固定されたツイート

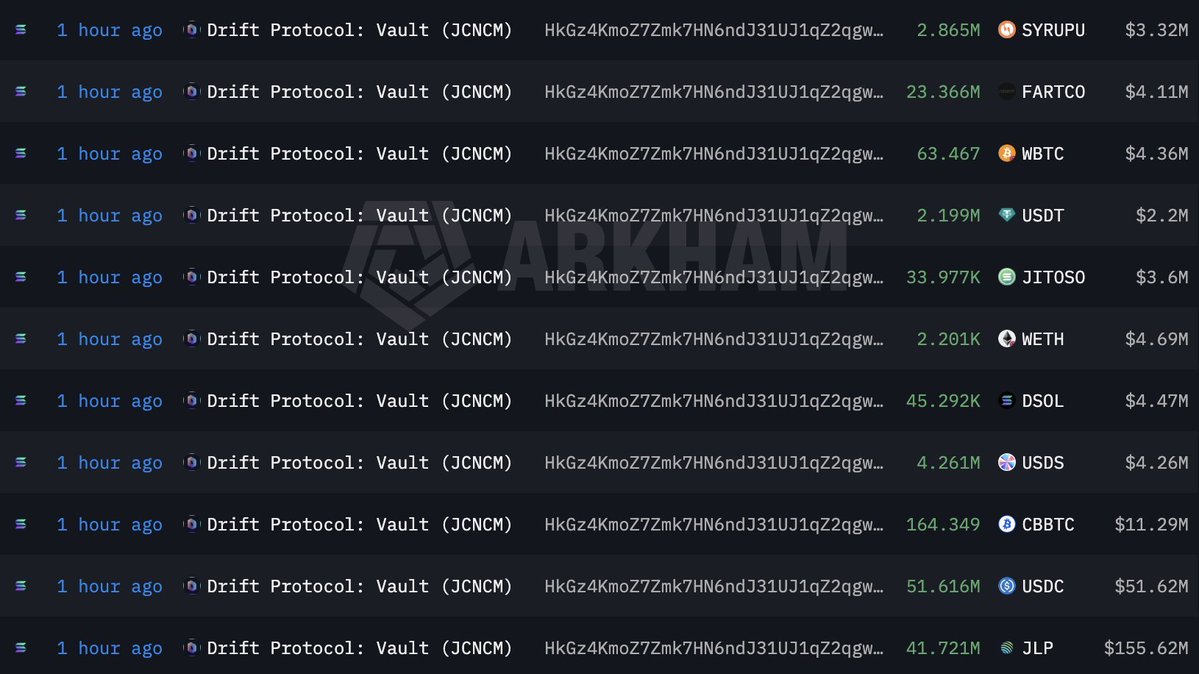
Biggest payout yet from a contest.
More wins coming this year for sure.
Thanks @immunefi
Thank you web3
#Web3Security #immunefitribe

English
RazkkyDev
347 posts

@dev_razkky
Web3 security researcher || @CyfrinUpdraft alumni
















A Nigerian fintech startup lost ₦47 million in one night. Not to hackers. Not to fraud. To one missing line of code. Every backend dev in Nigeria needs to see this
Whitehat @00xSEV recently scored a $50,000 payout for a High smart contract vulnerability. Well done! You can pledge IMU to this security researcher here and earn IMU when they find more vulnerabilities: immunefi.com/pledge/xSEV/
