

Carl Smith
316 posts


@cffsmith
Security @Google; @FluxFingers/@Sauercl0ud; previously V8 Security, Intern {Project Zero, @XI_Research}. Personal account. https://t.co/w9zosKSHdh on Bluesky.






More HW security goodness from Arm: community.arm.com/arm-community-… vMTE (Virtual Memory Tagging) allows to use MTE in a more flexible way, consuming less RAM. POE2 allows to build efficient in-process sandboxes and isolation. More-or-less improvement over x86 Memory Protection Keys.

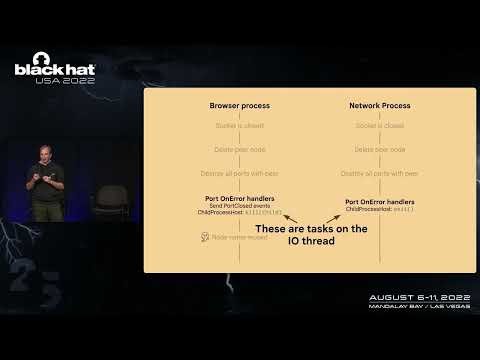
Whoah... $250000 (CVE-2025-4609, similar to CVE-2025-2783/412578726)[412578726][Mojo][IpczDriver]ipcz bug -> renderer duplicate browser process handle -> escape sbx is now open with PoC & exploit(success rate is nearly 70%-80%) issues.chromium.org/issues/4125787… #comment11" target="_blank" rel="nofollow noopener">issues.chromium.org/issues/4125787…


Part 5 of @j00ru's Windows Registry Adventure is out! googleprojectzero.blogspot.com/2024/12/the-wi… Incredible depth of knowledge on display, and good to see it shared as a reference with the world ❤️



The latest Apple security update contains fixes for three CoreAudio issues (CVE-2025-24160, CVE-2025-24161, CVE-2025-24163). These were found by Google Threat Analysis Group using Jackalope fuzzer.




What kind of email is she sending?
