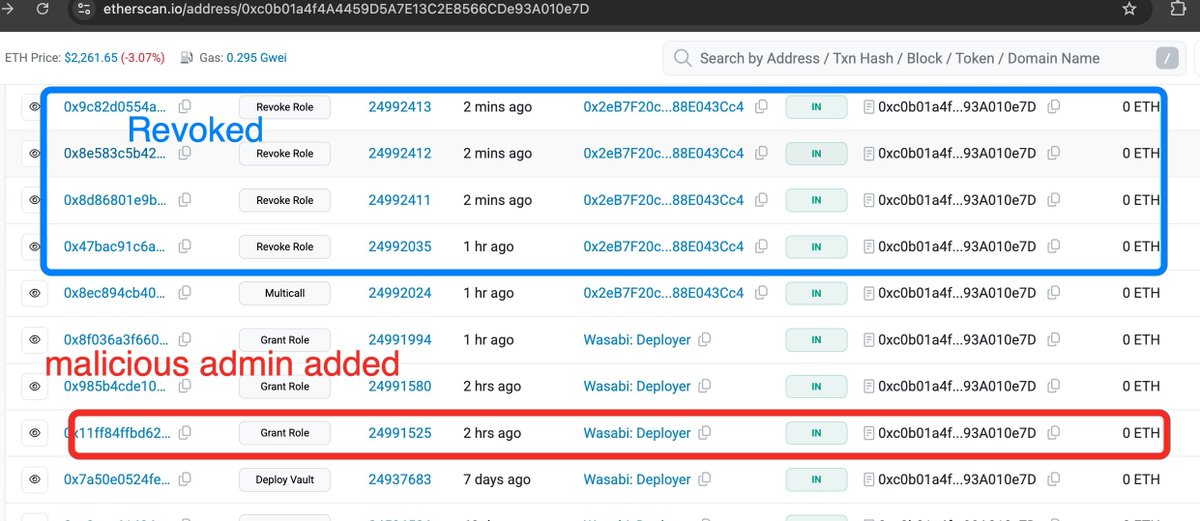
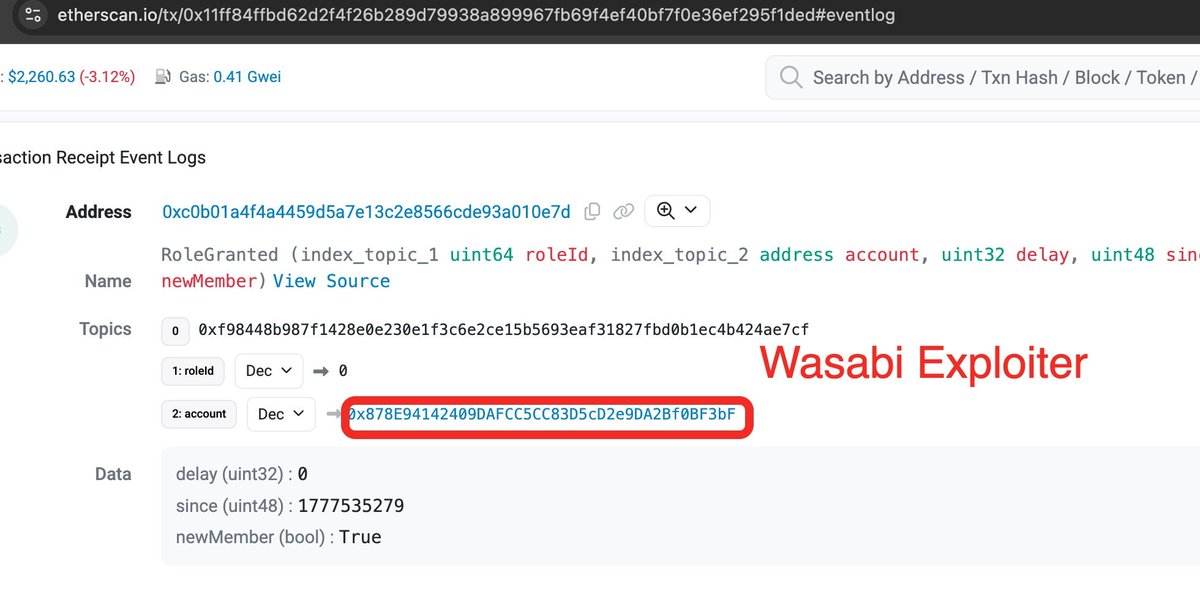
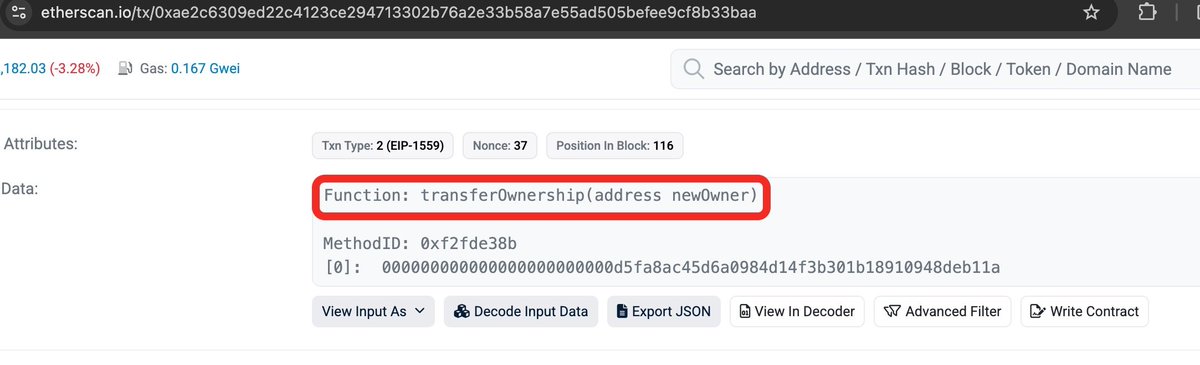
We're aware of an issue and are actively investigating. As a precaution, please do not interact with Wasabi contracts until further notice. We'll share an update as soon as we have more information. Thanks for your patience.

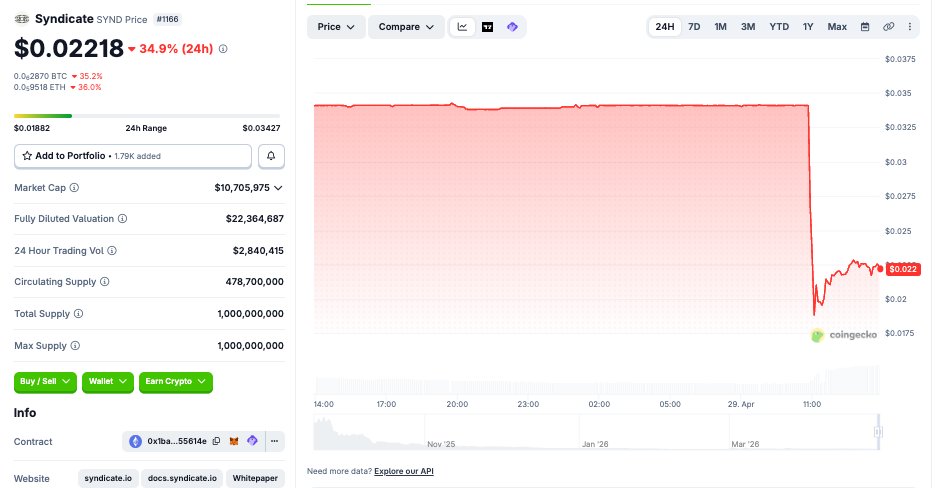
IMPORTANT: We are investigating a compromise of the Commons bridge. We are tracing the attack and engaging with security firms. We are also looking at options to make people whole. Syndicate has sufficient tokens available to help users who have lost SYND.


idk why peckshield is being so reckless in their messaging here, but to be clear, this is the yearn v2 WETH vault, and it is not connected to Alchemix in any way whatsoever. Since the v2 -> v3 migration was completed almost two weeks ago, we have not had any funds deployed to it.

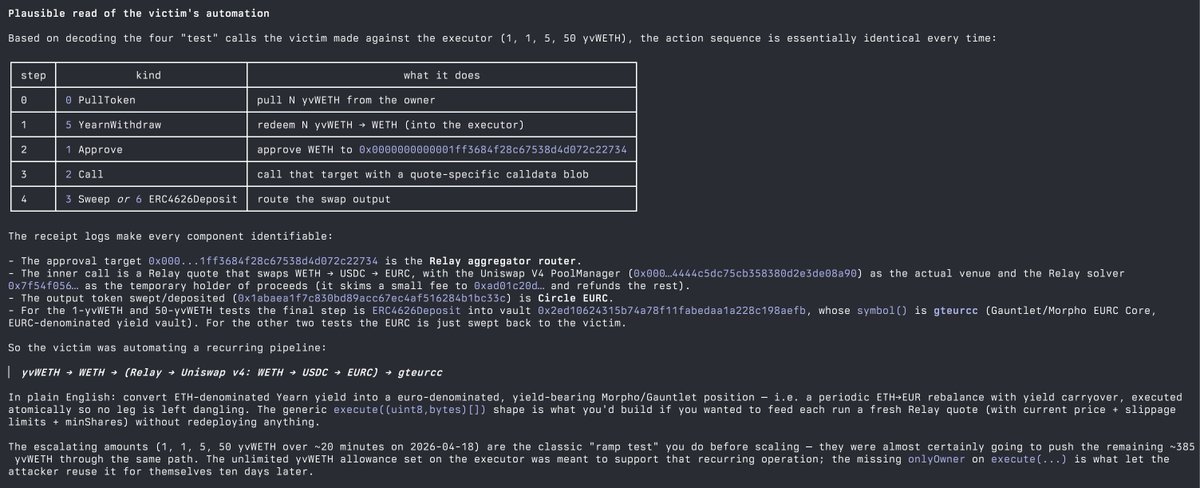
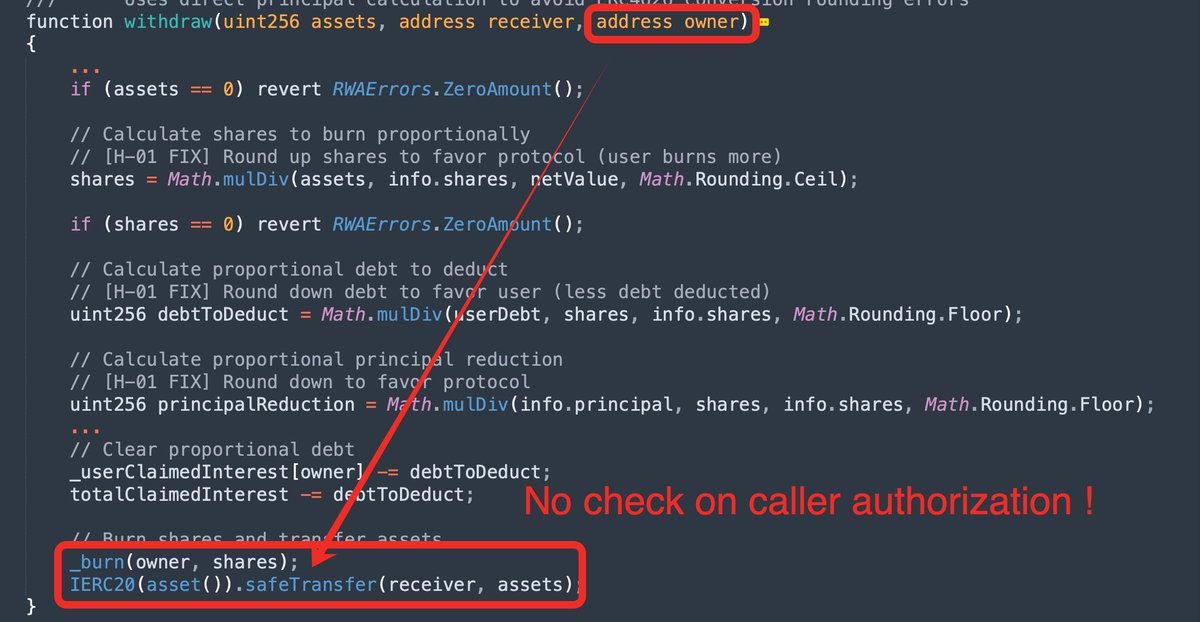
A victim just lost a Alchemix Yearn yvVault position $yvWETH (estimated $~1m), from an earlier approval to an unverified contract (etherscan.io/address/0x143a…). This unverified contract, created 10 days ago, turns out to be buggy and can be exploited for arbitrary call execution. Here is the vulnerable logic from the decompiled contract, affected in the following exploit tx: etherscan.io/tx/0xebaaab69b…






#PeckShieldAlert The @KelpDAO exploiter bridged $ETH from #Ethereum to #Arbitrum via @AcrossProtocol, swapped for $USDT0, and subsequently routed funds to @trondao via @LayerZero_Core

The latest fund movement from the @KelpDAO exploiter: arbiscan.io/tx/0x561804424…





Hi @KelpDAO , you may want to take a look at: etherscan.io/tx/0x1ae232da2…