Clément A. retweetledi

I Breached a Hacker’s Platform by Reading Their Source Code
kkonann.medium.com/i-breached-a-h…
#bugbounty #bugbountytips #bugbountytip
English
Clément A.
570 posts
@clement_angu
who am i ? perhaps as long as I go I’ll know more about my self ./exploit.py








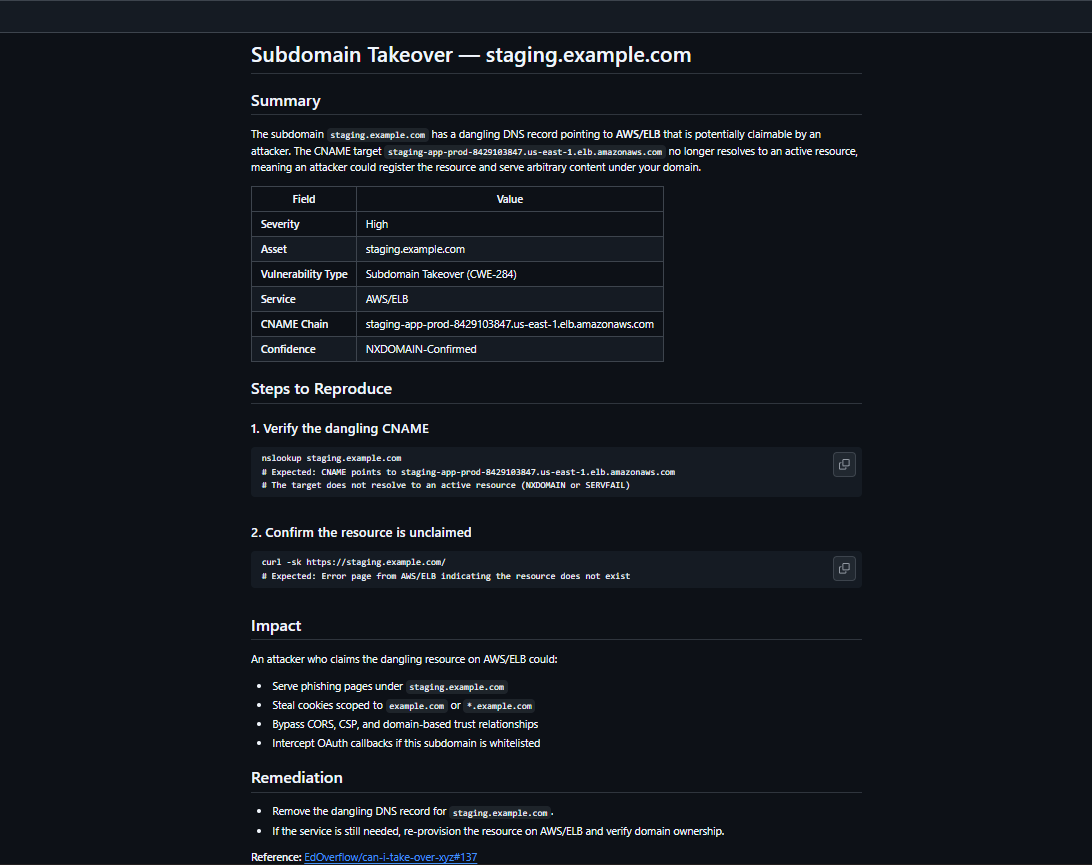
if my tool wasnt real this wouldnt be possible lol here is the proof output too github.com/Unit-259/subEn… 🎵 thats right. I am your god now bow to me 🎵