Tweet fixado

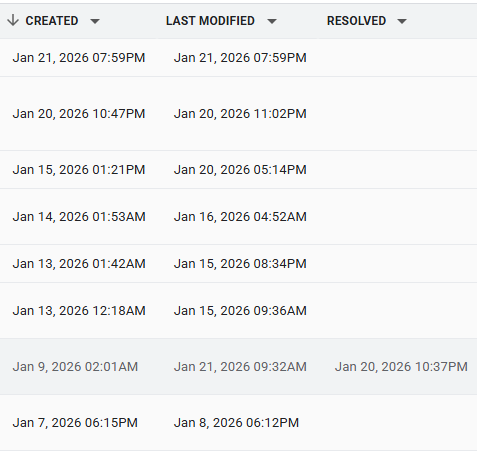
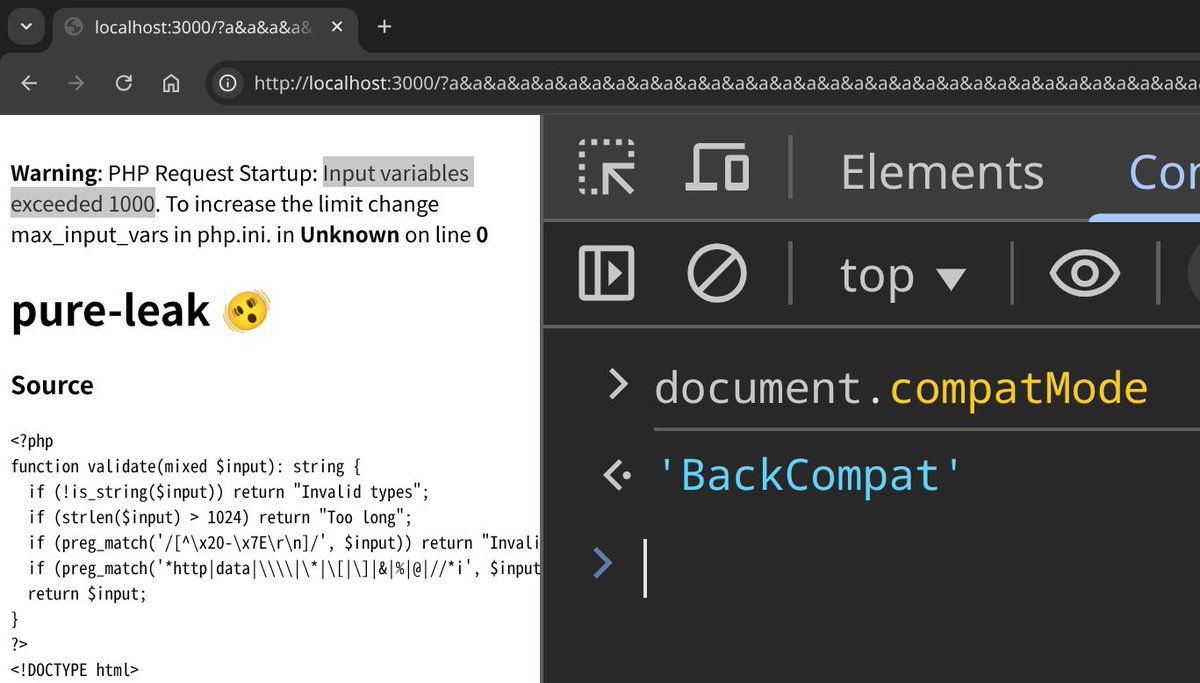
I began looking into browser security issues again in 2026 and while reviewing extension permission APIs, I noticed that the default declarativeNetRequest API (which only requires permission to block content on all pages) can be leveraged into a side-channel attack.
This permission ends up allowing an extension to infer the full URL of open tabs without requesting the chrome.tabs permission, and it can also leak the full URL of cross-origin redirects.
Unfortunately, fixing this issue has been deemed unrealistic by Chrome, and the risk has been accepted, so it is worth keeping this in mind when granting content-blocking permissions to browser extensions.
The complete public report can be found at issues.chromium.org/issues/4792584….
English