

ChainLight
1.6K posts

@ChainLight_io
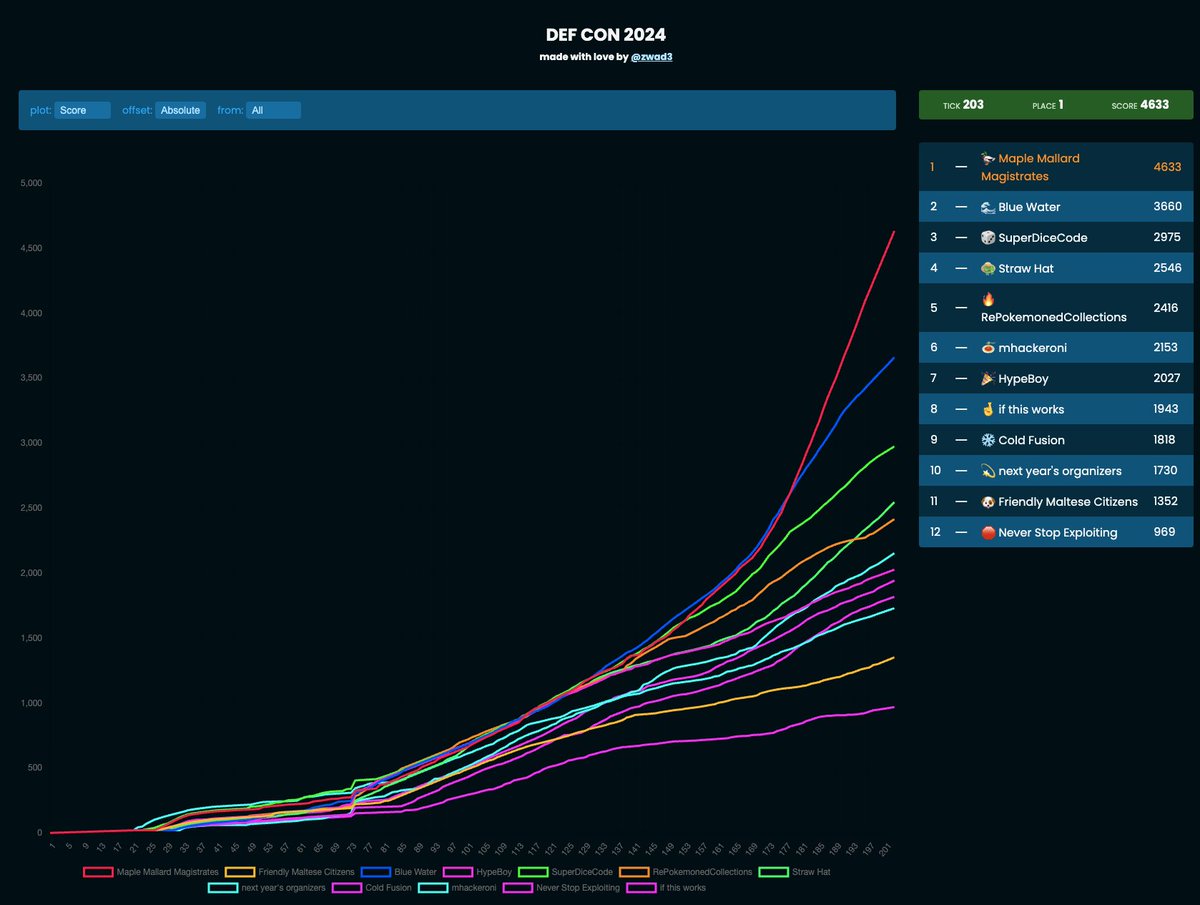
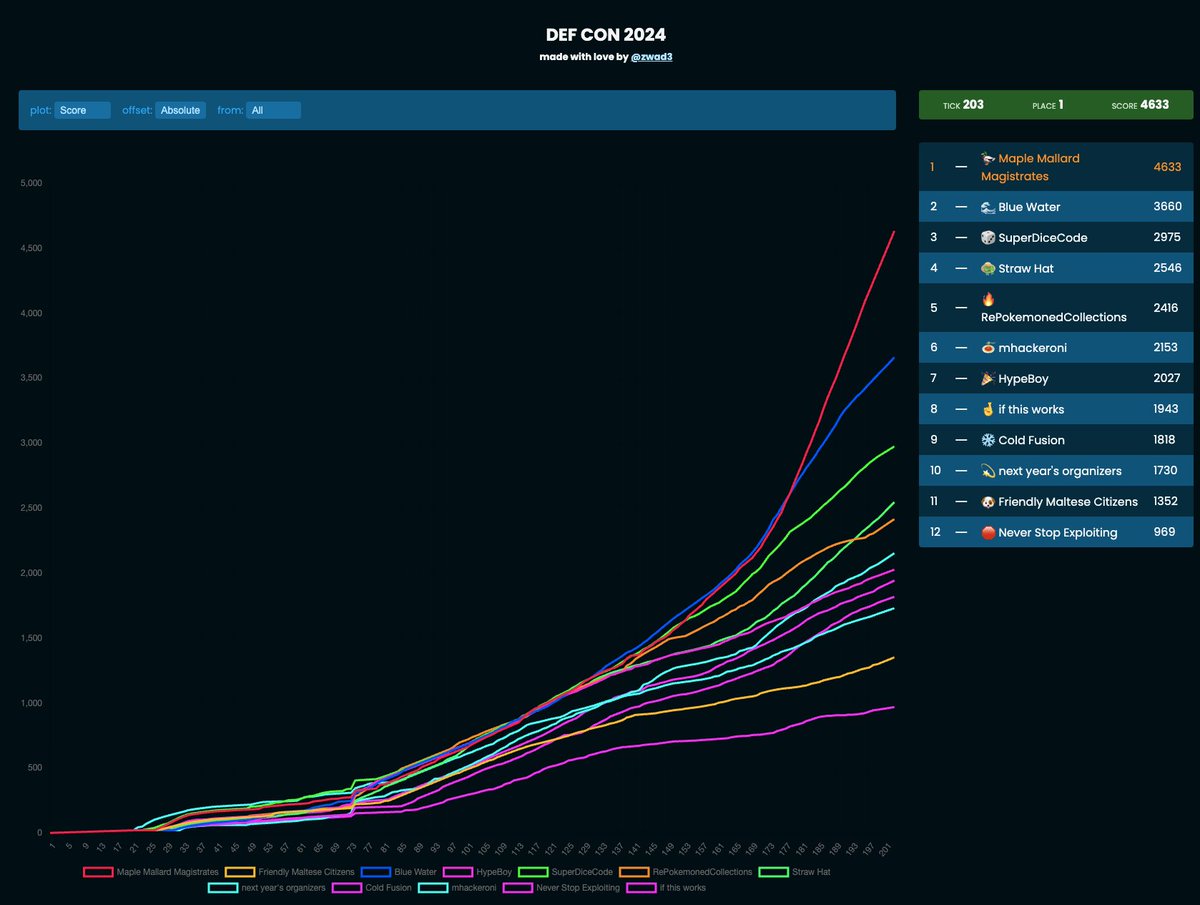
smart contract audit & token regulation and compliance | 8-time winner @defcon | winner @paradigm_ctf 23 | member @_SEAL_Org | est. 2016




Earlier today, the $1R0R staking contract had tokens removed and dumped on the open market. At this stage, we do not believe this to be an external exploit. One nefarious developer, external to R0AR core team, is seemingly behind the drain. They have been removed from the project with all accesses revoked. Some really important points: - We have a lot more liquidity than what was initially added. There is plenty in the treasury to replace this with. - Whereas with most projects this would be fatal, it isn't with R0AR, in the slightest. Our 1:1 liquidity promise at presale has transpired to be the ultimate safeguard here. We haven't spent presale funds, so there is plenty there to add back as LP. Most importantly, don't panic. There is not a team with more integrity in this space and we will make sure that we do the right thing by the community. It's a bump in the road, nothing more. Thankyou to the entire pride for your continued support. Any claims of an external hack or exploit should be ignored.


@0xNickLFranklin UPDATE: The liquidity protocol @aqualoan_io which @0xNickLFranklin was a contributor to has pulled all of it's liquidity overnight (~$800k) and deleted it's Github. github.com/techaqualoan/ hxxps[://]aqualoan[.]io/ (site still online) H/t @blackbigswan