Josh Krueger
10.3K posts


Josh Krueger
@_defaulty
'You know- you're pretty okay for a guy who talks to himself out loud.' -Me In Public #ThreatIntel #OSINT #SocialEng #IndieGameDev #OptimisticPessimist


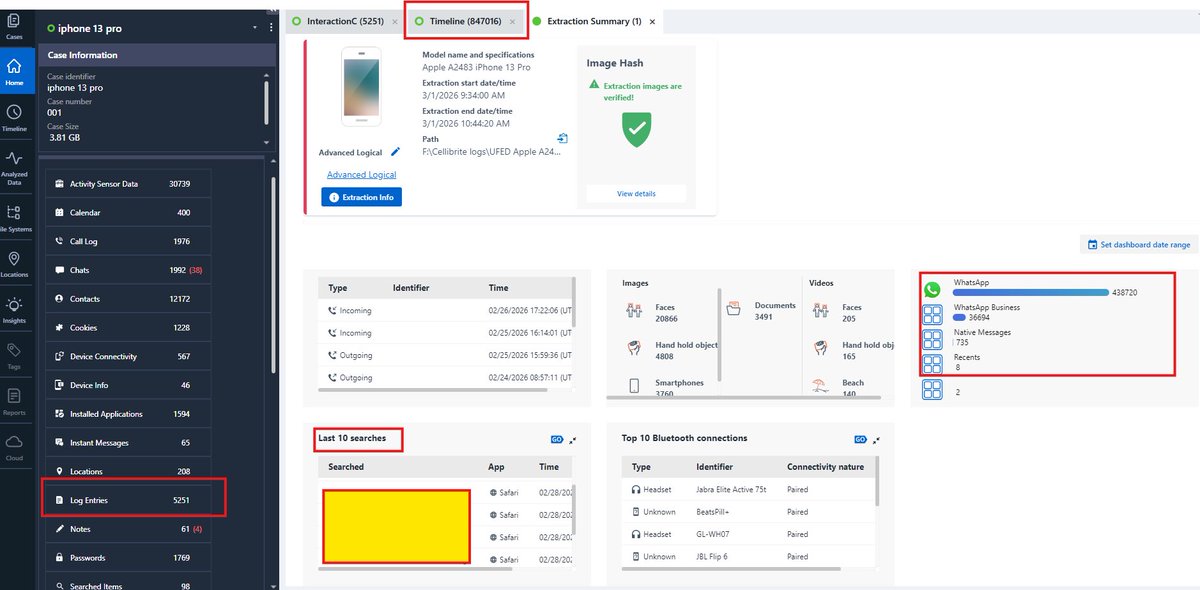

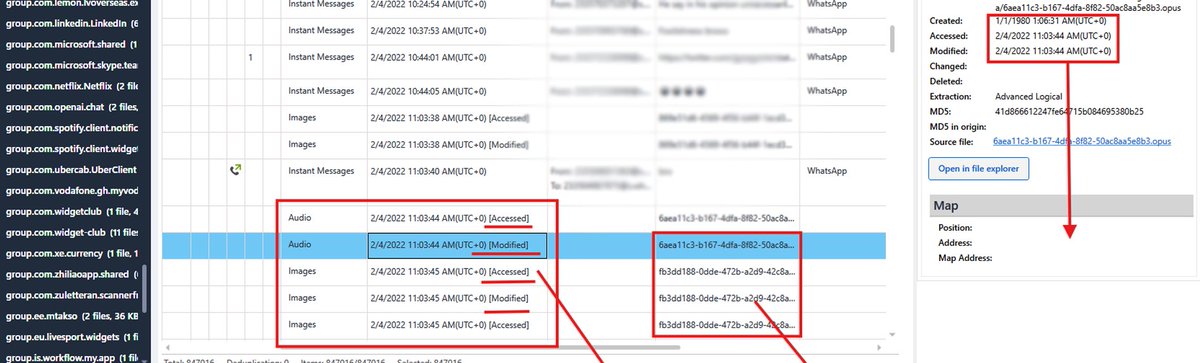
How mobile forensics can uncover a lie even when phone logs are deleted. Someone tells their partner they stayed home all evening and never met anyone. At first glance the phone looks clean. Messages deleted. Call logs cleared. Photos removed. But mobile forensics does not rely on what is visible on the screen. It relies on the traces devices quietly leave behind in the file system. Two days earlier the phone’s search history shows something interesting. Search: cozy restaurants near me. Another search follows a few minutes later. Best cozy restaurants in the restaurant district. Nothing suspicious on its own. Just a search. The evening in question begins at 6:12 PM when the phone is unlocked. At 6:16 PM a ride is requested from a ride hailing app. The pickup location matches the apartment. At 6:20 PM the trip begins. Location artifacts stored by the operating system show the device moving across the city for the next twenty minutes. At 6:41 PM the ride ends in a restaurant district. At 6:42 PM the phone connects to a restaurant WiFi network in that same area. Earlier in the evening a message had been sent to a contact. “I am on my way”. At 6:43 PM a reply “I am inside already” appears in the database. The message had been deleted, but it still lingers in the database even after deletion. At 7:05 PM a photo is taken. The image itself may later be deleted, but the EXIF metadata still records the GPS coordinates of the restaurant. Two minutes later another photo is captured. Face detection records that two people were present in the frame. At 7:12 PM a social media app opens and selects a photo from the gallery for upload. At 9:03 PM another ride is requested. At 9:25 PM the phone returns to the apartment. Now read the original statement again. I stayed home all evening. No single artifact proves anything by itself. But when search history, ride records, location logs, system events, messaging databases and image metadata all point to the same place at the same time, the pattern becomes difficult to dispute. This is what digital forensics actually does. It reconstructs the story a device recorded even when someone tries to erase it. Your phone doesn’t forget, even when you try to erase it. #digitalforensics #DFI #mobileforensics #CyberSecurity

Today, we're introducing Spectre I, the first smart device to stop unwanted audio recordings. We live in a world of always-on listening devices. Smart devices and AI dominate our world in business and private conversations. With Deveillance, you will @be_inaudible.




What is bro doing 😱




i never want to read any other way again.








AS/400 square mug. Get a great grip on your business with the IBM AS/400!