Arn
14 posts


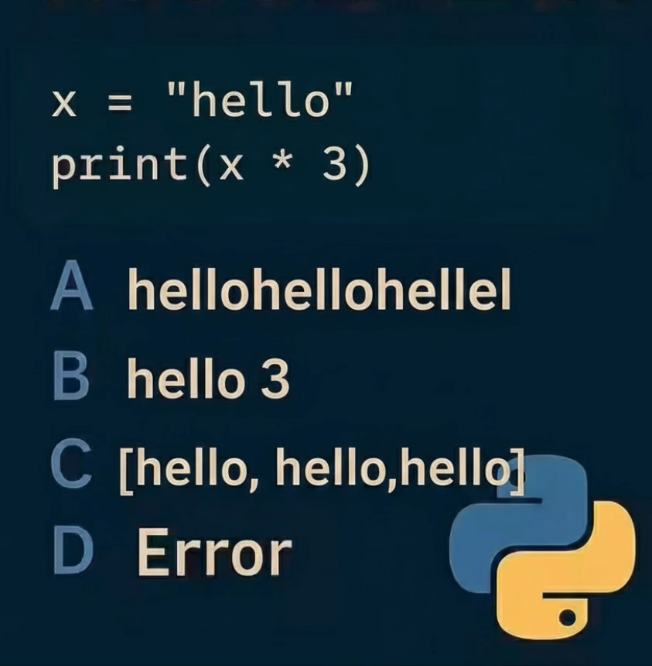
Complete DSA in 100 days
If you're looking to become Master in DSA This handwritten note will make learning DSA easier.
The handwritten notes include a comprehensive overview of DSA .
You will get:
→ Day to day learning
→ Interview questions
→ Save 300hrs + on Research
→ Complete Roadmap
𝐍𝐨𝐫𝐦𝐚𝐥𝐥𝐲 𝐈𝐭'𝐬 $30 𝐛𝐮𝐭 𝐟𝐨𝐫 𝟐𝟒 𝐡𝐨𝐮𝐫𝐬, 𝐢𝐭'𝐬 𝟏𝟎𝟎% 𝐅𝐑𝐄𝐄!
To get it, just:
1. Like & Reply “DSA“
2. Retweet (much appreciated)
3. Follow me (so that I can DM)
English
Arn がリツイート

🚨BREAKING: ANTHROPIC CEO JUST ENDED OPENAI
@sama
After getting blacklisted by Pentagon, Dario sits down and writes the most unhinged CEO memo in silicon valley history:
>calls openai's pentagon deal "safety theater"
>says trump admin hates them because they haven't "given dictator-style praise to Trump (while Sam has)"
>names greg brockman's $25M trump super PAC donation by name says they supported AI regulation
>"which is against their agenda"
>says they "told the truth about AI policy issues like job displacement"
THE PALANTIR EXPOSÉ:
>reveals palantir's actual pitch to anthropic during negotiations
>"you have some unhappy employees, you need to offer them something that placates them or makes what is happening invisible to them, and that's the service we provide"
>palantir's pitch wasn't safety. it was CONCEALMENT
>palantir offered a "classifier" to detect red line violations
>dario: models get jailbroken, monitoring only works in a few cases "maybe 20% real and 80% safety theater"
>says palantir offered openai the same package
>openai accepted it
>says Altman is "peddling narratives" to his own employees
>calls openai employees "sort of a gullible bunch" due to "selection effects"
>says the "attempted spin/gaslighting" isn't working on
>the public or media but IS working on "some Twitter morons" rofl
>says his main concern is making sure it doesn't work on openai employees too
BTW near the end of negotiations the pentagon offered to accept ALL of anthropic's terms if they deleted ONE phrase:
>"analysis of bulk acquired data"
>anthropic refused
>same surveillance clause pentagon said they didn't even want to do
>meanwhile Altman told his employees: "you don't get to weigh in on that" 💀
ITS OVER.
ANTHROPIC WON, DEAL WITH IT

English

I analyze thousands of bug bounty content items every month. Less than 5% makes it to the newsletter.
I distilled those curated selections down to the top 25 resources for 2026 and put them in this PDF. It includes the top platforms, tools, and people that consistently deliver high signal content.
Comment RESOURCES and I'll DM you the PDF for free. (Make sure your DMs are open)
#BugBounty

English
Arn がリツイート

4.4 stars .... FOR FREE --- FOR YOU!!!!
udemy.com/course/pentest…
Grab it now - only 1000 spots
English
Arn がリツイート

GIVEAWAY TIMEEEE - 3000x @Burp_Suite course FREEEEE
udemy.com/course/burp-su…
udemy.com/course/burp-su…
udemy.com/course/burp-su…
It is the season of giving so please share this so others can take advantage <3 if none of the codes say FREE anymore they are all taken
English
Arn がリツイート

100 Exploits every bounty hunter should know!
thexssrat.podia.com/christmas2024?…
BAC: Function-Level Authorization Bypass
BAC: Object-Level Authorization (IDOR)
BAC: Horizontal Privilege Escalation
BAC: Vertical Privilege Escalation
BAC: Missing Authorization on API Endpoint
BAC: Forced Browsing to Restricted Pages
BAC: Multi-Tenant Data Isolation Failure
BAC: Role Manipulation via Parameter Tampering
BAC: Authorization Based on Client-Side Logic
BAC: Insecure Direct Object Reference via UUID Guessing
AUTH: Account Enumeration via Error Messages
AUTH: Brute-Force Login Attack
AUTH: Credential Stuffing
AUTH: Weak Password Policy
AUTH: Missing Rate Limiting on Login
AUTH: Password Reset Token Leakage
AUTH: Password Reset Token Reuse
AUTH: Authentication Bypass via Logic Flaw
AUTH: Missing Multi-Factor Authentication
AUTH: OAuth Login Misbinding
SESSION: Session Fixation
SESSION: Session Hijacking
SESSION: Missing Session Expiration
SESSION: Predictable Session IDs
SESSION: Concurrent Session Abuse
SESSION: Logout Function Not Invalidating Session
SESSION: Session Token in URL
SESSION: Cross-Device Session Reuse
SESSION: Missing Session Rotation After Login
SESSION: Privilege Change Without Session Refresh
COOKIE: Missing HttpOnly Flag
COOKIE: Missing Secure Flag
COOKIE: Missing SameSite Attribute
COOKIE: Client-Side Cookie Trust
COOKIE: Cookie Scope Too Broad
INJECTION: SQL Injection
INJECTION: Blind SQL Injection
INJECTION: NoSQL Injection
INJECTION: Command Injection
INJECTION: OS Command Injection via File Upload
INJECTION: LDAP Injection
INJECTION: XPath Injection
INJECTION: Expression Language Injection
INJECTION: Server-Side Template Injection (SSTI)
INJECTION: CRLF Injection
XSS: Reflected Cross-Site Scripting
XSS: Stored Cross-Site Scripting
XSS: DOM-Based Cross-Site Scripting
XSS: Blind Cross-Site Scripting
XSS: HTML Injection Leading to XSS
CSRF: Missing CSRF Protection
CSRF: CSRF Token Reuse
CSRF: CSRF Token Not Bound to Session
CSRF: GET Request Performing State Change
CSRF: JSON CSRF via CORS Misconfig
CORS: Wildcard Origin with Credentials
CORS: Reflected Origin Trust
CORS: Null Origin Allowed
CORS: Overly Permissive Methods
CORS: Sensitive Headers Exposed
FILE: Unrestricted File Upload
FILE: MIME Type Validation Bypass
FILE: Path Traversal in File Upload
FILE: File Overwrite via Upload
FILE: Stored XSS via File Upload
PATH: Directory Traversal
PATH: Arbitrary File Read
PATH: Arbitrary File Write
PATH: Local File Inclusion (LFI)
PATH: Remote File Inclusion (RFI)
DESERIALIZATION: Insecure Deserialization
DESERIALIZATION: PHP Object Injection
DESERIALIZATION: Java Deserialization RCE
DESERIALIZATION: YAML Deserialization Abuse
DESERIALIZATION: JSON Deserialization Logic Flaw
LOGIC: Business Logic Abuse
LOGIC: Price Manipulation
LOGIC: Coupon Reuse Abuse
LOGIC: Race Condition (TOCTOU)
LOGIC: Negative Value Injection
INFO: Sensitive Data Exposure in API Response
INFO: Stack Trace Disclosure
INFO: Debug Mode Enabled in Production
INFO: Source Code Disclosure
INFO: .git Directory Exposure
SSRF: Server-Side Request Forgery
SSRF: Blind SSRF via PDF/Image Fetch
SSRF: Cloud Metadata Access
SSRF: Internal Port Scanning
SSRF: Protocol Smuggling (gopher/file)
RCE: Remote Code Execution via Injection Chain
RCE: Template Injection to Code Execution
RCE: Unsafe Eval Usage
RCE: Command Injection via Environment Variables
RCE: Dependency Confusion Attack
CONFIG: Default Credentials
CONFIG: Hardcoded Secrets in Frontend
CONFIG: Exposed Admin Panel
CONFIG: Insecure Feature Flags
CONFIG: Insecure API Versioning
#BugBounty #WebSecurity #AppSec #ApplicationSecurity #InfoSec #CyberSecurity
#EthicalHacking #Hacking #Pentesting #Pentest #RedTeam #BlueTeam
#BrokenAccessControl #BAC #IDOR #AuthBypass #PrivilegeEscalation
#API #APISecurity #OWASP #OWASPTop10 #OWASPAPI
#XSS #CSRF #SQLi #NoSQLi #SSTI #RCE #SSRF #LFI #RFI #PathTraversal
English
Arn がリツイート

⚠️ Hackers Allegedly Claim Breach of Mercedes-Benz USA Legal and Customer Data
Source: cybersecuritynews.com/mercedes-benz-…
A threat actor known as "zestix" has claimed responsibility for a significant data breach affecting Mercedes-Benz USA (MBUSA), allegedly exfiltrating 18.3 GB of sensitive legal and customer information.
The threat actor posted the dataset for sale on a dark web forum, pricing the complete archive at $5,000. According to the listing, the breach exposes a wide array of internal documents, spanning active and closed litigation files from 48 U.S. states.
At the time of this report, Mercedes-Benz USA has not issued any official statement confirming the authenticity of the data.
#cybersecuritynews

English
Arn がリツイート
🚨 New release alert!
The OWASP Top 10 2025 (Release Candidate) is now live and it’s a must-see for anyone in AppSec, DevOps, or cyber security.
The 2025 list:
A01 – Broken Access Control
A02 – Security Misconfiguration
A03 – Software Supply Chain Failures
A04 – Cryptographic Failures
A05 – Injection
A06 – Insecure Design
A07 – Authentication Failures
A08 – Software or Data Integrity Failures
A09 – Logging & Alerting Failures
A10 – Mishandling of Exceptional Conditions
Why it matters:
• Reflects the evolving threat landscape.
• A powerful checklist for managers, developers and security teams alike.
• If you’re building or securing applications treat this as a roadmap.
Everything you need to know: owasp.org/Top10/2025/0x0…
Keep an eye out we are updating our labs pretty soon! 🚀 👀
English