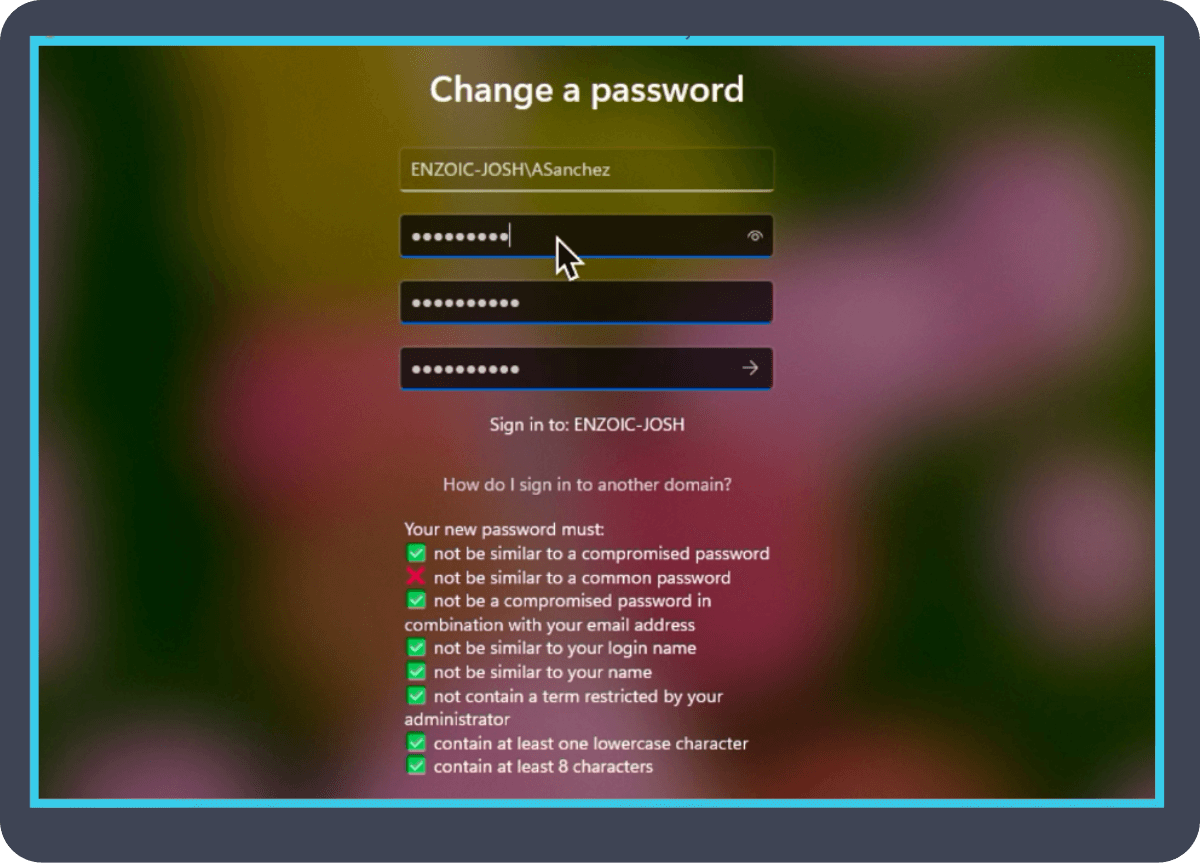
The problem doesn’t start at login.
It starts when credentials are already exposed.
New post breaking down the latest SANS identity threat findings:
hubs.ly/Q04bhlXg0
#Cybersecurity #ThreatIntelligence
English
Enzoic
4.4K posts


@EnzoicSecurity
Enzoic’s industry-leading solutions protect your customers and employees from authentication fraud online and in Active Directory.