



dougy
921 posts

@R3dHash
Cyber Threat Intelligence | OSINT | Misinformation | Threat Hunting












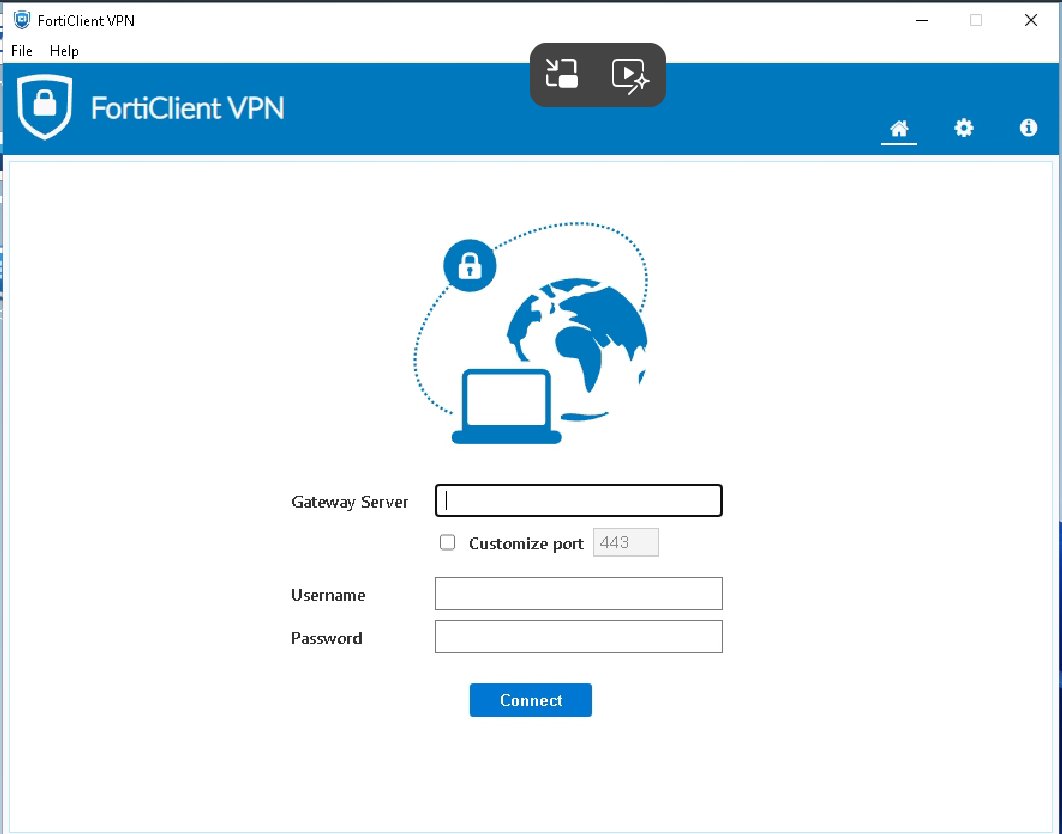
Watch out for fake Fortinet websites! Also do not blindly trust search engines AI summarizations as they can also lead to malicious redirects. These redirects lead the user to a phishing site asking FortiClient credentials, sending to myfiles2[.]download, and downloading legit builds as decoy after a valid submission >> Redirect vpn-fortinet[.]github[.]io fortinet-vpn[.]com >> Phishing vpn-fortinet[.]com





⚠️ Our threat intel team just caught attackers using a clever new trick to bypass security tools: cache smuggling. Instead of downloading malware, they hide it in fake images that browsers automatically cache. Then PowerShell extracts and runs it—no web requests needed.





@sahilypatel From software, equipment to materials, China is reconstructing an entire ecosystem inside the country





