Your vulnerability backlog will never be zero. AI-speed exploitation made sure of that.
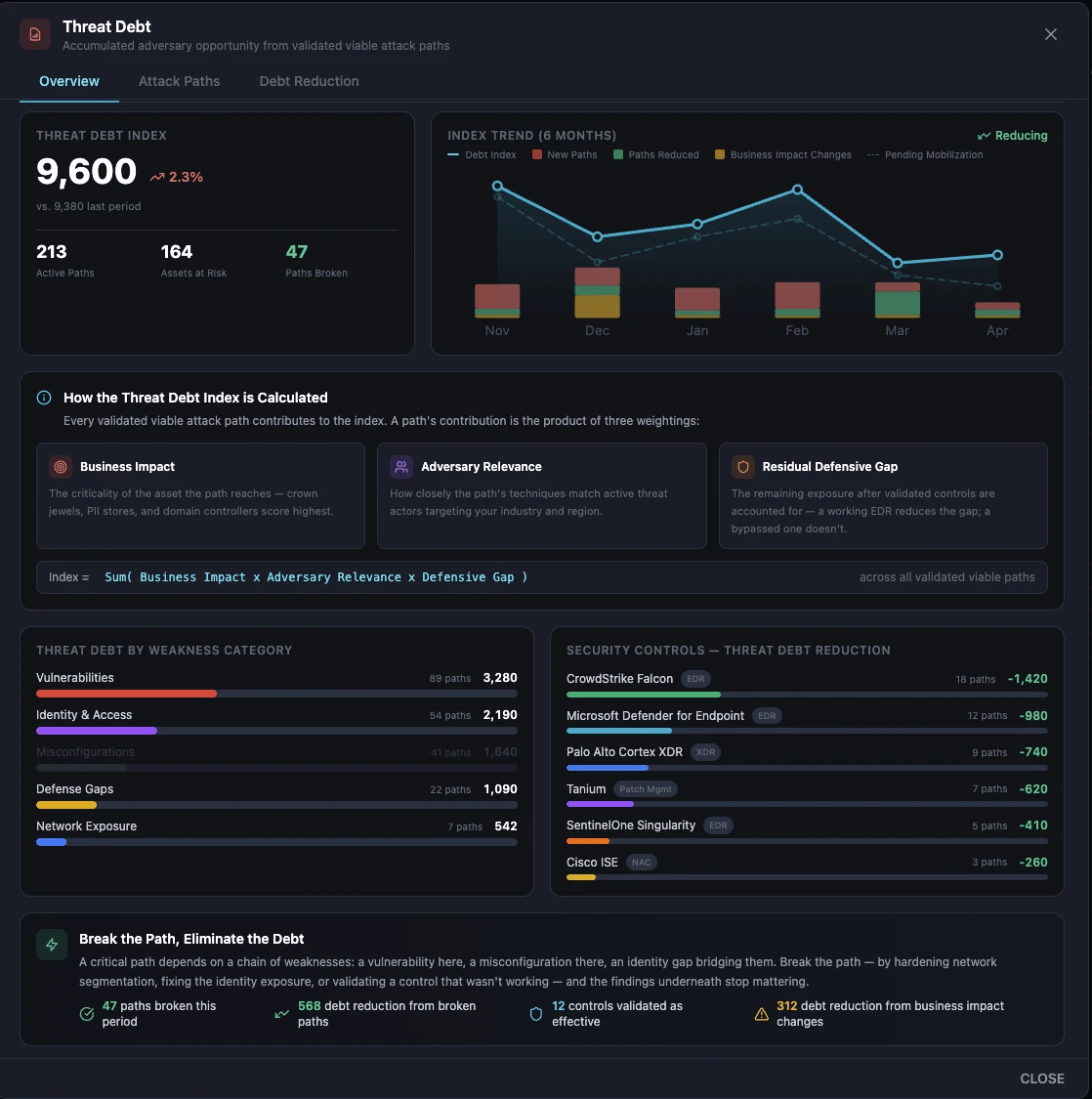
Threat debt is what accumulates when adversaries find paths faster than you break them.
Learn what it is, what drives it, and how to pay it down on May 21: attackiq.com/resources/webi…

English