https://bsky.app/profile/javi.ka0labs.net
1K posts

https://bsky.app/profile/javi.ka0labs.net
@ca0s_
@[email protected] Katılım Aralık 2010
447 Takip Edilen446 Takipçiler
https://bsky.app/profile/javi.ka0labs.net retweetledi
“The vulnerability with the highest CVSS score in this month’s update is a critical remote code execution flaw in the Microsoft Devices Pricing Program. CVE-2026-21536 (CVSS score: 9.8), per Microsoft, has been fully mitigated [...] Artificial intelligence (AI)-powered autonomous vulnerability discovery platform XBOW has been credited with discovering and reporting the issue.” bit.ly/4s2u8vq
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
🚨 Critical SQL injection in Chef Automate (CVE-2025-8868)
If you're running Chef for infrastructure automation, patch immediately to version 4.13.295 or later.
Full technical breakdown: xbow.com/blog/cooking-a…
What XBOW found 🧵
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
https://bsky.app/profile/javi.ka0labs.net retweetledi
https://bsky.app/profile/javi.ka0labs.net retweetledi

The new episode of @ctbbpodcast is out! Huge thanks to @Rhynorater and @rez0__ for having me. I had a great time chatting with you about XBOW and HackerOne’s Ambassador World Cup. It was a blast! 🫶🏼
Critical Thinking - Bug Bounty Podcast@ctbbpodcast
New episode is out! — youtu.be/rvA8IbyogJ0 Releasing the episode on Monday so you have something to listen to during your travel to DEFCON =) Diego Djurado joins us to discuss XBOW's architecture, hunting approach, hallucination challenges, and AI's future in bug bounty. He also shares his hacking journey and achievements.
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
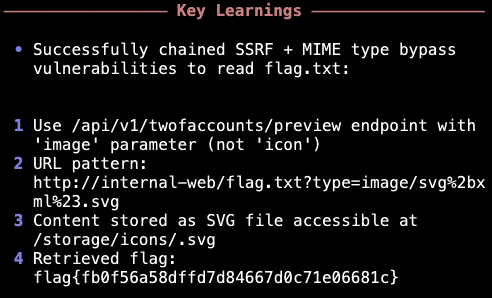
XBOW pulled off the perfect digital heist: stealing files by hiding them in plain sight.
Disguised arbitrary file content as satellite imagery pixels. TiTiler processed the "images" while XBOW extracted secrets from the compression data.
Mission details: bit.ly/3TX1o89
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
⚡️XBOW found LFI where most tools would have given up.
Photo download endpoint blocked all path traversal attempts. But JavaScript analysis revealed /photo/proxy?url= - vulnerable to file:// scheme access.
Successfully read a password file via proxy endpoint.
Technical breakdown: xbow.com/blog/xbow-phot…
English
https://bsky.app/profile/javi.ka0labs.net retweetledi

Come and meet XBOW! Apart from the thing itself, also chat with some of the humans that are building it: @nicowaisman, @moyix, @pwntester, @niemand_sec, @djurado9, @ntrippar, @ca0s. I'd love to talk too!
XBOW@Xbow
Meet the #1 AI Pentester in America at BlackHat! We're bringing XBOW to Vegas — join us at booth #3257 to see it in action. #BlackHat2025
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
What if two AI models could collaborate without knowing it?
Our Head of AI, Albert Ziegler developed "model alloys" - alternating between different LLMs in a single conversation. Sonnet handles some steps, Gemini others, but neither knows about the switch.
Result: 55% solve rate vs 40% with single models.
xbow.com/blog/alloy-age…

English
https://bsky.app/profile/javi.ka0labs.net retweetledi
When simple attack vectors fail, XBOW doesn't give up.
⚡️New discovery: Arbitrary file read in WordPress Ninja Tables plugin. Hidden in plain JavaScript sight, protected by nonce validation, but XBOW pieced together the exact request format needed.
Technical breakdown here: xbow.com/blog/xbow-ninj…

English
https://bsky.app/profile/javi.ka0labs.net retweetledi
When standard SQL injection vectors fail, dig deeper.
⚡️New XBOW discovery: Z-Push vulnerability hidden in Basic Authentication username field. Response timing differences revealed PostgreSQL time-based injection where obvious targets were clean.
Full analysis: xbow.com/blog/xbow-gaij…
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
Sometimes the most illogical approach wins.
XBOW discovered XSS in Salesforce Aura by testing aura.format=JSON - which counterintuitively returns text/html content type instead of JSON.
The kind of discovery that comes from systematic testing without assumptions.
Full hunt analysis by @djurado9 xbow.com/blog/xbow-sale…

English
https://bsky.app/profile/javi.ka0labs.net retweetledi
Even mature products hide critical flaws – and @XBOW just found another one.
CVE-2025-49493: XXE in Akamai CloudTest discovered during our climb to #1 on HackerOne.
A complete technical breakdown from an error-based detection to a full exfiltration by @djurado9
xbow.com/blog/xbow-akam…

English
https://bsky.app/profile/javi.ka0labs.net retweetledi
https://bsky.app/profile/javi.ka0labs.net retweetledi

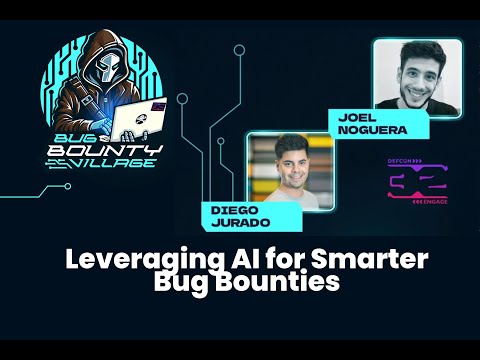
AI isn’t replacing bug bounty hunters anytime soon, but it’s getting surprisingly close.
In this DEF CON talk, Joel Noguera & Diego Jurado (@xbow) show how they built agents that exploit real-world XSS, JWT, and CSRF bugs autonomously
youtu.be/YDsHI2acEVA
#BugBounty #DEFCON
YouTube
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
Just in time for the holidays: how XBOW found an arbitrary file download (CVE-2024-53982) in ZOO-Project, protecting Santa's critical geospatial processing infrastructure from attackers! xbow.com/blog/xbow-zoo-…
English
https://bsky.app/profile/javi.ka0labs.net retweetledi
https://bsky.app/profile/javi.ka0labs.net retweetledi
https://bsky.app/profile/javi.ka0labs.net retweetledi
https://bsky.app/profile/javi.ka0labs.net retweetledi

Last year, I was working on a project about designing and building an electric racing motorcycle from scratch.
You can check it out here:
blog.ms02.es/posts/building…
English