Day 26 of #BugQuest! 🤠
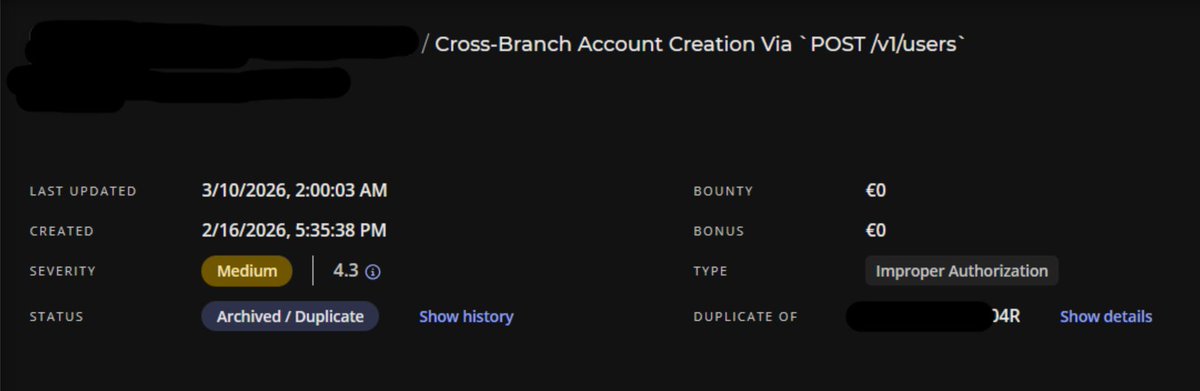
Yesterday's challenge featured a method-specific authorization check where GET requests were protected, but POST/PUT or any other requests bypassed the authorization entirely, allowing attackers to modify any user's profile data.
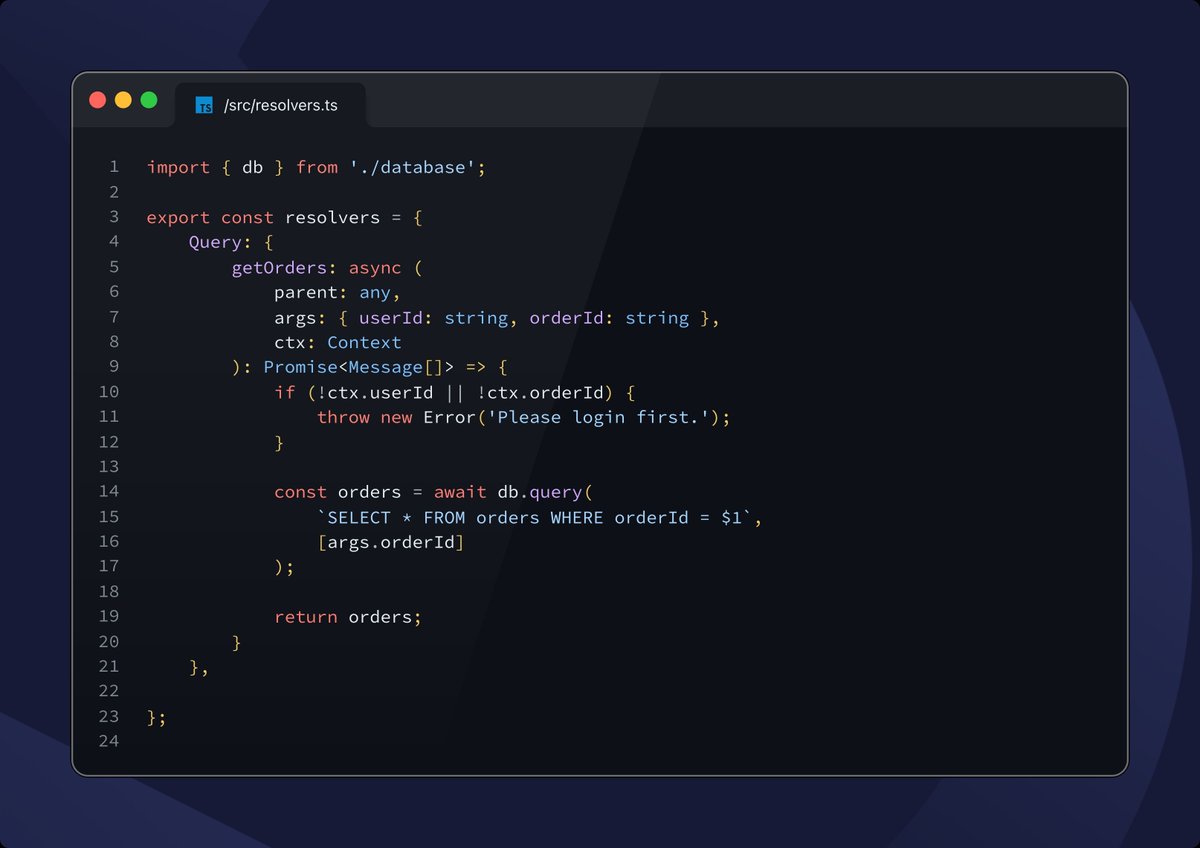
Today's challenge involves GraphQL authorization! This vulnerability pattern was covered on Day 14, where we learned about the importance of finding and testing GraphQL queries & mutations.
Can you spot the broken access control in this code snippet? 🐛
Swipe through to see the vulnerable code! As usual, solution will be revealed tomorrow!
#BugBounty #HackWithIntigriti #BugQuest



English