고정된 트윗
reversebrain
593 posts


reversebrain
@reversebrain
Penetration Tester | Red Team Operator | Incident Response Operator | CTF player with @mhackeroni
/dev/null 가입일 Mart 2012
581 팔로잉2K 팔로워
reversebrain 리트윗함

New writeup from @_specters_ and I: we're finally allowed to disclose a vulnerability reported to Kia which would've allowed an attacker to remotely control almost all vehicles made after 2013 using only the license plate.
Full disclosure:
samcurry.net/hacking-kia
English

Ever heard about cross-queries? 👀
During a recent penetration test, I uncovered the powerful capabilities of cross-queries in PostgreSQL. Discover how this feature can be exploited to dump tables in complex scenarios: reversebrain.github.io/2024/09/19/Cro…
English
reversebrain 리트윗함

Firmware 1.0 released! 🔥
What’s new: Apps catalog, JavaScript support, New NFC subsystem, 2X faster Bluetooth, External radio module support and more! 🤩
Read the blog post: blog.flipper.net/released-firmw…
English
reversebrain 리트윗함
reversebrain 리트윗함

Now that we're all back and caught up on sleep it's @defcon CTF @Nautilus_CTF wrap-up time! 🐚🚩 we managed a great 6th place in a tough competition with conventional pwnage, GenAI-powered spaceships, and LiveCTF duels


English
reversebrain 리트윗함

And that's it for this year @defcon #CTF: your favorite Italian team got 6th place after 3 intense days of !sleeping. Thanks to the organizers @Nautilus_CTF and all the amazing teams that competed with us in this backdoor-sharing event!
See you next year! ♥️
#defcon #defcon32



English
reversebrain 리트윗함
Some of you may already be aware but due to extenuating circumstances we've made an early award!
The 2024 Pwnie for Epic Fail goes to @CrowdStrike for the CRWD2K bug! 🦃

English
reversebrain 리트윗함

I don't do Windows but here are some (initial) details about why the CrowdStrike's CSAgent.sys crashed
Faulting inst: mov r9d, [r8]
R8: unmapped address
...taken from an array of pointers (held in RAX), index RDX (0x14 * 0x8) holds the invalid memory address
@_JohnHammond


English
reversebrain 리트윗함

Job 1 in repairing CrowdStrike.. get access to computer.
techAU@techAU
This is the reality for IT Admins hit by @CrowdStrike hope they send an invoice for their time and downtime.
English
reversebrain 리트윗함
reversebrain 리트윗함

🔥 XSS on any website with missing charset information? 😳
Attackers may leverage the ISO-2022-JP character encoding to inject arbitrary JavaScript code into a website. Read more in our latest blog post:
sonarsource.com/blog/encoding-…
#appsec #security #vulnerability

English
reversebrain 리트윗함

My latest blog about my discovery for Evernote Client All-platform RCE via PDF.js font-injection to preload.js exposed ipcRenderer-BrokerBridge-boron.actions bypassing Electron's nodeIntegration | context-isolation;
Enjoy reading!
0reg.dev/blog/evernote-…
English
reversebrain 리트윗함

JULIAN ASSANGE IS FREE
Julian Assange is free. He left Belmarsh maximum security prison on the morning of 24 June, after having spent 1901 days there. He was granted bail by the High Court in London and was released at Stansted airport during the afternoon, where he boarded a plane and departed the UK.
This is the result of a global campaign that spanned grass-roots organisers, press freedom campaigners, legislators and leaders from across the political spectrum, all the way to the United Nations. This created the space for a long period of negotiations with the US Department of Justice, leading to a deal that has not yet been formally finalised. We will provide more information as soon as possible.
After more than five years in a 2x3 metre cell, isolated 23 hours a day, he will soon reunite with his wife Stella Assange, and their children, who have only known their father from behind bars.
WikiLeaks published groundbreaking stories of government corruption and human rights abuses, holding the powerful accountable for their actions. As editor-in-chief, Julian paid severely for these principles, and for the people's right to know.
As he returns to Australia, we thank all who stood by us, fought for us, and remained utterly committed in the fight for his freedom.
Julian's freedom is our freedom.
[More details to follow]
English
reversebrain 리트윗함
reversebrain 리트윗함
reversebrain 리트윗함

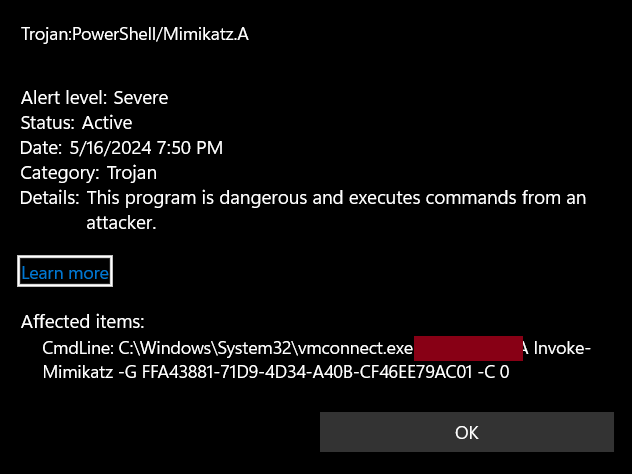
The most sophisticated exploit we've ever seen.
Thank you to @wdormann for bringing this to our attention. This is basically Stuxnet. 2.0

English
reversebrain 리트윗함
reversebrain 리트윗함
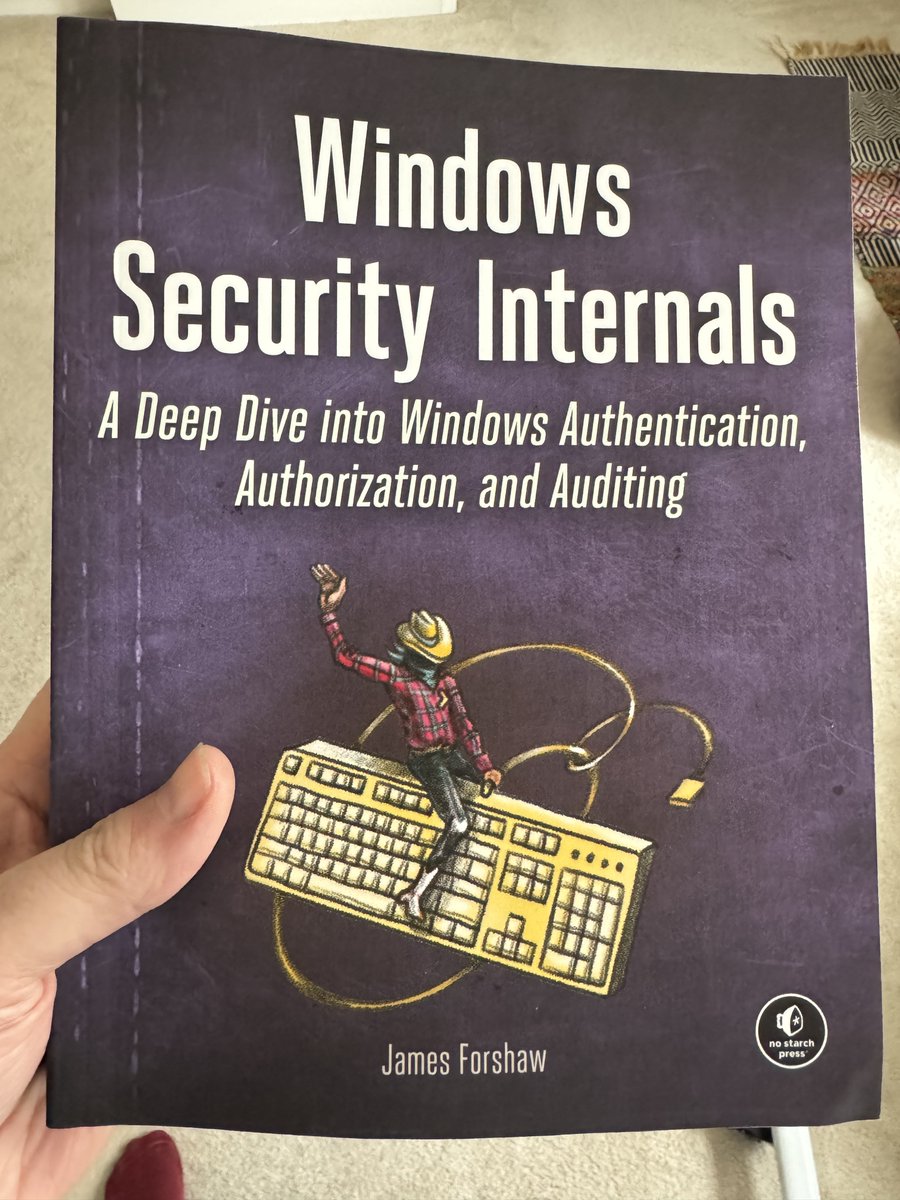
This new book has finally arrived. Thank's to @nostarch as well as @billpollock for making it happen as well as @Lee_Holmes as my tech reviewer.
English
reversebrain 리트윗함
reversebrain 리트윗함