bk (Ben Koehl)
456 posts

bk (Ben Koehl)
@bkMSFT
Partner Director of Threat Intelligence at @Microsoft Threat Intelligence Center (MSTIC).


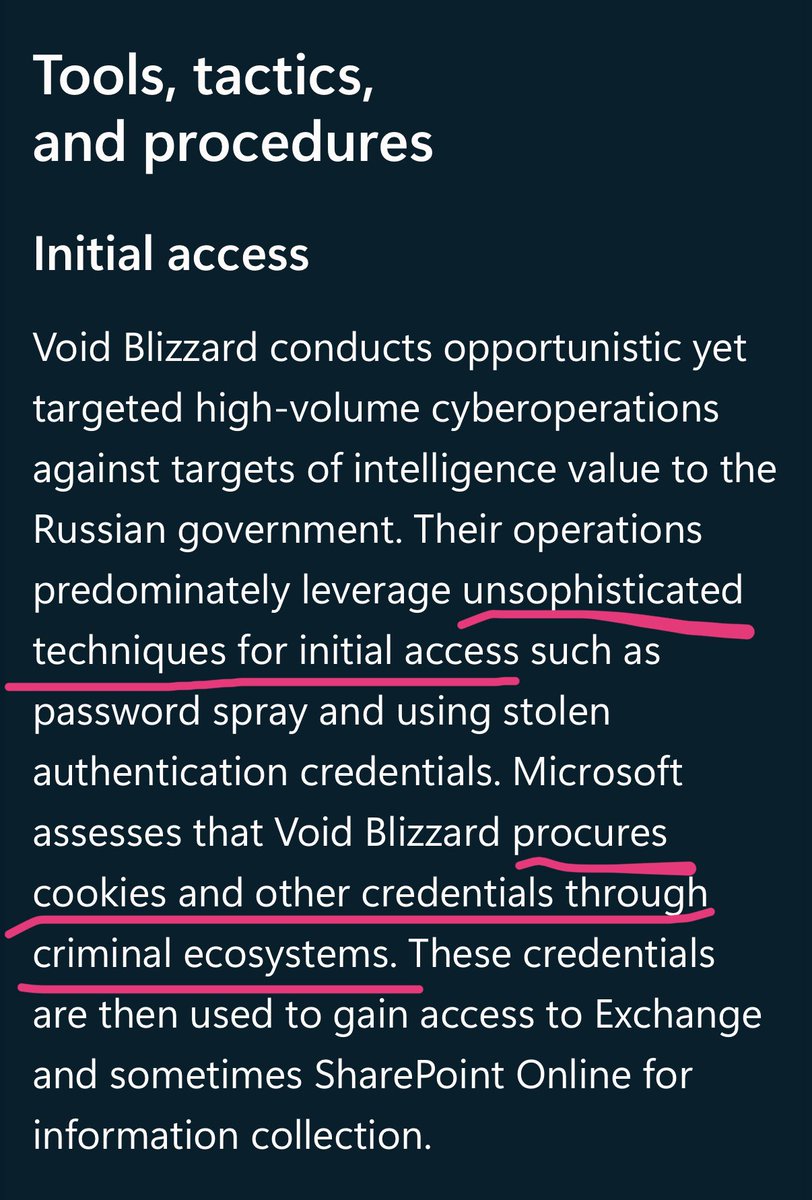

Microsoft has discovered worldwide cloud abuse activity by new Russia-affiliated threat actor Void Blizzard (LAUNDRY BEAR), whose cyberespionage activity targets gov't, defense, transportation, media, NGO, and healthcare in Europe and North America. msft.it/6011S9JpN





I'm told we are hiring in MSTIC: aka.ms/msticjobs Come for the data, stay for the data. Creative problem solvers have the most impact. If we've worked together, I'm happy to refer you. But...




CYBERWARCON is coming!!! Registration and CFP are now open for this year’s #CYBERWARCON! This year’s keynote will be given by the NSA’s @adamski_morgan. The in-person event is in Arlington, VA on Nov. 22nd and virtual tickets are available. 1/x cyberwarcon.com