Detecteam
105 posts


Detecteam
@DetecteamInc
Our REFLEX platform automates the detection lifecycle—building, testing, validating and deploying detections in minutes, not months.
























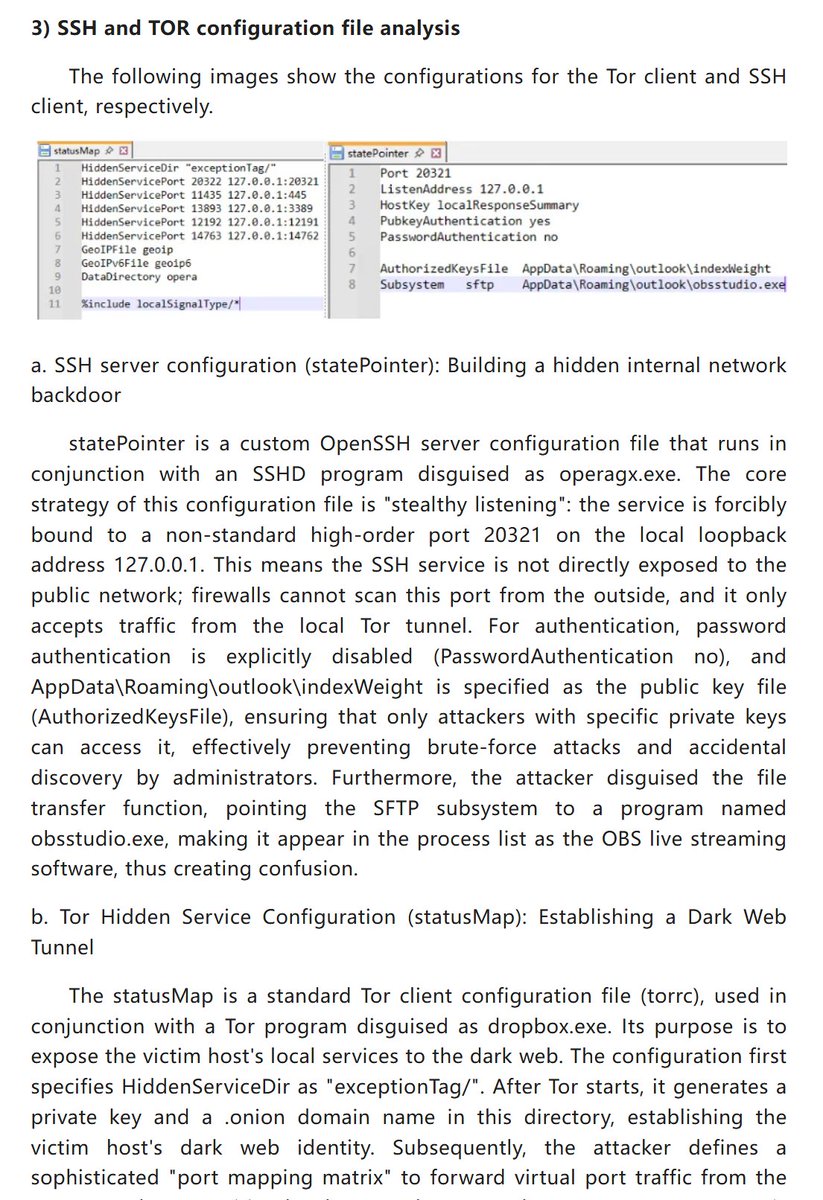
#Sandworm Targeted RDP Backdoor Campaign (2024-2026) The group has fully evolved its operational strategy from high-impact instantaneous system destruction to intelligence-driven, long-term stealthy persistence. The campaign leverages a highly modular, iterated attack framework (Tambur/Sumbur/Kalambur/DemiMur) targeting global defense industry, critical infrastructure, and government entities. mp.weixin.qq.com/s/QWe2m4qdp45u…







Genians Security Center uncovers an APT37 campaign that used social networking as an initial access vector. Two Facebook accounts set to North Korea-linked locations were used to screen targets, build trust, and move conversations to Messenger. genians.co.kr/en/blog/threat…