Julian Derry
4.6K posts

@CyberSamuraiDev
Digital Frosenics | Cybersecurity | Manchester United









Exclusive: Legendary director David Lynch left behind a massive estate to his four children and substantial gifts for his close friends. tmz.me/ahrmuOG
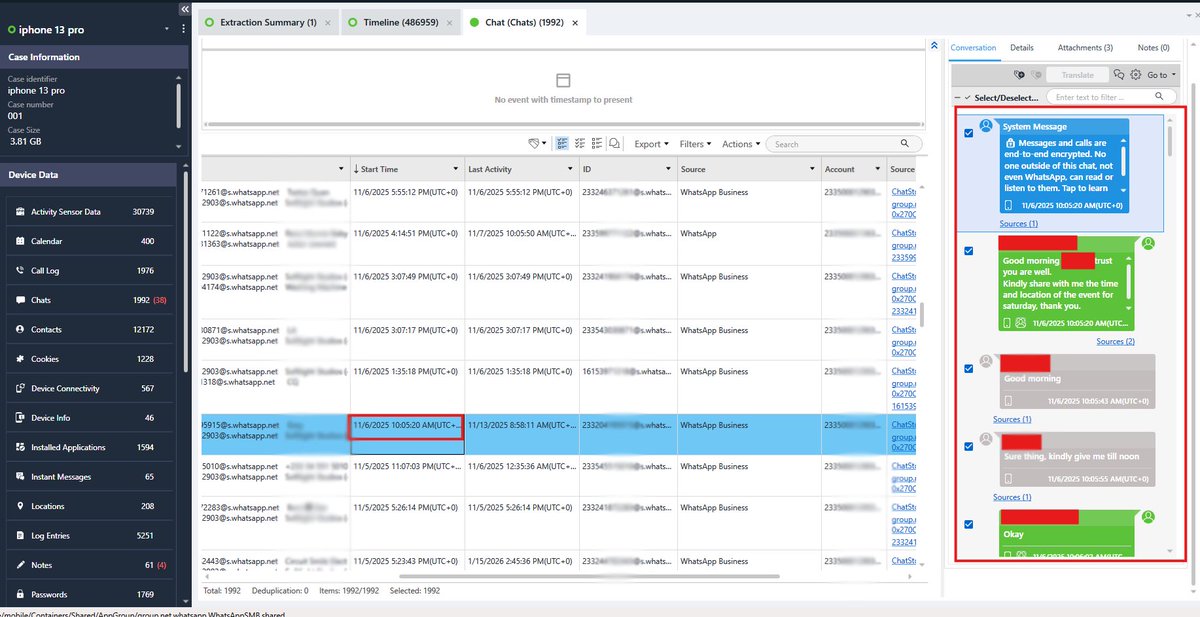
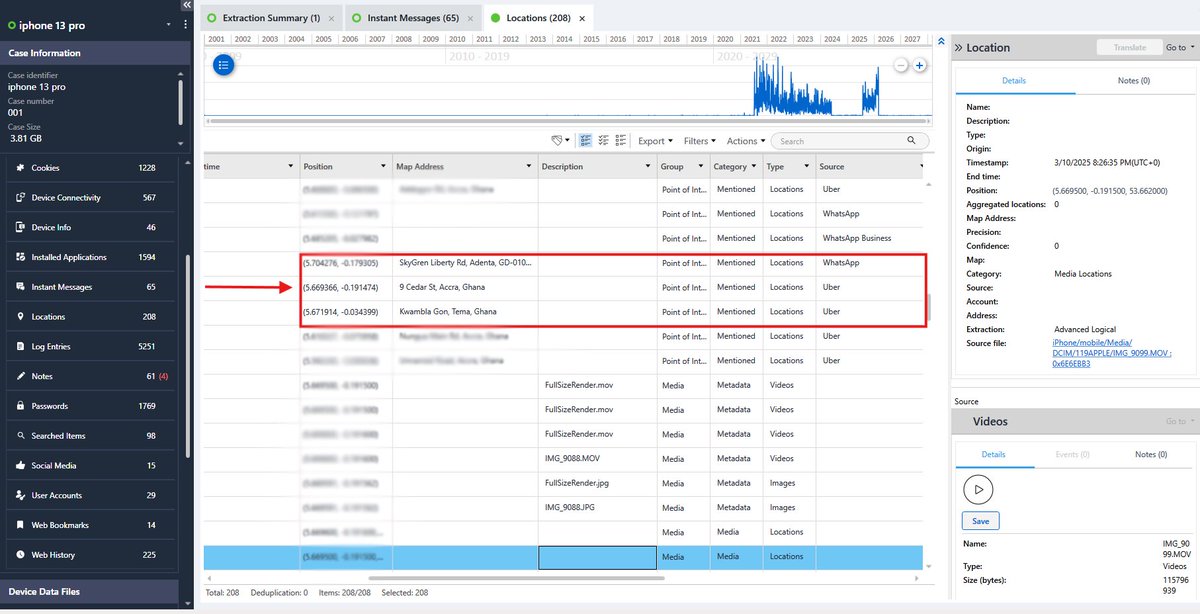
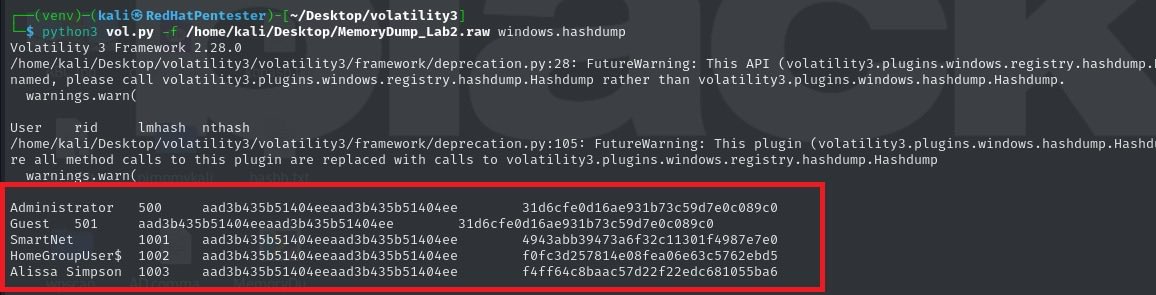
A high-profile environmental activist lost access to his system. His company needed critical data recovered, browser files, password manager credentials… everything. No disk access. Just memory. I loaded the memory dump into Volatility 3. Chrome and KeePass immediately stood out among active processes. From there, I carved out browser artifacts directly from memory and began recovering traces of stored data. Here’s what people underestimate. Even when files aren’t saved to disk, user activity still lives in RAM. Memory forensics isn’t just a backup plan. Sometimes, it’s the only place the truth still exists.







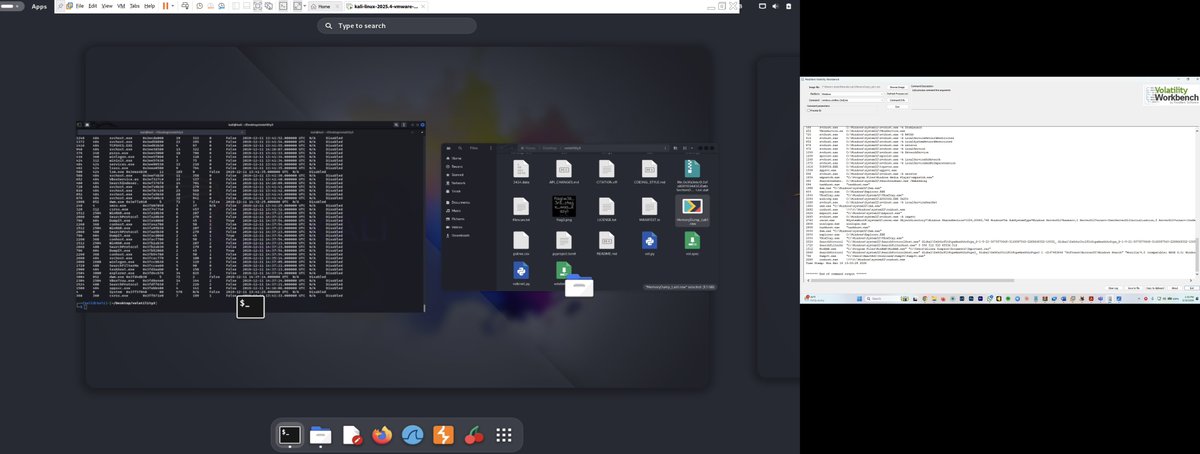
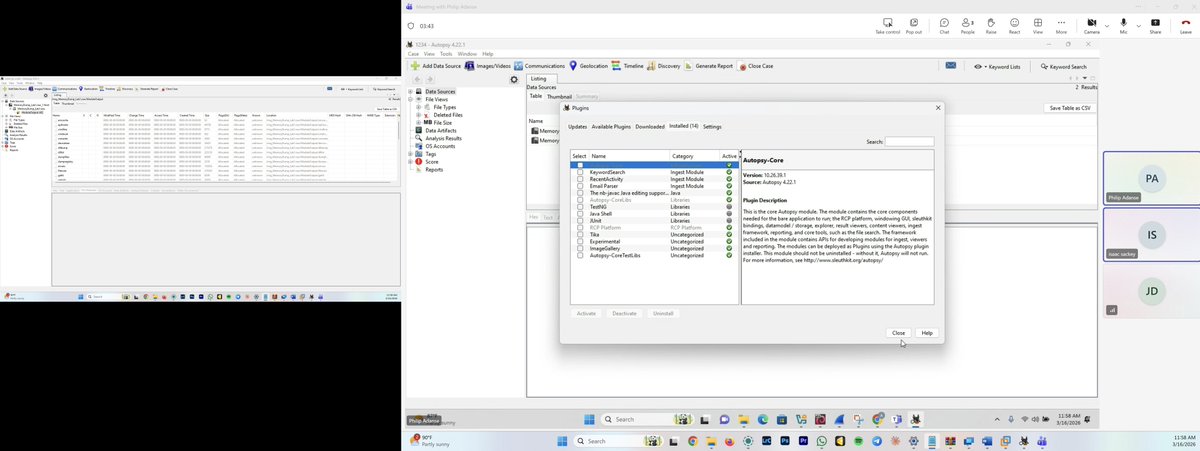

Just wrapped up a really interesting digital forensics lab where I had to investigate a system crash using only a memory dump. Think of memory like the brain of a computer. Even when a device crashes, traces of what was happening seconds before can still be found there. @elormkdaniel @RedHatPentester #DigitalForensics #DFIR #CyberSecurity #MemoryForensics #IncidentResponse #BlueTeam #ThreatHunting #CyberInvestigation

If you think your job is safe because it's 'too complex,' you're just next on the list. No one is safe from the automation wave.



Story time : > there’s this F00L > Blocks me without ever interacting > I block him back too End of story right?? Nahhh, there’s more > the “F00L” gets butt hurted and decided to call me a “fraud” Why??? You may ask??? > Apparently because I post AI generated stories > But there’s more to it > Real reason = “jealousy” > “F00L” wanna go “viral” too > “F00L” wanna be an “influencer” too > but “F00L” can’t, so “F00L” decided to just focus on hating instead of been a “real” cybersecurity professional > but “F00L”doesn’t know He messed with the wrong dude > now “F00L” I’ve never asked anyone for money on here, begged for a job or even sold a course to anyone. > I’ve never claimed to be a Pro, Infact I tell everyone that generally I’m still learning myself. > now if “F00L” can’t prove that I’m a fraud, we are gonna have serious issues > Finally once I notice you are in support of “F00L” too, I’ll do you the favor for your mental health and block your ass too CRY!!!!!!!!!