bsky.affine.group 리트윗함
bsky.affine.group
189 posts

bsky.affine.group 리트윗함

Can LLMs write software that reasons? mikolasjanota.github.io/blog/2026-03-1… #llm #smt #logic #claude
English
@bl4sty @Lina_Hoshino Hey @blasty! I don't have much to say, I guess we just have to live with it. Maybe onsite with screen recording could still work as a competitive option. I also hope for more uncompetitive ctfs/challenges with clear AI discouragement.
English
bsky.affine.group 리트윗함

@lina/116198976928184530" target="_blank" rel="nofollow noopener">vt.social/@lina/11619897… this sums up the CTF vs LLM stuff nicely. Good job @Lina_Hoshino !
the competitive metric (ctftime) is dead/a gimmick at this point...
.. as a retired and washed up competitive ctf player with user id #18 on ctftime it is kinda saddening to see it implode like this. ;-(
I simply don't see any workable solution to bring back fair competitive CTF (with varying difficulty).
you could argue "well anyone can use the LLM's, that levels the playing field". by definition that means
1) you need anti-LLM (difficult) tasks, killing the element of having varying difficulty ("something fun for everyone").
2) teams/entities with cashflow could buy more clankers/compute/access to more expensive models, etc.
3) you're really gonna sit there and watch codex dream up "the house of force" instead of revisiting github dot com slash shellphish slash how2heap all by yourself
and yes I'm aware of all the various "underhanded" CTF tactics teams have employed over the years (where is that picture of the iceberg?); but forcing everyone who wants to compete to start using the ridiculous cheatcode doesn't feel like it addresses/fixes anything..
back in the days when we had to address fairness adjustment in the scoring algo of individual CTFs or ctftime as a whole we'd have a civil discussion (that would sometimes quickly erupt into a full on flamewar) on IRC with the involved parties. I'm afraid the solution is not so simple this time around :)
yo @kyprizel @leetmore @snkdna @hellman1908 I'm curious to hear how you people feel/think about this situation
English
bsky.affine.group 리트윗함
bsky.affine.group 리트윗함
bsky.affine.group 리트윗함
🤯 Quarkslab spent five months trying to report vulns to security vendor Avira/Gen Digital but hit a deadlock because Gen Digital would only accept reports through their bug bounty platform (which required an NDA), so Quarkslab eventually just emailed the report and published after 90 days.
This timeline explains the madness blog.quarkslab.com/avira-deserial…
English
bsky.affine.group 리트윗함

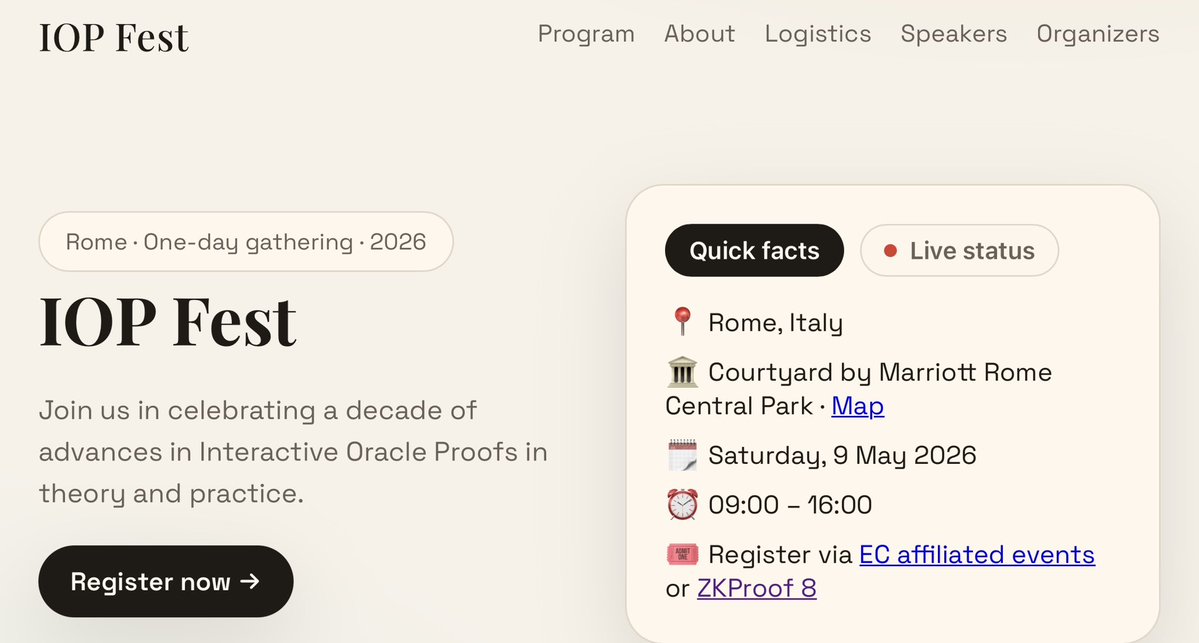
1/11 Lean Ethereum is preparing for a PQ future.
But how secure are the hash-based SNARKs powering it?
A recent $1M prize by the EF sparked a flurry of papers.
Here is the breakdown of the discussion between @nico_mnbl, @asanso and @GiacomoFenzi for @zeroknowledgefm !🧵👇
English
bsky.affine.group 리트윗함

Google has identified an iOS exploit kit named Coruna. 5 full exploit chains, 23 vulnerabilities, documentation in native English, modular architecture. Full professionalism. It must have cost millions of dollars. Who built it? Google doesn’t say, but the evidence points to US government tools. The kit also contains components previously used in a cyber operation that Russia attributed to the NSA.
Coruna traveled. First, an anonymous “company client”, then used by a Russian cyber espionage group, which hid the code on Ukrainian websites inside a visitor-counter script, delivering it only to selected users from a specific geolocation. Later a financially motivated actor “operating from China” deployed it (infecting over 42,000 devices).
The malware added to the ready-made kit was lower quality than the original suggesting the tools were acquired and modified by someone else. One US government subcontractor, Peter Williams, just received a 7-year prison sentence for selling tools to Russian broker Operation Zero. The US government spent millions on a tool that now steals cryptocurrency. A good return on investment, just not for themselves. One more detail: Coruna did not attack devices with Lockdown Mode enabled. cloud.google.com/blog/topics/th…
English
bsky.affine.group 리트윗함

Still only few days before the deadline extended #africacrypt #hammamet #tunisia
We are waiting your submissions
africacrypt2026.tn
English
bsky.affine.group 리트윗함

We are pleased to share that using Gauss, we have completed a ~200K LOC formalization of Maryna Viazovska’s 2022 Fields Medal theorems on optimal sphere packing in dimensions 8 and 24.
This is the only Fields Medal-winning result from this century to be completely formalized, and is the largest single-purpose Lean formalization in history.
We are honored to have assisted @SidharthHarihar1 and the rest of the sphere packing team in this achievement.
math.inc/sphere-packing
English
bsky.affine.group 리트윗함

Two counterintuitive puzzles, from @alexbellos and @fortnow.
blog.computationalcomplexity.org/2026/02/a-prob…
English
bsky.affine.group 리트윗함

90-day disclosure deadlines are insufficient if attackers are only 60 days behind.
Despite decades of progress in software security, it has never been easier to find vulnerabilities at scale. It's crucial that defenders scale up efforts to find and fix these vulnerabilities before attackers get to them.
We are running Xint Code on high-impact targets, and are reporting multiple high severity vulnerabilities each day. Several recent findings could be used to compromise fully-patched flagship devices. Our only bottleneck is the (understandably) high bar for reports set by responsible disclosure policies.
Finding these bugs is not difficult. We simply point Xint Code at the source code, describe the attack surface and scope we care about, and it handles the rest.
The hard part is writing up the bug reports, meeting the project-specific bug demonstration requirements, and working with maintainers to ensure the bugs get fixed correctly.
We have worked incredibly hard on Xint Code, but attackers are surely working hard on their own systems built with open-weight models. How far behind are they? With the pace of progress, both in AI models and in the security tooling built with them, it's increasingly hard to predict how the offense/defense balance will shift.
English
bsky.affine.group 리트윗함
bsky.affine.group 리트윗함
bsky.affine.group 리트윗함
bsky.affine.group 리트윗함
bsky.affine.group 리트윗함

Call for CHES 2026 Challenge Organisers
ches.iacr.org/2026/callforch…
English
bsky.affine.group 리트윗함

Video is up (video.cr.yp.to/2026/0203/vide…) for my first talk on the new speed records from sorting.cr.yp.to for sorting integer arrays. I hadn't recorded the live presentation last week but I did a retake for a general audience. Slides are also up: cr.yp.to/talks/2026.02.…
English
bsky.affine.group 리트윗함

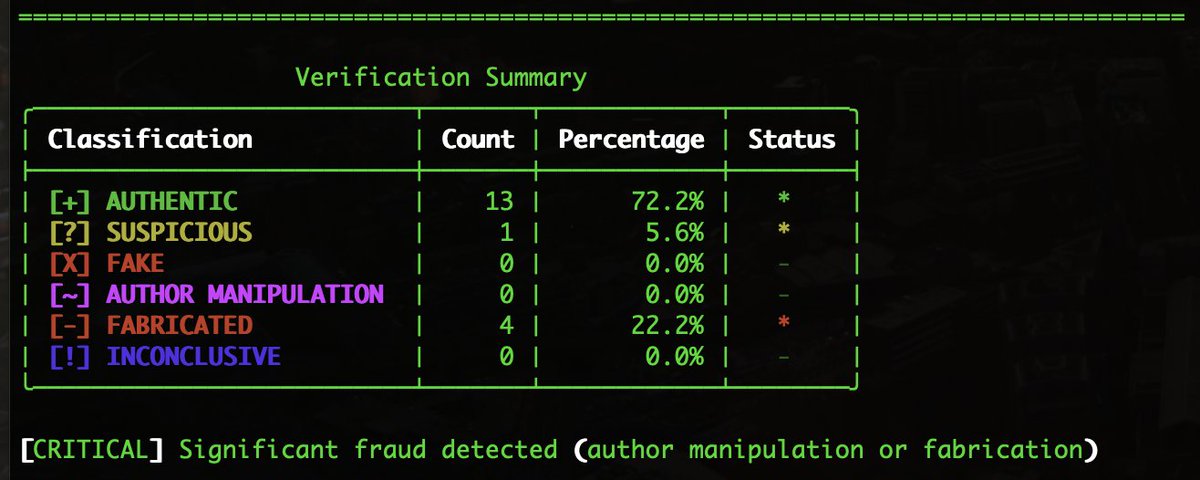
VerifyRef: Detect fabricated references in academic papers
LLMs can generate fake citations. VerifyRef cross-checks references against 8+ databases (+ optional AI) to catch them.
pip install verifyref
verifyref paper.pdf
github.com/hadipourh/veri…
#OpenSource #AcademicIntegrity
English