
bugga
2.1K posts






Getting ready to cook 🧑🍳 “The Demo”




🚨 TEEs are AGAIN compromised! 🚨 This time it's even bigger! TL;DR - 3 weeks ago: Intel SGX exploit (DDR4) - Today: Exploit affecting the latest State-Of-The-Art TEEs by Intel, AMD and Nvidia (DDR5) TEEs don't bring privacy or security in crypto. All you need to know 👇🧵







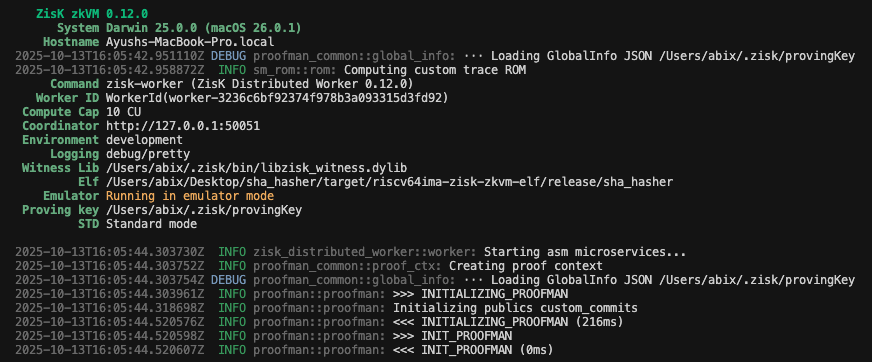
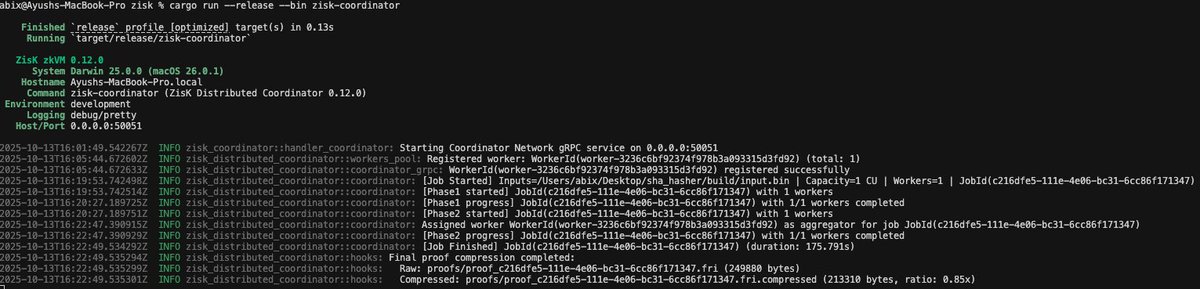

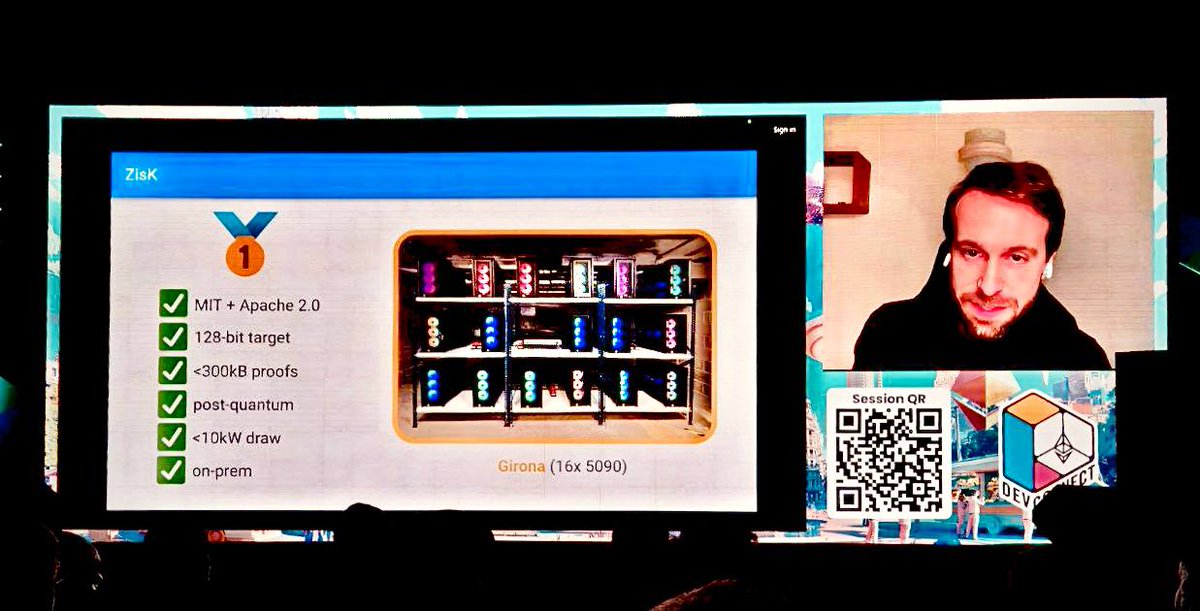
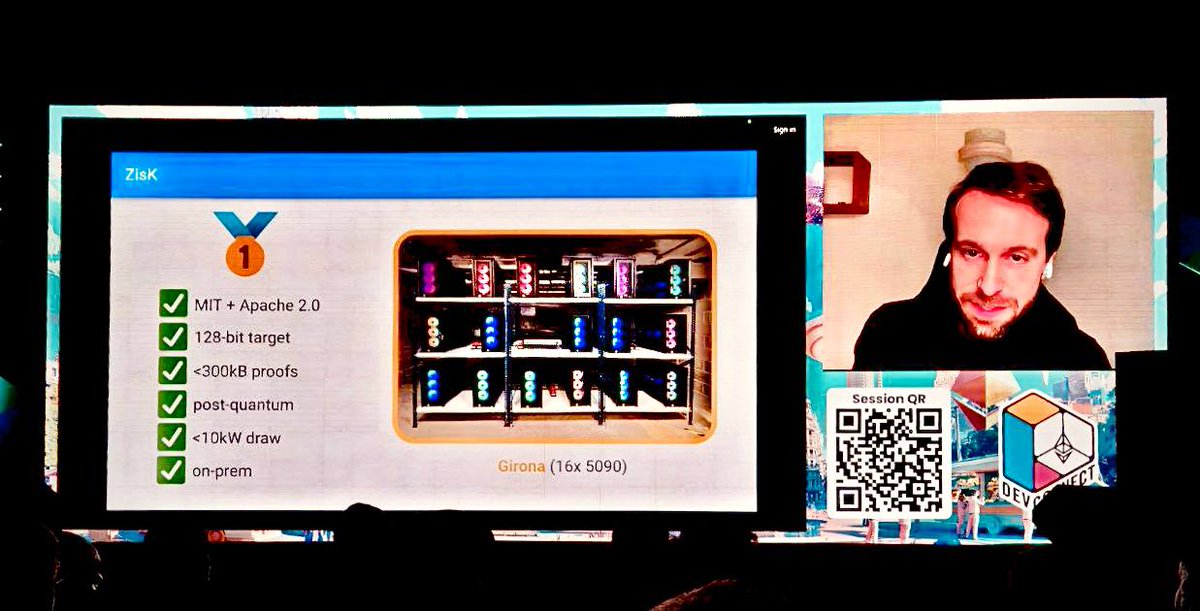
Getting started with ZisK - Part 1 This piece walks through what actually happens when you write and prove a ZisK program. It also breaks down how ZisK internally works for generating and working with @ziskvm's proof system. By the end, you’ll have an understanding of how execution and proof generation fit together in ZisK, and how you can start building private, verifiable programs. Part 2 will focus on distributed proof generation with @ziskvm






