EXPMON
78 posts

EXPMON
@EXPMON_
Advanced sandbox-based system specifically designed and built for detecting file-based zero-day and hard-to-detect exploits. By @HaifeiLi.





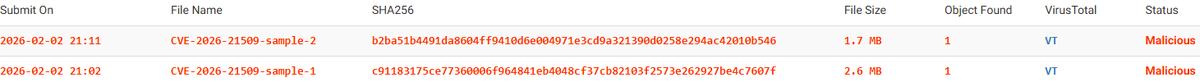
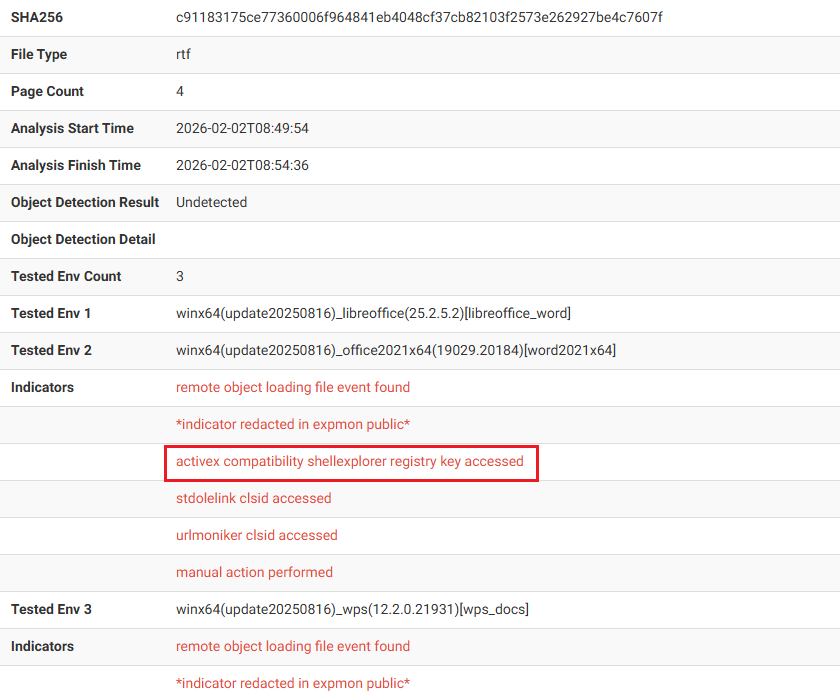
Whoa! This does seem to be a variant if you look at the Relations on VT, and this sample appeared on VT since 2025-11-28, (if confirmed) showing how long this advanced zero-day attack campaign has been ongoing! However, I don't have a VT account, could someone share the sample w/ me or just submit it to pub.expmon.com ? Thanks! x.com/greglesnewich/…

@HaifeiLi Also, the original sample you found has a PCAP on VT that gets a cipher text payload but not the key :( Uploaded traffic here: gist.github.com/g-les/05f6edd8…



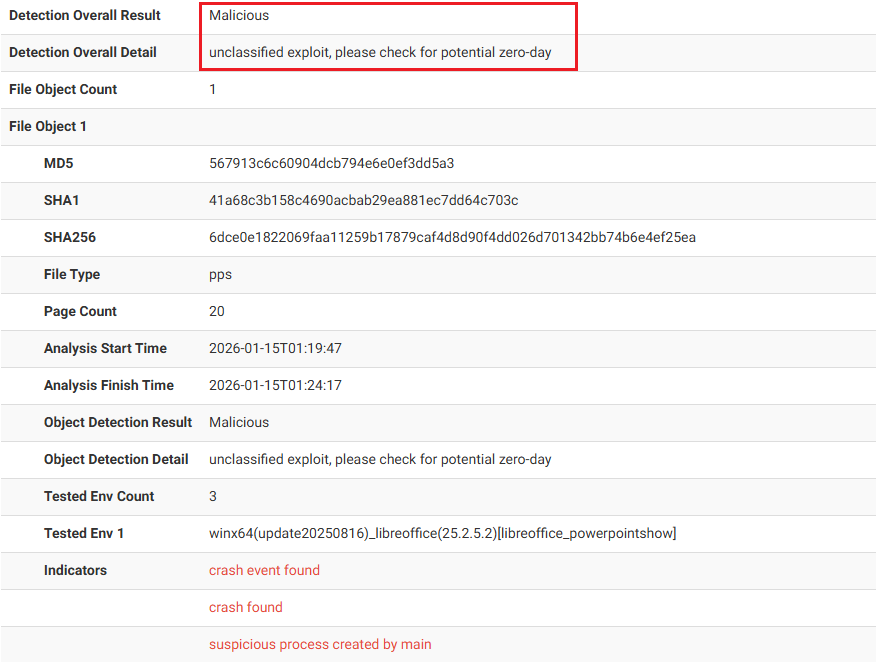
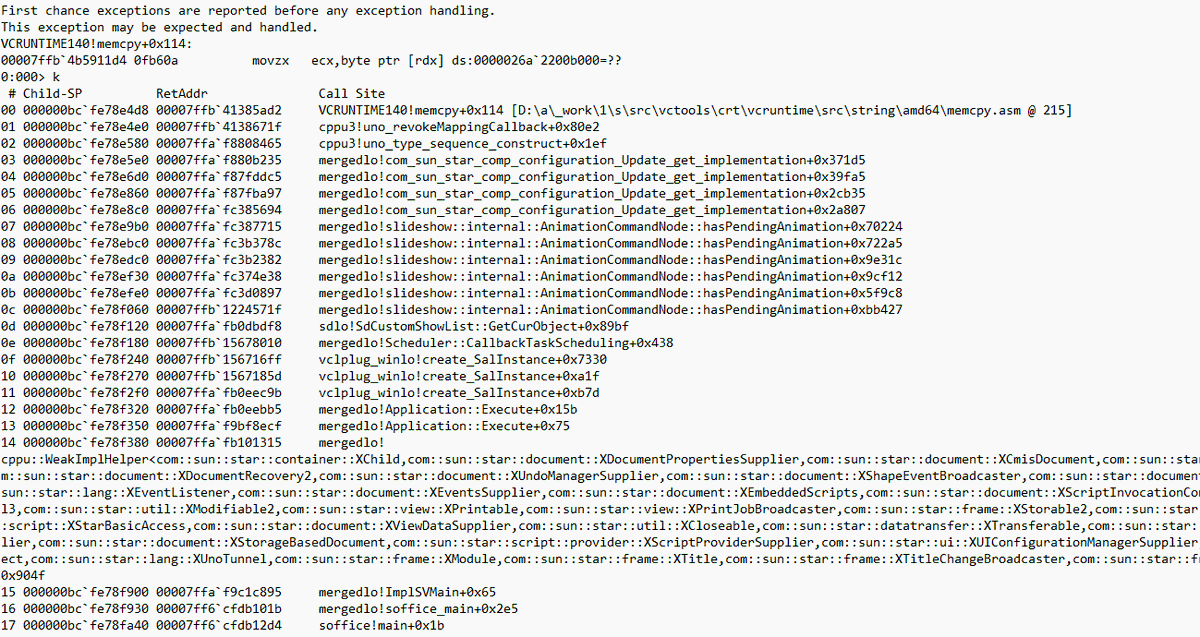
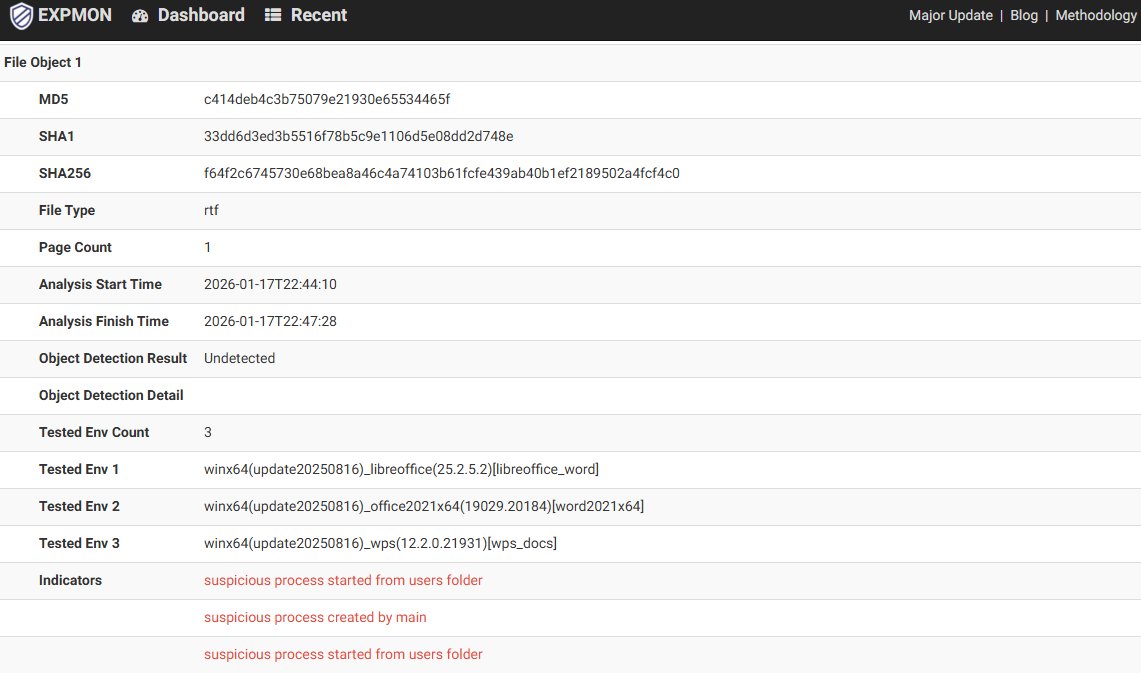
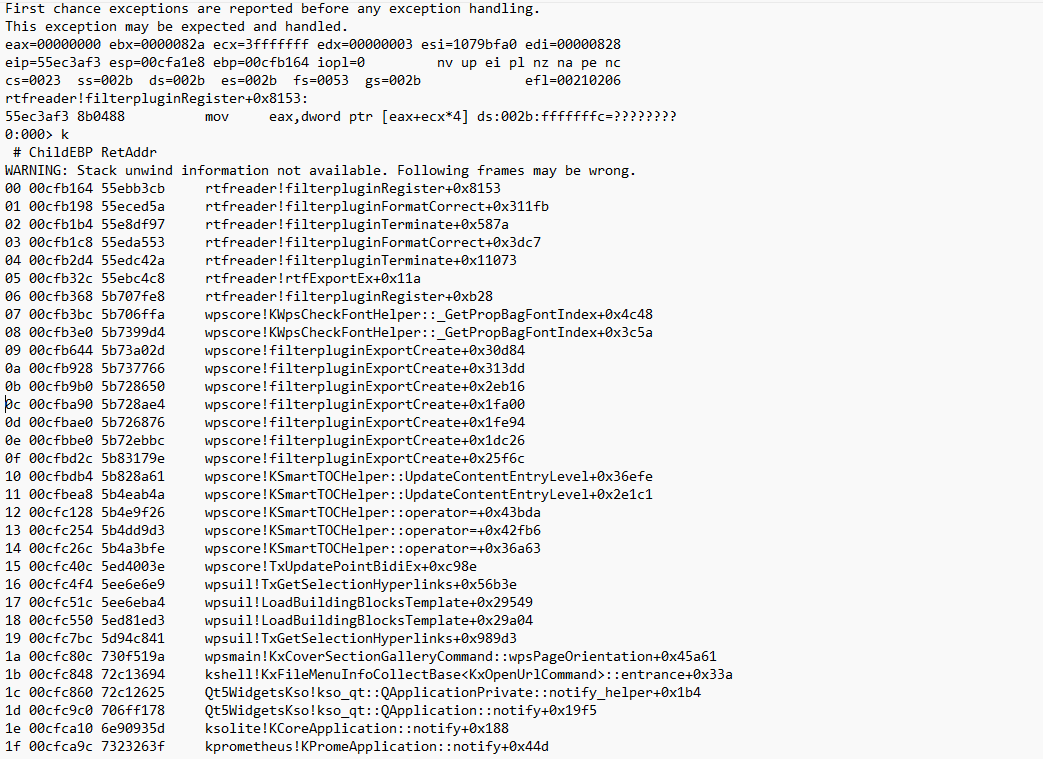
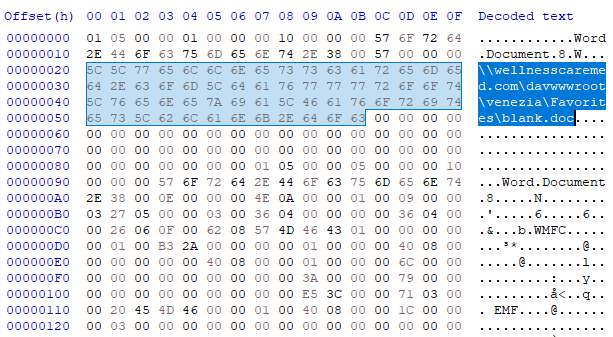
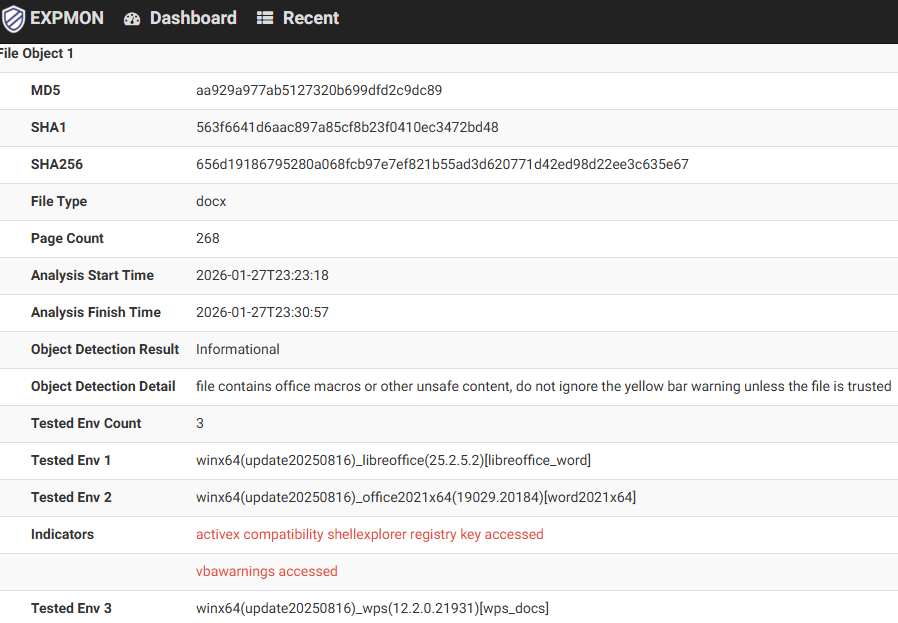
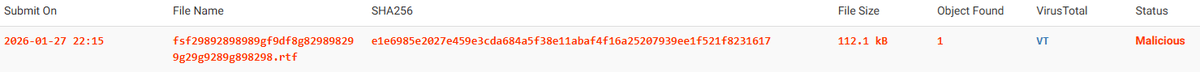
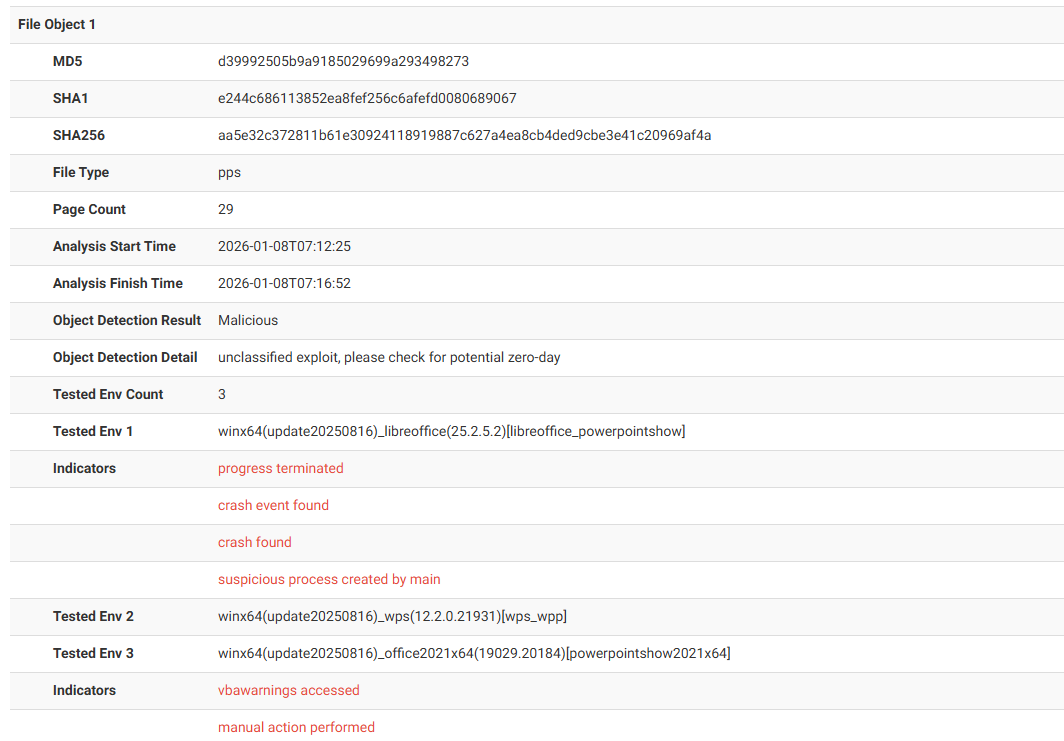
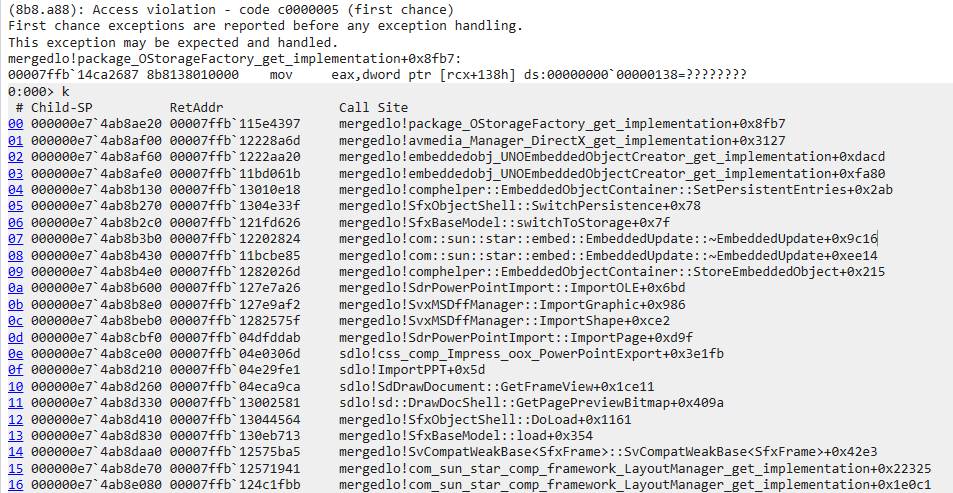
A "wild" submission on EXPMON! On January 17, a suspicious RTF sample was submitted to EXPMON (pub.expmon.com). pub.expmon.com/analysis/31128… While the EXPMON system didn't immediately flag it as "Malicious", it reported multiple highly suspicious Indicators — such as the "suspicious process started from users folder", and the "suspicious process created by main". These Indicators allowed me (and other researchers) to quickly zero in on and investigate the sample. Upon analysis, I've confirmed that it triggered an unpatched crash on the latest version of WPS Office. Since I found no suspicious payload within the sample, I reported it as a potential vulnerability via the ZDI program. Thanks to the ZDI researchers, it was confirmed last week that the crash is technically non-exploitable. Therefore, I am now disclosing the full details. The sample is available for download here (password: "infected"): drive.google.com/file/d/1zBruA0…, so other researchers can investigate this interesting crash. The crash looks like the following attached picture shows. This case once again demonstrates EXPMON's capabilities — not only in detecting in-the-wild zero-day exploits but also in identifying minor suspicious behaviors from an exploit/vulnerability perspective. I have also updated the Detection Logic for WPS to ensure immediate reporting when a suspicious WPS application crash is detected. You can view the re-submission of the sample here: pub.expmon.com/analysis/314933. Some interesting points regarding this submission.. 1. This is the first WPS crash that EXPMON detected since EXPMON covered the WPS Office software in January (justhaifei1.blogspot.com/2026/01/major-…). 2. This is not a normal sample, but a manmade/crafted one, a crash PoC. 3. While this is probably not exploitable, it still looks ugly (an integer overflow?). If you're the vendor (WPS), you may want to patch it. 4. No idea who submitted this, and EXPMON does not track any submitter information. And, yeah, I noted the string message in the sample.. Anyway, thanks for testing EXPMON, I guess.. #expmon #zeroday #0day #wps #threatintel