Sabitlenmiş Tweet

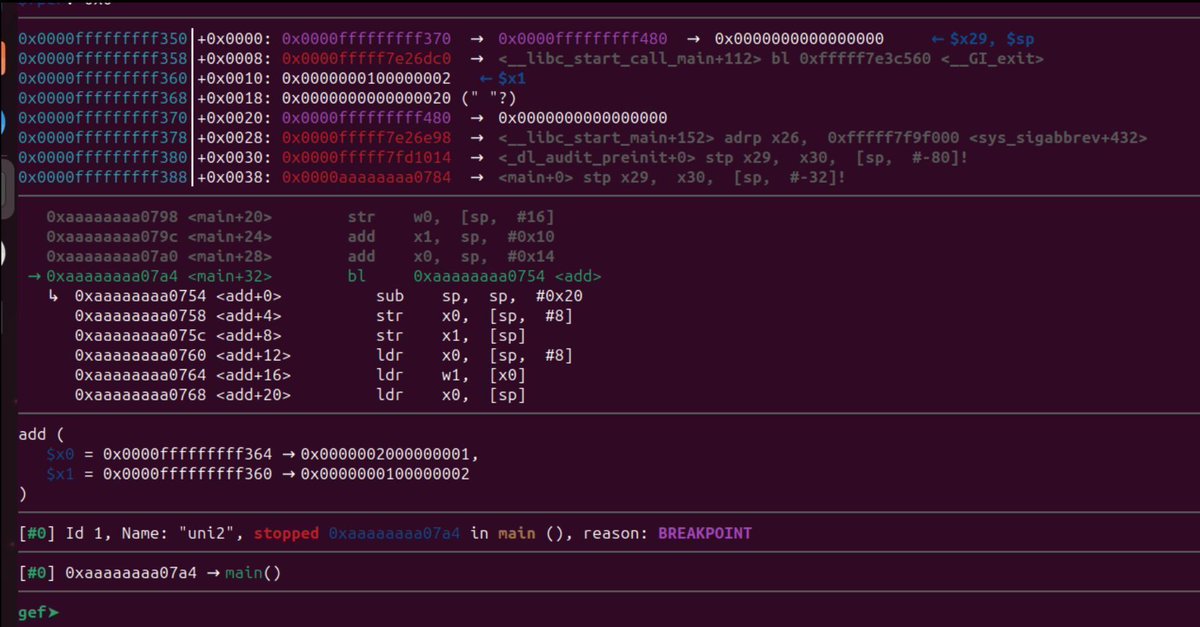
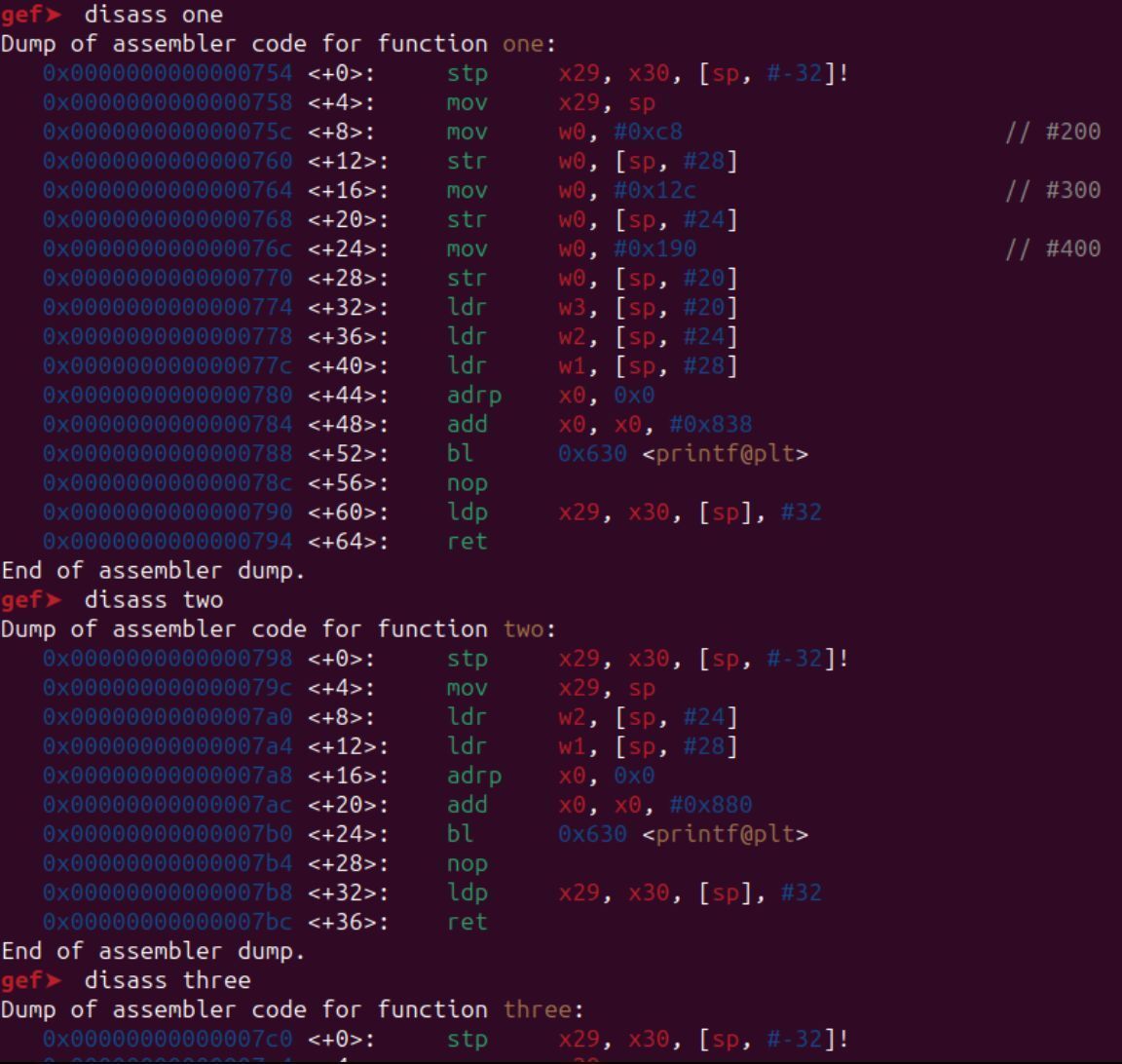
MCP servers can expose file read/write tools to AI assistants. When they do, unsafe path handling can let requests escape the intended workspace. Here are two path traversal bugs showing up in many MCP file servers.
Who needs to act:
→ Developers: check read_file + write_file for path validation and the fix is ~3 lines of Python
→ Security engineers: the example paths with traversal pattern mentioned in the image are your audit checklist
→ Security leads: no filesystem sandbox, and MCP tools run with full host process permissions
Bookmark this!
Find detailed lesson: academy.8ksec.io/course/practic…

English