pt200
92 posts

pt200
@_pt200
Cyber Security Engineer - Bug Bounty Hunter - Flysec Co-Founder (https://t.co/UwFfLMDys7)










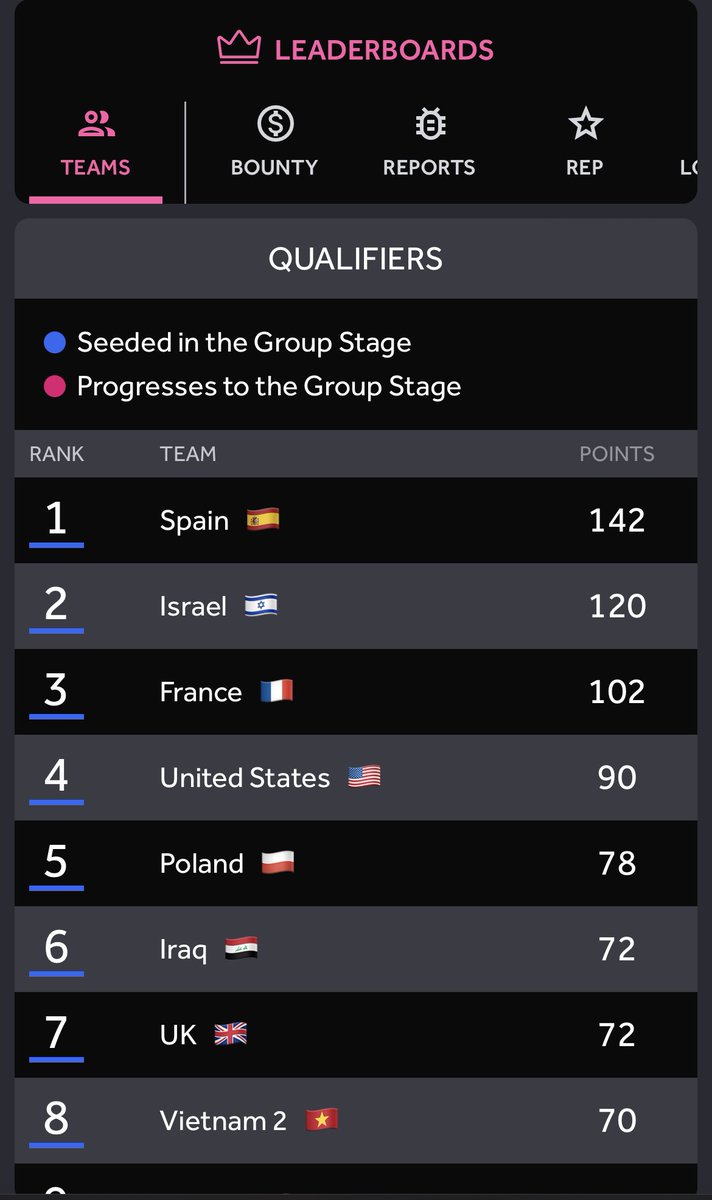
Give it up for the four teams headed to the next round of the #AmbassadorWorldCup! 🏆 👏 The teams from Greece 🇬🇷, Egypt 🇪🇬, Spain 🇪🇸 and The Netherlands 🇳🇱 dominated the Elite 8 round and will move on to go head-to-head as the final four. Who do you think will make it to the #1 spot and take home the gold?🥇














The 2024 Brand Ambassadors are ready to kick off the year right! 🙌 Thank you to everyone who submitted their applications to the program this year. Check out the thread below to see our newest ambassadors, and sign up on h1.community to join your local chapter! 🌎






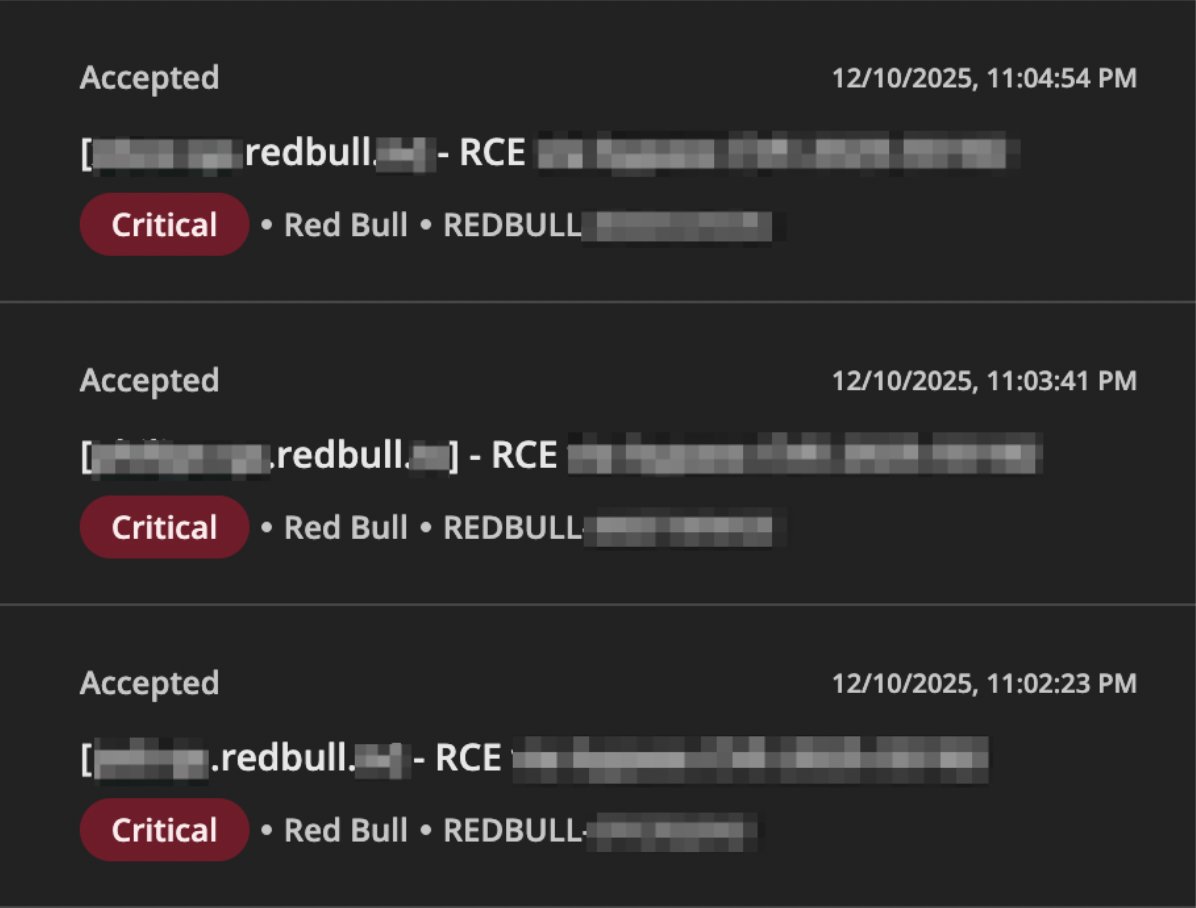
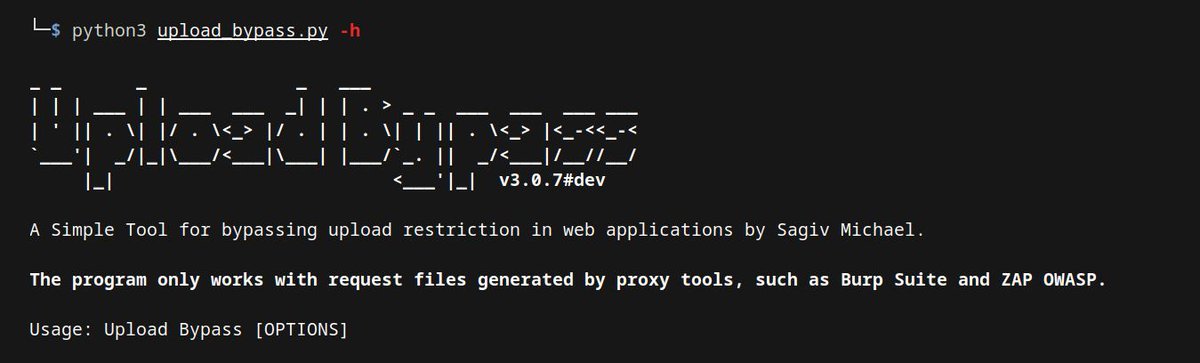
FlySec Journey's 1st month: 🔥Fired by A Critical Vulnerability affects massive companies 🔥Write-Up coming soon. Stay tune! ❤️🔥FlySec try our best to save the internet! #FlySecJourney