swtl retweetledi

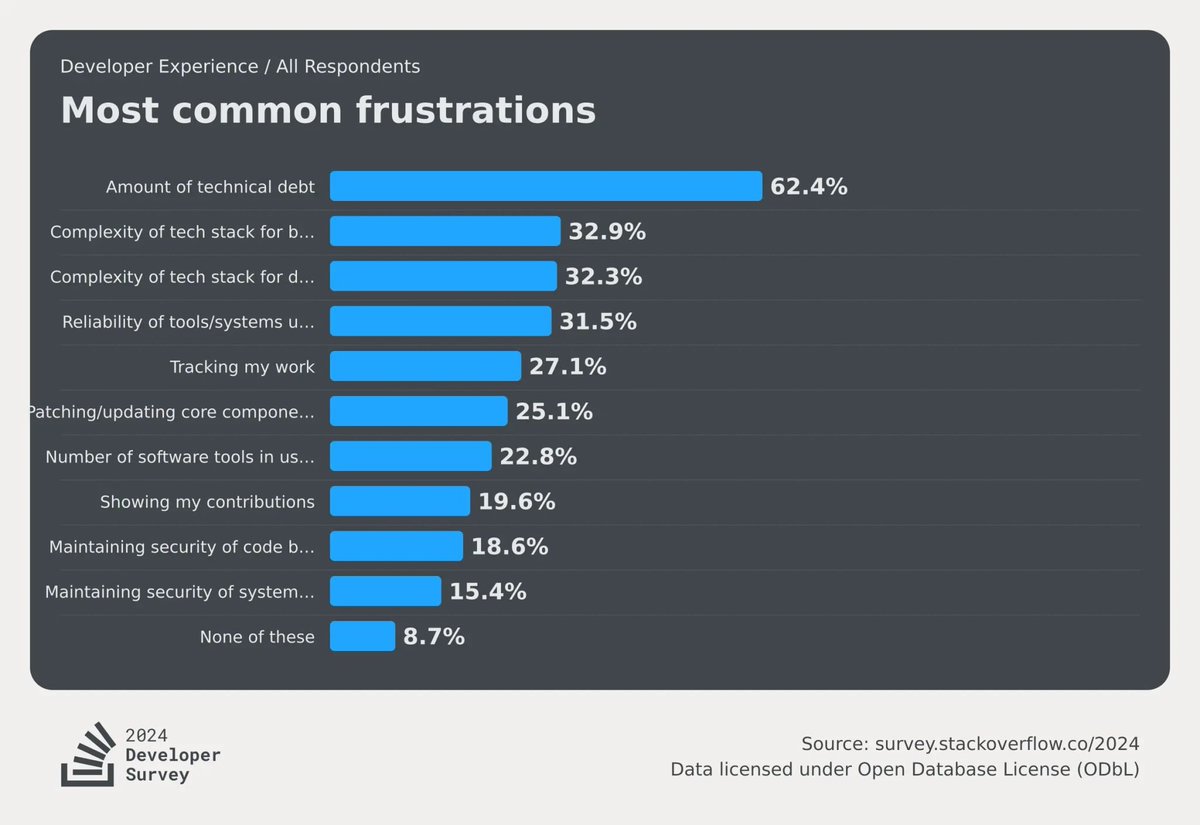
𝗛𝗼𝘄 𝗱𝗼 𝘆𝗼𝘂 𝗱𝗲𝗮𝗹 𝘄𝗶𝘁𝗵 𝗧𝗲𝗰𝗵𝗻𝗶𝗰𝗮𝗹 𝗗𝗲𝗯𝘁?
The latest SO survey (stackoverflow.blog/2024/07/24/dev…) identified technical debt as one of the most important causes of developer frustration.
How do you deal with it? What practical methods or strategies did you use to minimize or reduce it?
English