MHD retweetledi

Don’t rush to report.
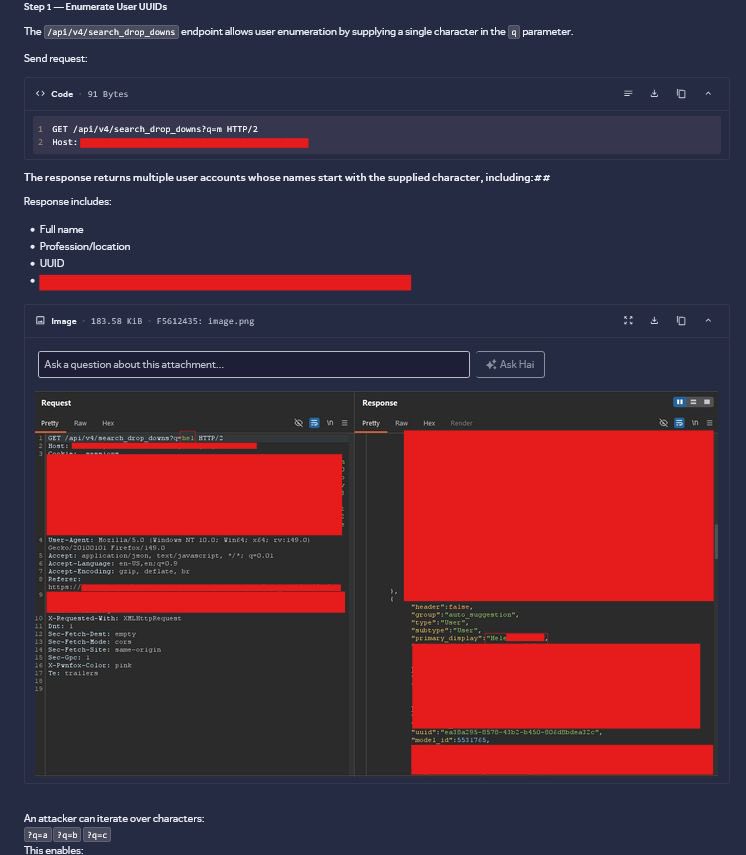
A UUID IDOR looked informative at first. Dug deeper, found an endpoint leaking valid IDs, chained both, and it became critical.
Full writeup: urli.info/1oYlx
#BugBounty #IDOR #hackerone



English
MHD
1.7K posts


@MhdAsfan
Security Researcher | Web Dev | CTF Player #web3 الحمد لله











When Live domains are over , I prefer not reachable domains to Pop SQLi💀😂