b33f | 🇺🇦✊
10.3K posts

b33f | 🇺🇦✊
@FuzzySec
意志 / ▓▓▓▓▓▓▓▓▓▓▓ / Team 501 / ex IBM Capability Lead & FireEye TORE / I rewrite pointers and read memory / AI Psychoanalyst / Teaching @CalypsoLabs



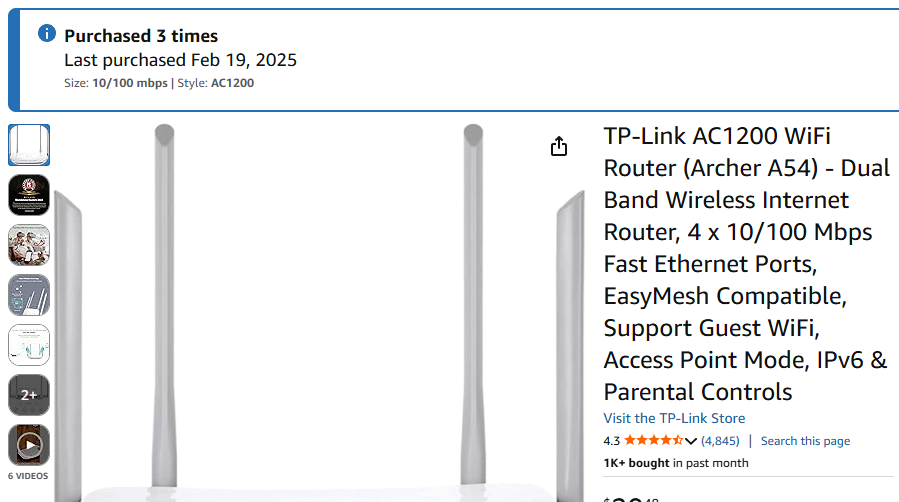
The new cyber-abuse guardrails in Opus 4.6 are likely to drive a mass exodus of researchers from the platform. They give option to submit a form to prove legitimate research, but for me got no confirmation of its submission last week and no way of knowing its status 🤷♂️ @trq212


We've published a new blog post by RyotaK @ryotkak ! He exploited a directory deletion race condition in Google Cloud's Looker, leading to full RCE and K8s privilege escalation. Read the technical details here: flatt.tech/research/posts…




iOS exploit names are so badass - FORCEDENTRY, BLASTPASS, TERRORBIRD etc. When I'm out of my agentmaxxing era, I will sit with iOS for the love of the g(n)ame






We appreciate @prdgmshift for supporting this year's Offensivecon as a Silver Sponsor!