AndreaPN@AndreaPN
🚨 Below is the @KelpDAO step by step flow of the hack from the @LayerZero_Core 's postmortem.
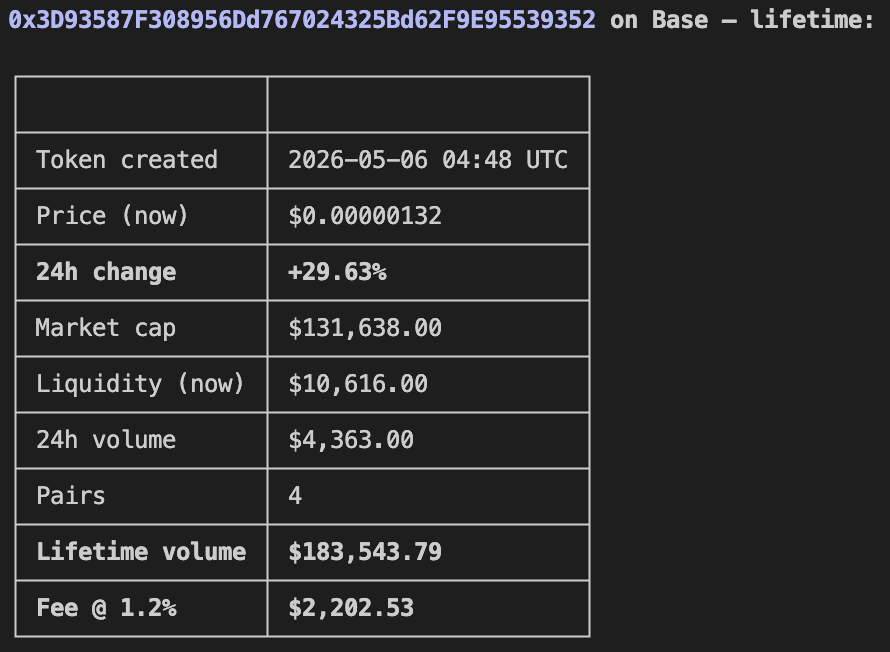
The hacker started by collecting the RPC node list, then quietly replacing the op-geth binary on two nodes. From that point, they ran two tactics at the same time: selective RPC spoofing and DDoS.
With selective spoofing, they sent fake data only to the DVN, while everyone else including LayerZero Labs monitors still saw real data. At the same time, they launched DDoS attacks on healthy nodes, forcing the DVN to switch over to the compromised ones.
The real weak point was KelpDAO using a 1-of-1 DVN setup. This meant only one verifier was needed. imo, if they had multiple DVNs, the attacker would need consensus across independent parties, and this exploit would likely fail.
The result: LayerZero Labs DVN validated transactions that never existed, leading to around $290M in rsETH drained. After that, the attackers wiped the compromised nodes to remove traces.