Kolja retweetledi
Kolja
124 posts

Kolja retweetledi
Kolja retweetledi

Drones are hot - their security is not.
Here is how removed the NAND, dumped firmware, and reverse-engineered ECC on a consumer drone. Stay tuned for part 2!
neodyme.io/de/blog/drone_…
English
Kolja retweetledi
Kolja retweetledi

🖨️ Print victory! Team @Neodyme just hacked the @CanonUSA imageCLASS MF654Cdw at #Pwn2Own. They head off to the disclosure room once more to provide the details of their exploit. #P2OIreland
English
Kolja retweetledi

Check out our new blog post on a research-driven look at software-only DRM. Explore how the Qiling emulation framework can be used to analyze Widevine and how Differential Fault Analysis (DFA) and emulation aid de-obfuscation.
▶️ Read more: neodyme.io/en/blog/widevi…
English
Kolja retweetledi
Kolja retweetledi
Kolja retweetledi

Kolja retweetledi
Kolja retweetledi
Kolja retweetledi

The Cyber Security Challenge Germany 2025 aftermovie is live! 🎥
Relive the highlights and the spirit of Germany's top young cybersecurity talents.
▶️ Watch now: youtu.be/D9SXZMNyk9U

YouTube
English
Kolja retweetledi

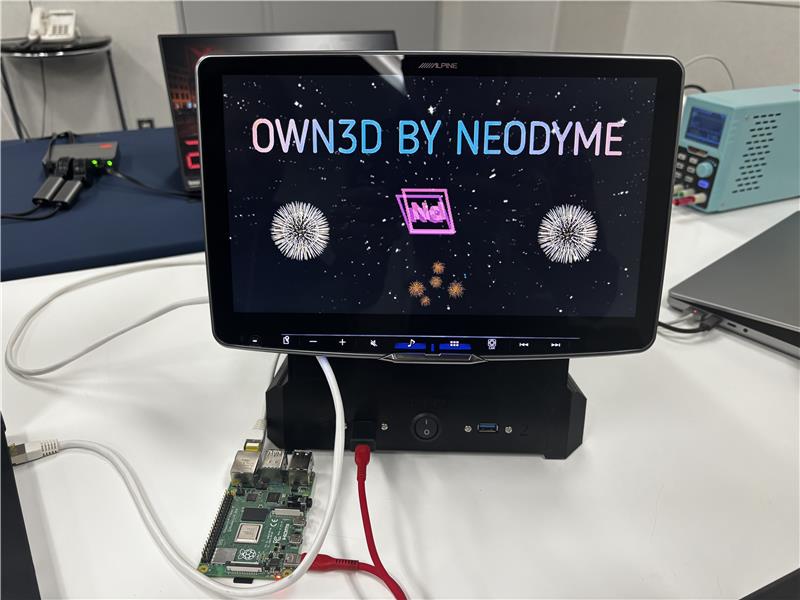
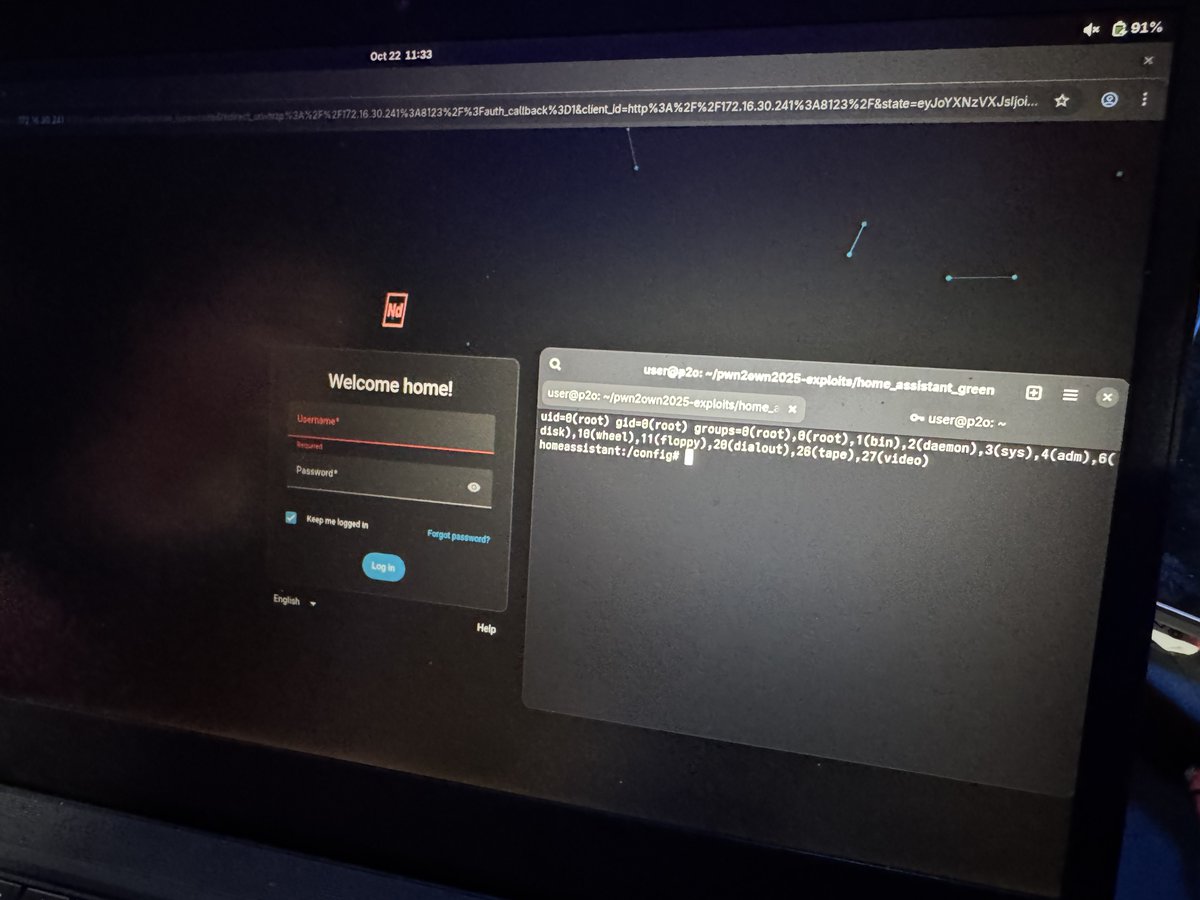
While our colleagues hack live at #Pwn2Own in Cork, take a look at our newly published last year's writeup on our blog: We compromised a QNAP router to take over a networked Canon printer.
▶️ Read the findings and how we got there: neodyme.io/en/blog/pwn2ow…
English
Kolja retweetledi

Our first confirmation of #Pwn2Own Ireland is in! @Neodyme used a stack based buffer overflow to exploit the HP DeskJet 2855e. They earn $20,000 and 2 Master of Pwn points. #P2OIreland

English
Kolja retweetledi

Heading to @hack_lu? 🔐
Our colleague Felipe will discuss how partial emulation and DFA can be used to study a legacy version of Widevine L3, Google's software-based DRM.
➡️ Dive into the past to strengthen future DRM security.
🗓️ Oct 23 at 2:15pm
2025.hack.lu/agenda/
English
Kolja retweetledi

Congratulations to Team Germany 🇩🇪 for achieving an impressive third place 🥉 at the #ECSC2025!
A fantastic performance and great spirit throughout the competition. Well done to all participants! 👏💻

English
Kolja retweetledi

It's game time at #ECSC2025!
👉 Livestream: ecsc2025.pl
👉 Live scoreboard: public.ecsc-board.pl
All the best to Team Germany and every participant. We're all watching with anticipation! 🔐
English
Kolja retweetledi
Kolja retweetledi

⚡️ Lenovo DCC contained an easy-to-exploit LPE: a weak ACL bug → local privilege escalation → full admin 🖥️👨💻
We break it down with reverse engineering, process tracing, & two exploit strategies. Read Part 1 of our deep dive: 👉 neodyme.io/de/blog/lenovo…
English
Kolja retweetledi