David Cannings
1.6K posts

David Cannings
@edeca
Cyber defence, reverse engineering and network geekery. Christian, husband & father of three. All views my own.
参加日 Eylül 2009
319 フォロー中837 フォロワー


@saidelike The last time (many years ago) I used VMware and serial from Windbg. I expect things have come on a long way 😃
English

@pitlane_girl @SkySportsF1 I wonder if it was showing incorrect data because there were two formation laps. The first racing lap showed 1/23 which should have been 2/23.
English

This is a neat way of signaturing PDF samples, provided you carefully manage performance.
I wrote a short post explaining how it works and a few suggestions for enhancements: edeca.net/post/2024-06-2…
Félix Aimé@felixaime
import "hash" rule Calisto_PDF_streams { strings: $s1 = { 0A 73 74 72 65 61 6D 0A } $s2 = { 0A 65 6E 64 73 74 72 65 61 6D 0A } condition: uint32be(0) == 0x25504446 and for any i in (0..#s1) : ( hash.md5(@s1[i]+8, @s2[i]-@s1[i]-8) == "b9950253cf88305a57cb350deb31c07e" ) }
English

@felixaime @s1 @s2 A fun technique. I explain how this works in the following blog post, and provide a few suggestions for potential improvements: edeca.net/post/2024-06-2… (thanks also to @wxs)
English

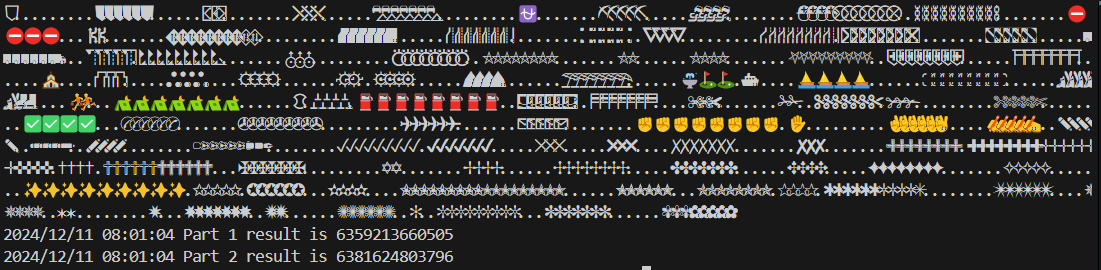
Even without recent publications on them, CALLISTO/#COLDRIVER are continuing their phishing campaigns. If you are looking to track them, beyond infrastructure tracking, you can use YARA rules on the streams of their PDF templates - example below ⬇️



English

@wxs @r0ny_123 @travisgoodspeed You’d need to be careful about the overall file size and test the last 1..3 bytes separately I assume. I didn’t try this.
English

@wxs @r0ny_123 @travisgoodspeed I am using logical OR to ignore the even addresses. I think this is correct based on my limited testing. I haven’t seen test data related to the original question.
English

@hydahy Now now, locals like Frodo and Bilbo from The Shire don’t want Londoners dictating their breakfast routines 🥐
English

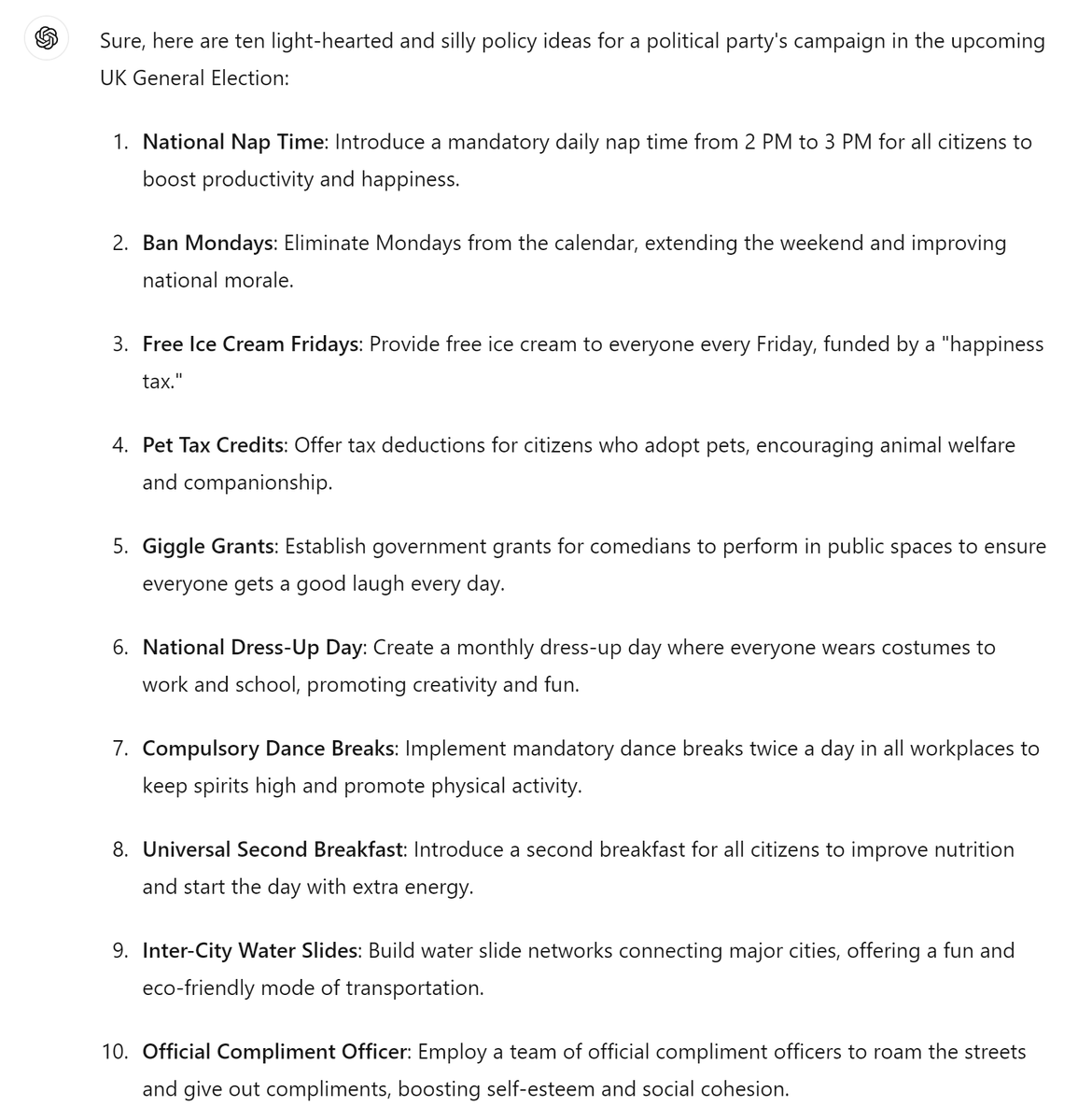
I asked #ChatGPT to generate 10 silly policy examples for the upcoming UK election campaign. I think it aced the question on the first try #generalelectionuk
English

@travisgoodspeed Here's a simple rule that seems to work: gist.github.com/edeca/643483f5…
Any solution will need to scan every byte, so the only potential performance improvement I see would be to scan 32 bit integers and handle the remaining 1..3 bytes separately.
English

@drfootleg @emfcamp Looks great! What are the panels you are using for this?
English

@AzakaSekai_ If it uses a funky multi-stage process with a fifty byte XOR loop then I suspect it is related. Your screenshots from IDA look familiar.
English

@edeca No, this was used to load a variant of Gh0st - though the anti-analysis technique is also quite common.
English

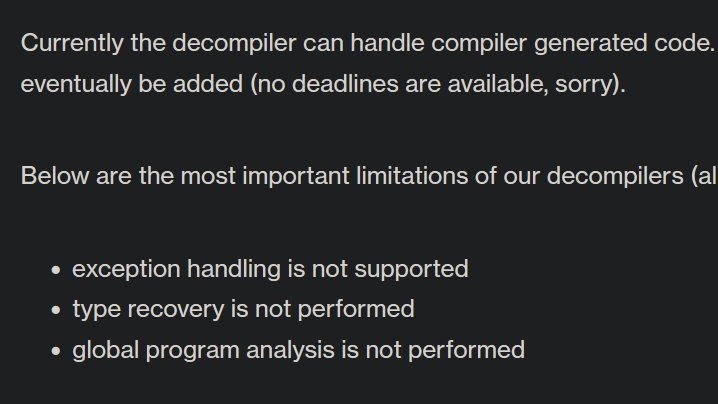
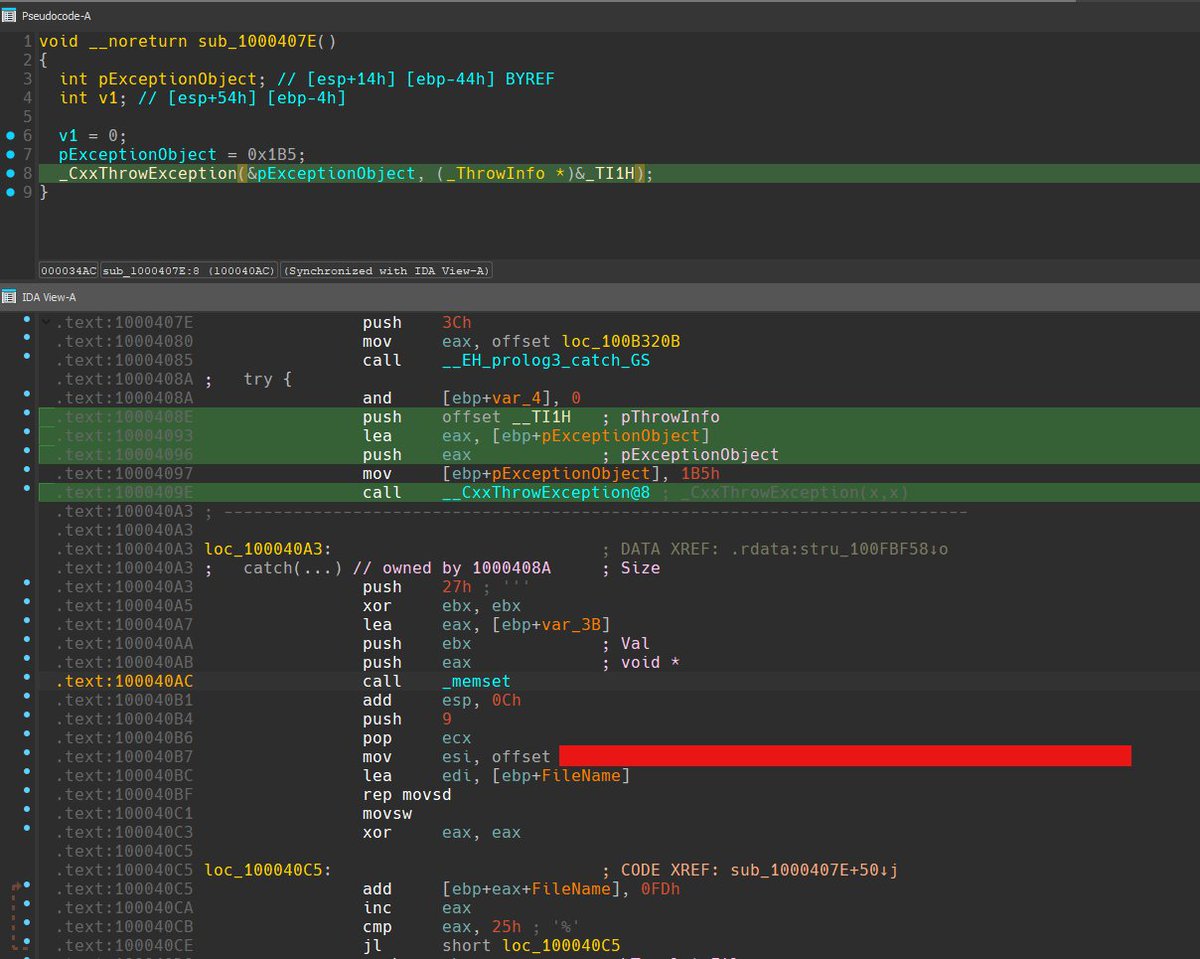
Some basic #IDA101 here: IDA does not support decompiling exception handlers; in other words, code that are within a catch block will not show up in the pseudocode view. A reminder that you should not blindly trust the pseudocode view.
This is a very common anti-analysis method, where an exception is intentionally thrown, triggering the code within the catch block that will not show up in the decompiled view in IDA.
English

@hmm261120 @ItsKylra @endermanch ASLR is supported on both 32-bit and 64-bit platforms, fastcall is available on x86 (for two registers) and MMX was introduced in 1997 on the Pentium P5.
English

@ItsKylra @endermanch ASLR only work on 64 bit and the ABI is different.
x64 has 16 General Purpose Registers while x86 only 8.
x86 use FPU for float number while x64 use XMM which is faster.
x86 stdcall use stack memory for passing argument, x64 use 4 initial register for passing argument.
English

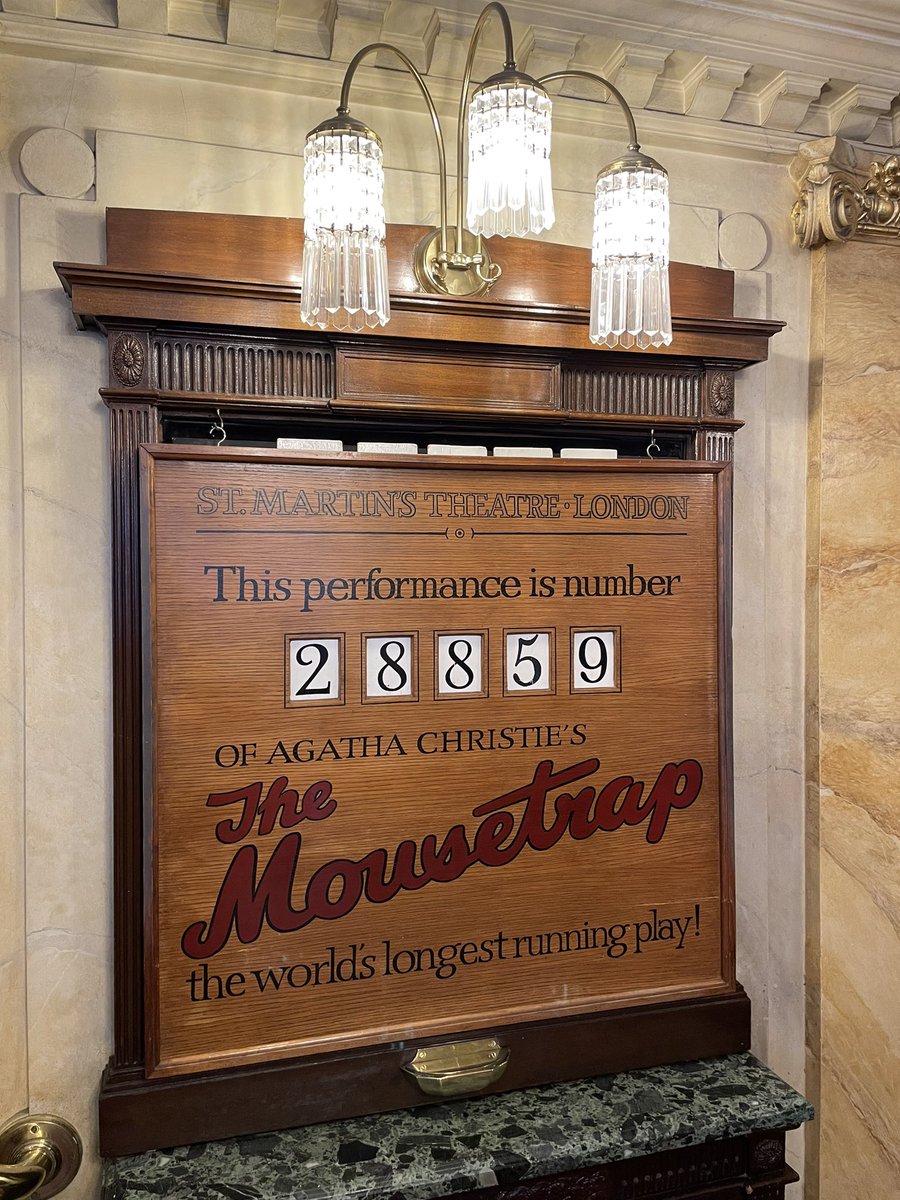
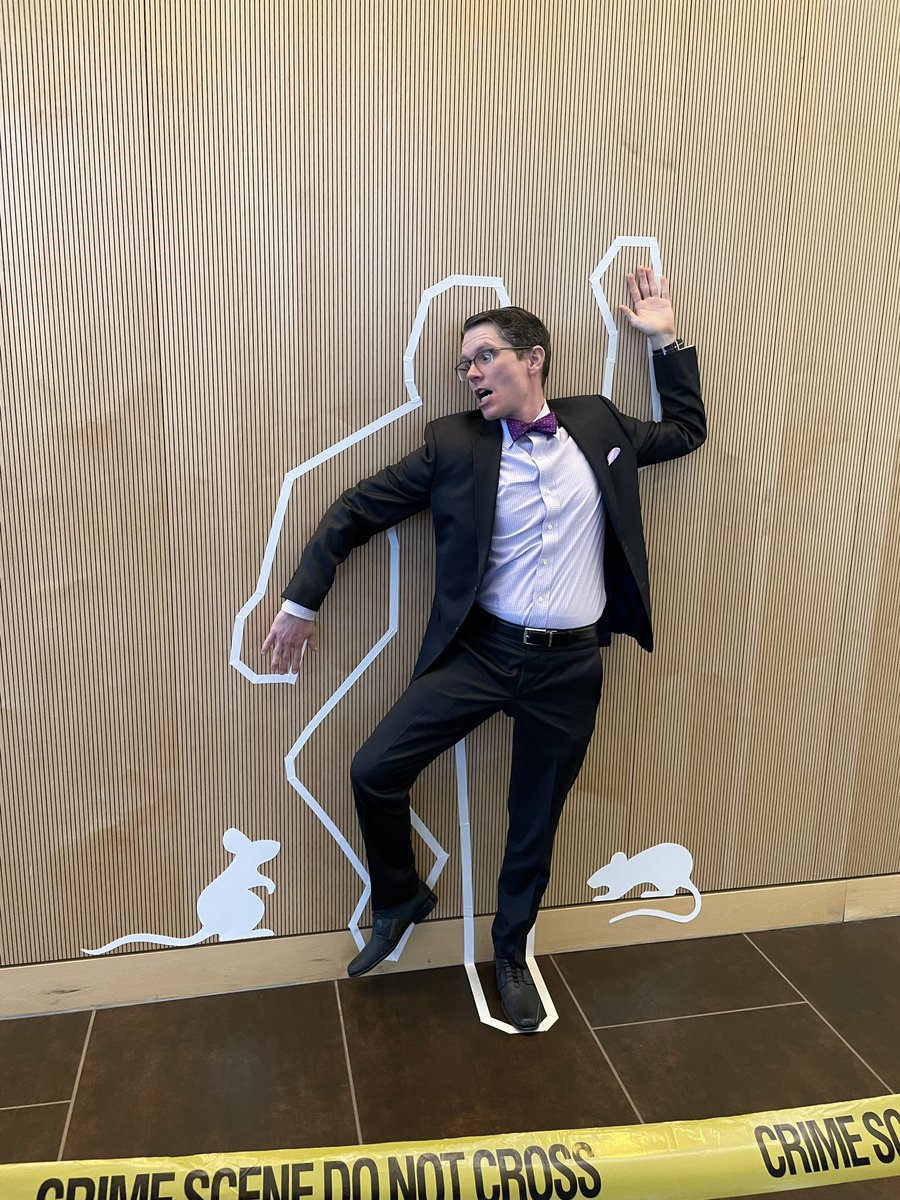
@ShawnHymel I have seen it twice, including in the West End in London. A fabulous play and a great performance. Glad you enjoyed!
English
Went to see The Mousetrap by Agatha Christie last night. It was a fun performance and had me guessing who the killer was until the end. #theatre
English

@matrosov @daveaitel And there is likely enough to reuse that could be deniable - not definitively linked back to the same individual(s) or group that were responsible for this incident. The wonders of open source!
English

My five cents. Not the entire toolchain, but parts of this complex framework could be reused. It's just too expensive to be a one-shot. We just scratched the surface on the analysis side of it. It's way more complex than it looks from current public reports.
There are a lot of previous incidents when not the entire chain, but some pieces of it could be reused in previous operations or tested separately.
English

I would be shocked if it WAS reused. Professionals build isolated tool chains for a reason. We covered this in Unethical Hacking 101 in 2004! :)
Dino A. Dai Zovi@dinodaizovi
I would be *shocked* if this code was only used for this attack... There is so much reusable kit in both the shell script and the injected payload that I think it's reasonable to assume that they have also been used elsewhere.
English

@mr__catmann @endless_sine I find @GoHugoIO works very well. It does need more technical skill than tools like Wordpress but there are plenty of free templates.
English

@endless_sine Will anyone be interested in a simple CMS or even website builder (not everyone is tech-savvy and wants to learn HTML) specifically made for "handmade" websites, fansites, forum-like communities, etc.? I've been thinking about this idea for several years
English

@RvLeshrac @DeathsPirate If this tactic worked then climate campaigners would only need to string bat boxes across a road, or cover the gates to an oil refinery with bat boxes 🦇.
Bats are protected species - not bat boxes.
English

@RvLeshrac @DeathsPirate You are not allowed to disturb bats, including the places where they are nesting or breeding. But that doesn’t magically make any wooden box protected unless it is being used.
English