jd
320 posts


jd
@c0kernel
Interested in books, mathematics, running, rock climbing, and infosec.
Minnesota 参加日 Aralık 2010
363 フォロー中138 フォロワー
jd がリツイート

My SCCM BloodHound OpenGraph collector, ConfigManBearPig, is finally ready to share! It can enumerate all of the relay TAKEOVERs and a few CRED and ELEVATE techniques from Misconfiguration Manager with just a domain account. Let me know what you find! specterops.io/blog/2026/01/1…
English

Patch em
Florian Roth ⚡️@cyb3rops
Critical Security Vulnerability in React Server Components CVE-2025-55182 and rated CVSS 10.0 The vulnerability is present in versions 19.0, 19.1.0, 19.1.1, and 19.2.0 of: react-server-dom-webpack react-server-dom-parcel react-server-dom-turbopack react.dev/blog/2025/12/0…
English
jd がリツイート

Stack spoofing isn’t dead.
Hear from @klezvirus at #BHEU on how modern detection still breaks, and unveils the first CET-compliant stack spoofing framework.
Learn more ➡️ ghst.ly/4izmuou

English
jd がリツイート
jd がリツイート

SCOM monitors critical systems, but insecure defaults make it a powerful attack vector.
At #BHEU, @unsigned_sh0rt & @breakfix show how to abuse SCOM for credential theft, lateral movement, and domain escalation, plus how to defend it. ghst.ly/4aoggph

English
jd がリツイート

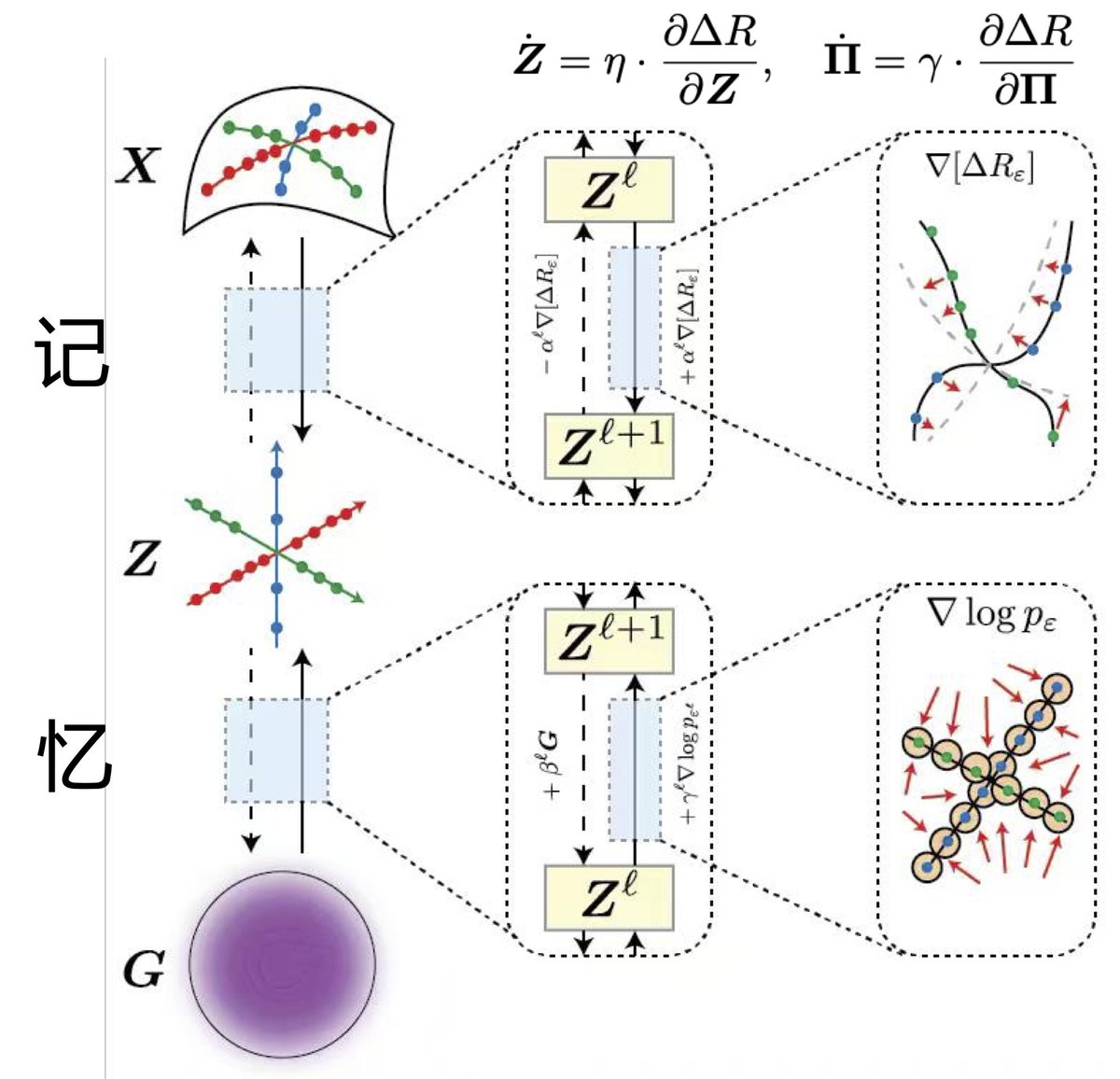
All done with my new course on Deep Representation Learning this semester. All lecture slides and video recordings are now available at the book website: ma-lab-berkeley.github.io/deep-represent… We believe, with the book, they help students clarify basic concepts and principles of Intelligence.
English
jd がリツイート
jd がリツイート

How do you model hybrid attack paths that span GitHub, GCP, Azure, and AD?
@c0kernel has released SecretHound, a new BloodHound OpenGraph extension for secrets 🤫 — enabling modeling of “credential watering holes” across tech platforms. ghst.ly/4oZin6Y
English

Released my first blog post today:
specterops.io/blog/2025/11/1…
And released SecretHound, a BloodHound OpenGraph extension for secrets:
github.com/C0KERNEL/Secre…
English
jd がリツイート
jd がリツイート

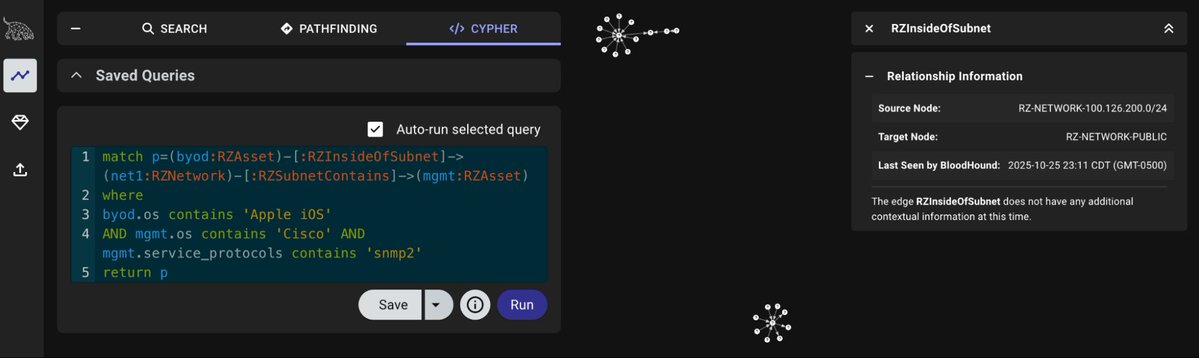
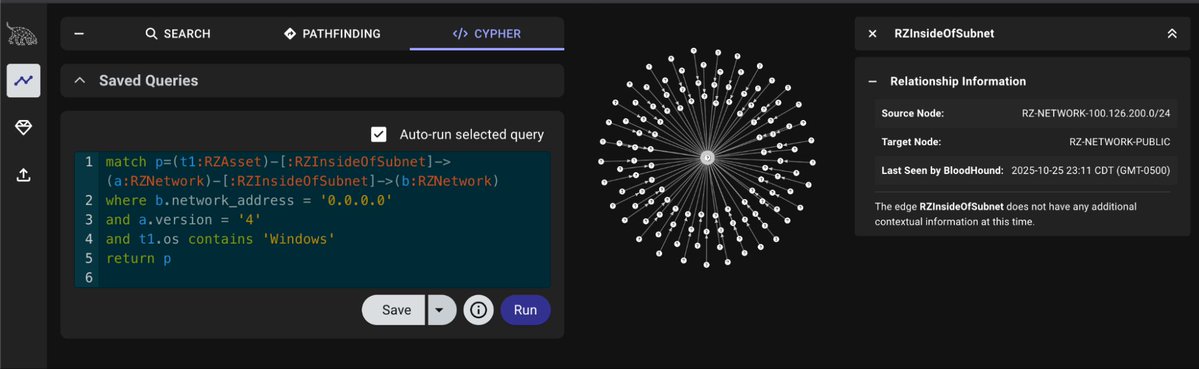
Just like chocolate and peanut butter, runZero and BloodHound are an amazing combination. Today we are introducing runZeroHound - an open source toolkit for bringing runZero Asset Inventory data into BloodHound attack graphs: runzero.com/blog/introduci…


English
jd がリツイート

Credential Guard was supposed to end credential dumping. It didn't.
@bytewreck just dropped a new blog post detailing techniques for extracting credentials on fully patched Windows 11 & Server 2025 with modern protections enabled.
Read for more ⤵️ ghst.ly/4qtl2rm
English
jd がリツイート
jd がリツイート

As an attacker, I care more about the presence of canaries in an environment than about triggering them. Their existence lets me know they're either being automatically deployed (Cortex, etc.) or have someone who cares enough to build the environment this way and proceed accordingly.
There is obviously a class of canaries where they're backed by server side monitoring, i.e., pulling a file from a file share and having the file server report the event, making it harder for an attacker to identify and avoid. However, the ones built into documents can almost always be avoided. I always suggest deploying a mix of self reporting canary files and server/EDR-backed ones, rather than just one type.
English
jd がリツイート

BloodHound OpenGraph allows you to map attack paths across ANY platform.
@jaredcatkinson spoke with @DarkReading during #BHUSA about how you can now connect the dots between Active Directory, GitHub repositories, and other sensitive assets.
👀: ghst.ly/4fAfwxQ
English
jd がリツイート

It's easy to see "red" and "blue" as being against each other, that blue is constantly trying to keep up with red.
The reality is that red and blue are on the SAME SIDE.
Together, we're trying to keep up with emergent risks created by legacy tech, new tech, and common configs:


Ciudad Autónoma de Buenos Aires, Argentina 🇦🇷 English
jd がリツイート