K4e
284 posts

K4e
@YKatone
K4e just somebody who want live on bug bounty in full time.
가입일 Temmuz 2024
141 팔로잉385 팔로워
K4e 리트윗함

I’ve officially launched my startup. To kick things off, I'm offering a free 72-hour full blackbox pentest for startup/org digital assets. If you're interested, say "hello," and I'll reach out.
DorkixAI@DorkixAI
DorkixAI An autonomous pentest agent for offensive security researchers. $0.00 — Free security assessment ( 2 scans only & it's under control of the company ) $200 — Full blackbox pentest ( lifetime access & it's under your control )
English

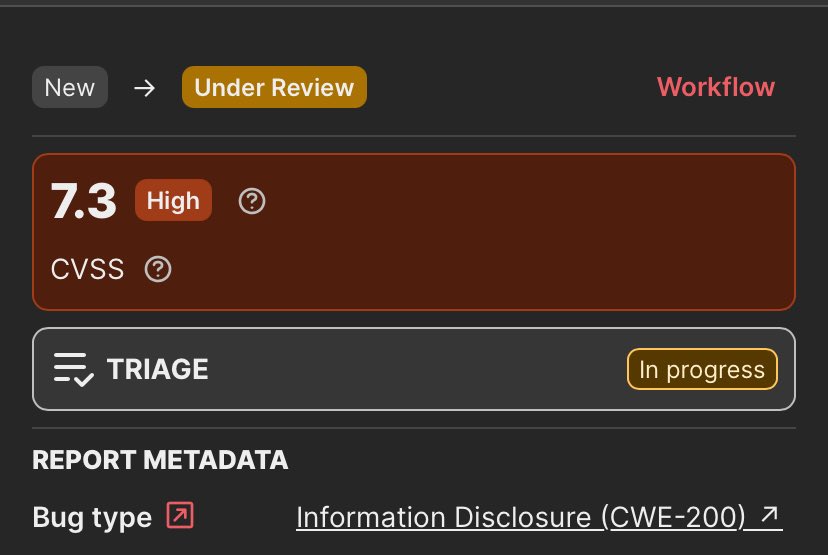
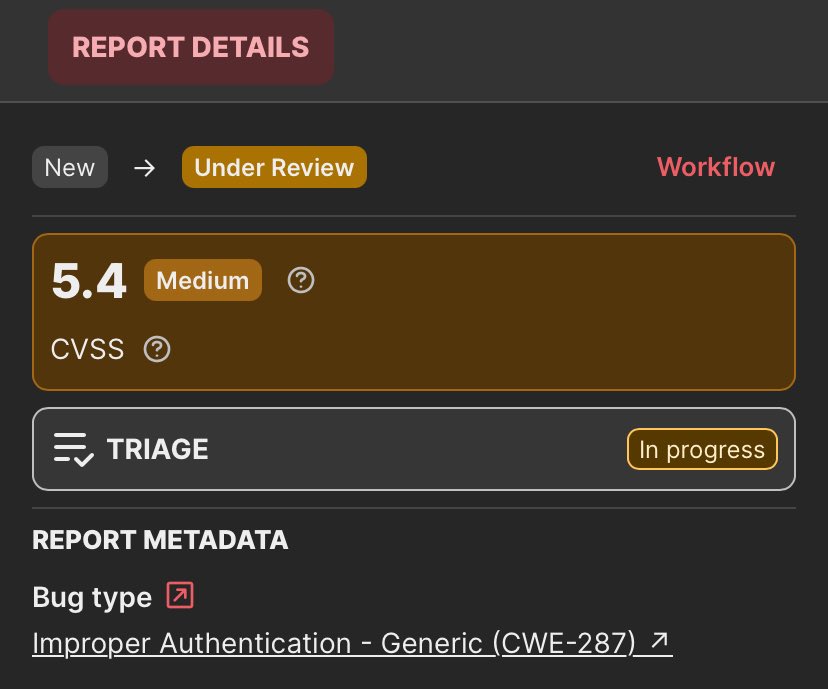
Imagine arguing with a triager on @Bugcrowd for a VDP where I'm not paid and won't earn any points.
I found a way to bypass a 401 restriction and get access to a dev JWT. I now need to prove the impact of the vulnerability...
It's getting harder to be an ethical hacker.

English

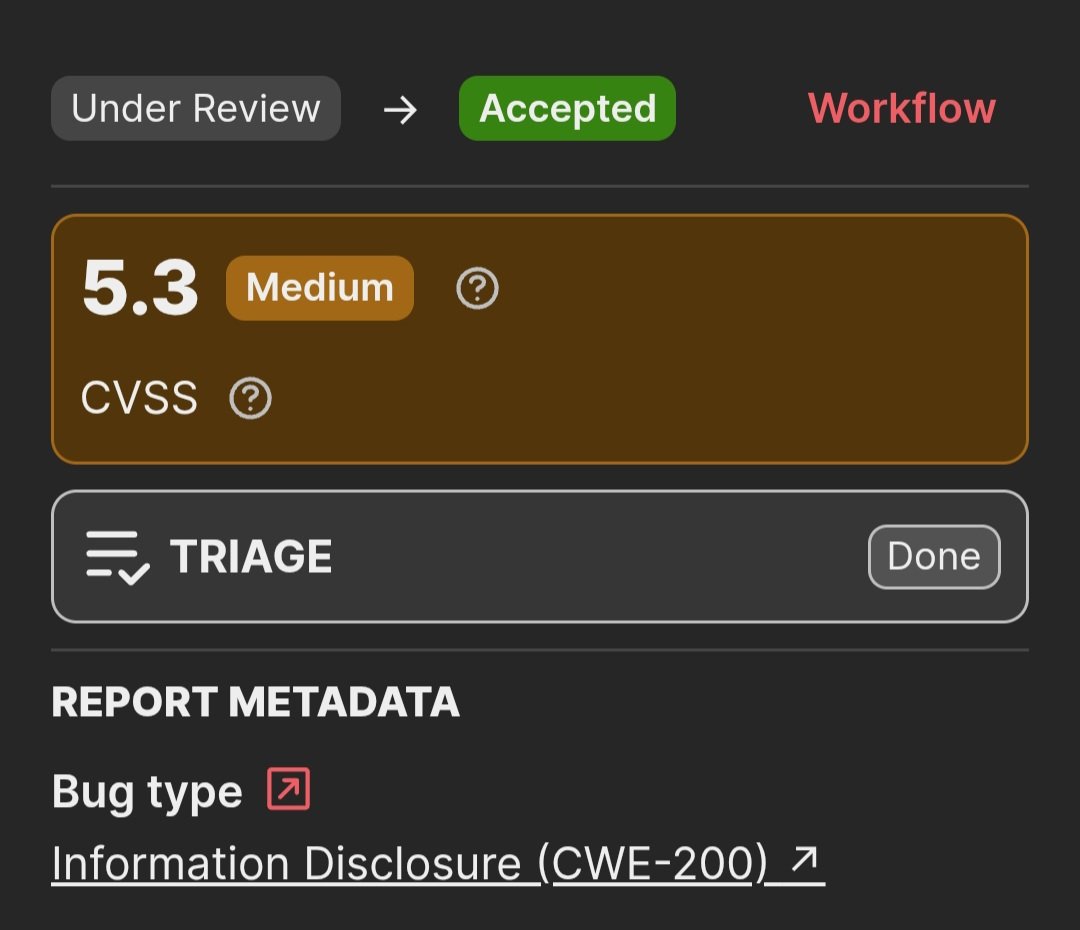
Apparently, the reset token leak via referrer is a MitM attack, so I'm being asked for more information about this report. It's so frustrating.
#bugbounty
K4e@YKatone
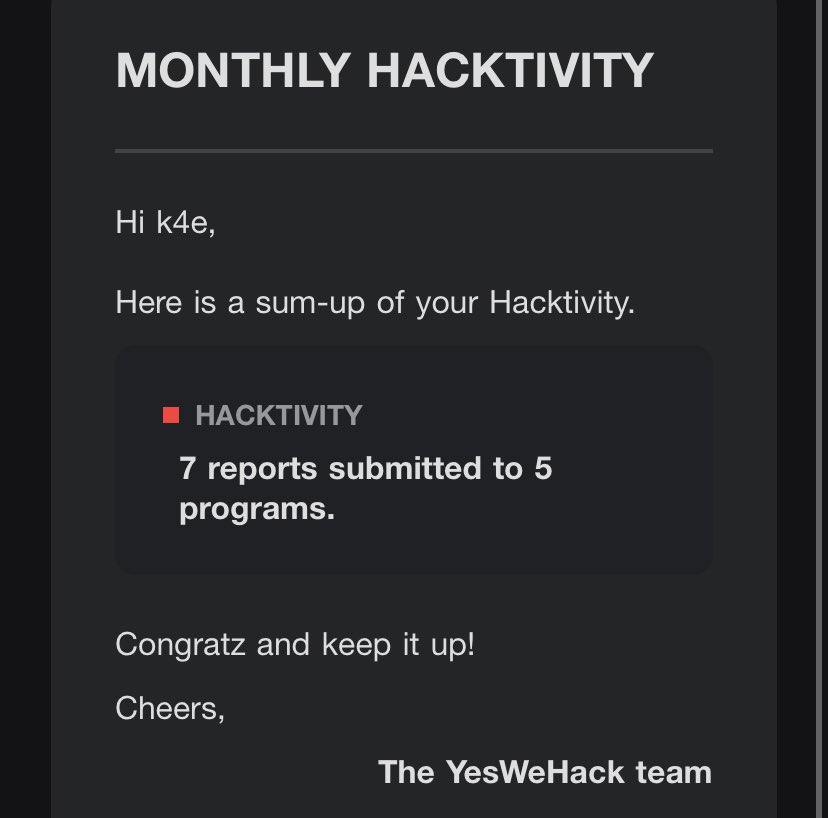
I'm crossing my fingers there won't be any more duplicates 😅 #bugbounty @yeswehack
English

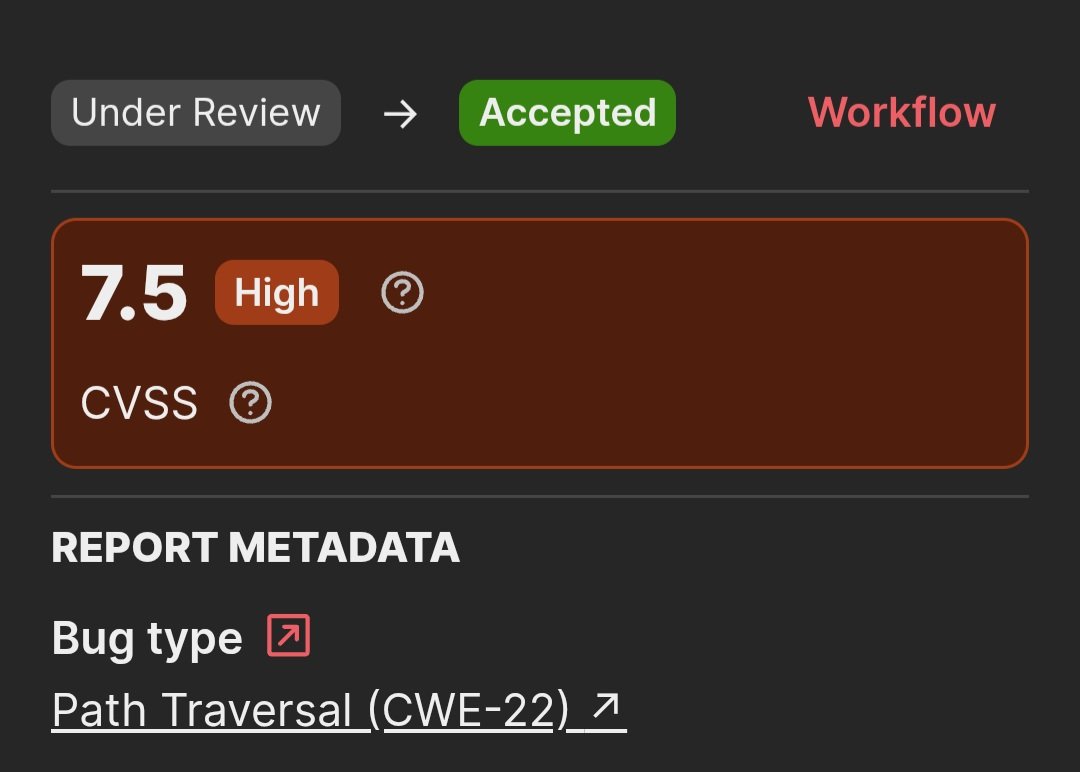
I’ve added a new entry to my CVE list , CVE number 1️⃣ 3️⃣ .
CVE-2026-4315
The issue is a Cross-Site Request Forgery (CSRF) in the Fireware OS Web UI that can allow a remote attacker to trigger a denial-of-service (DoS) condition by luring an authenticated administrator into visiting a malicious page.
Impact: High (CVSS 7.1)
Advisory: watchguard.com/wgrd-psirt/adv…
The issue was identified through @Hacker0x01 .
#bugbounty #cybersecurity #securityresearch #cve
English
@w4rcrypt @yeswehack Hey man, YWH is the platform where I started exploit hunting, so I can tell you it's the best out of habit, but no, there are programs that pay in a day after you submit your report 😅. And above all, the triage workflow means you really don't feel the wait because it's detailed
English

@YKatone @yeswehack Hey bro, can you share you experience on yeswehack platform like what’s average response time, triage experience and programs ?
English