Tech Curious
3.2K posts


Tech Curious
@TechDataCurious
Tech, data, crypto beginner-enthusiast trying to make sense of it all






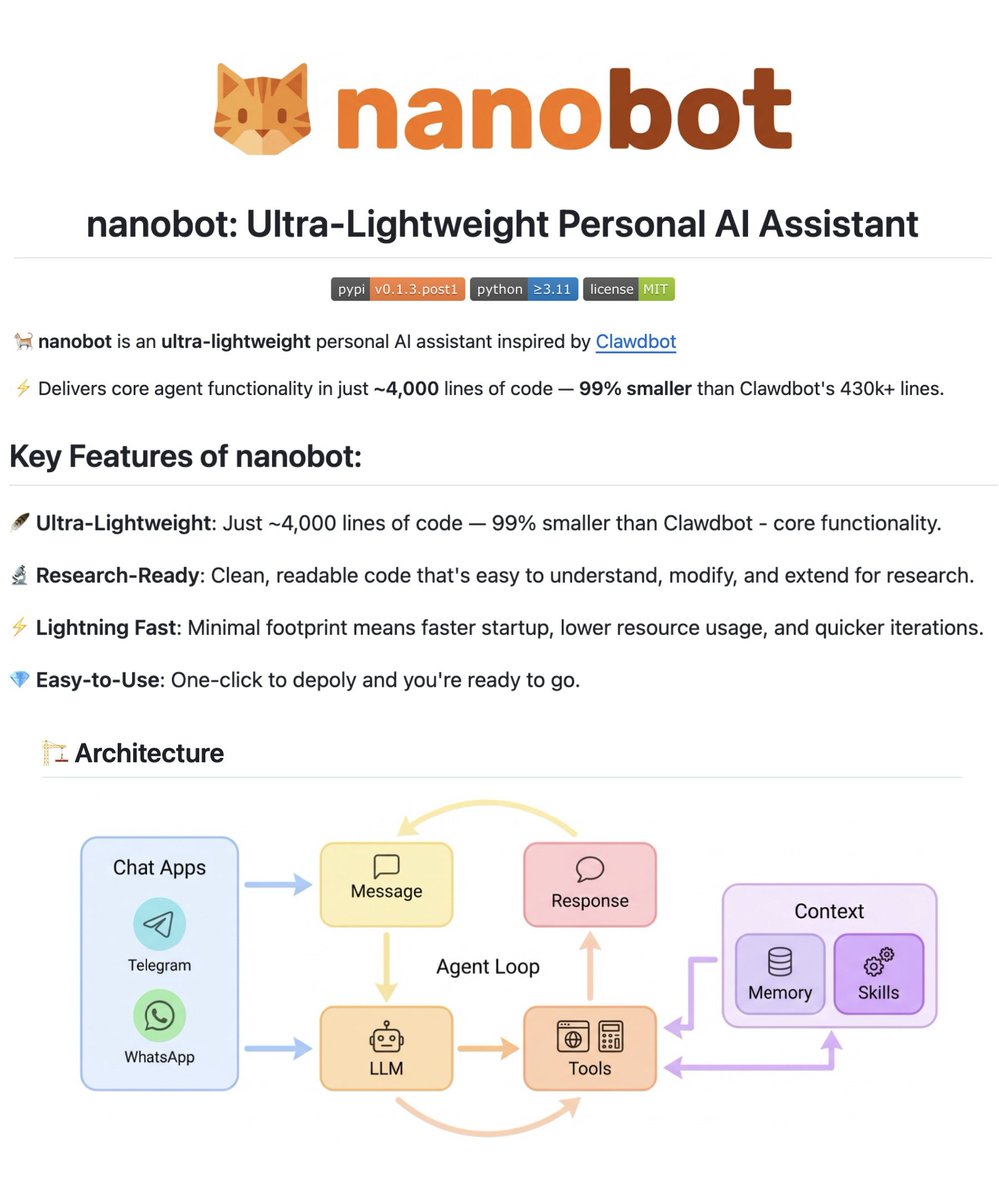



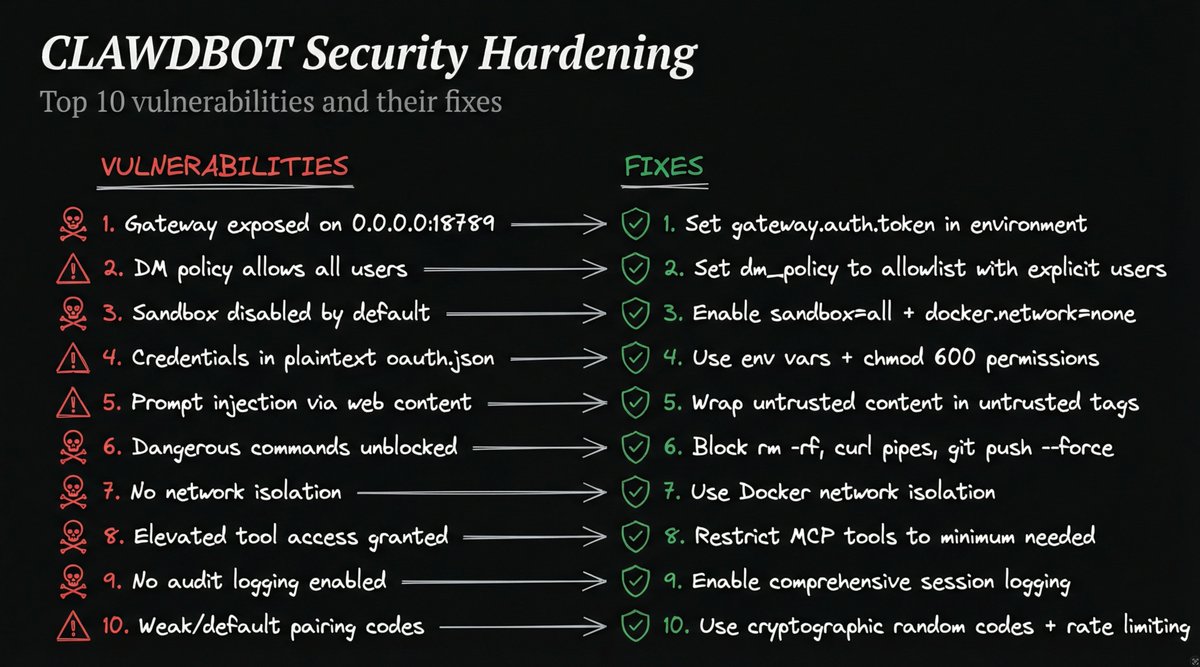

MoltBot shows what agentic AI can really do when software has memory, autonomy, and deep system access. It also exposes a gap most security models weren’t built for. When agents store tokens, configs, and long-term memory as plain text on disk, a compromise doesn’t just expose credentials, it leaks context too. Security for agents can’t be a one-time approval. It’s about continuously mediating it. @jmeller breaks it down ⤵️ bit.ly/4boMvVX


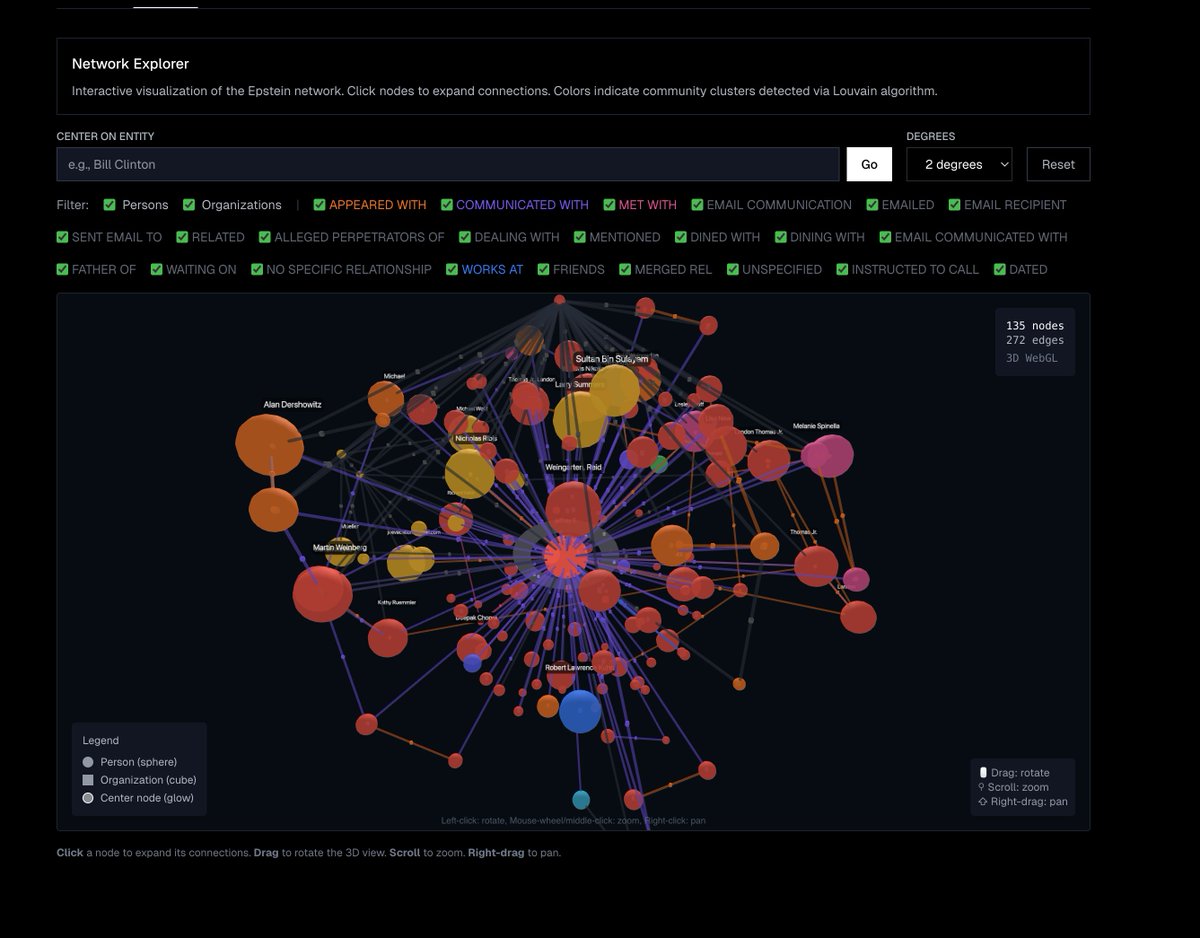

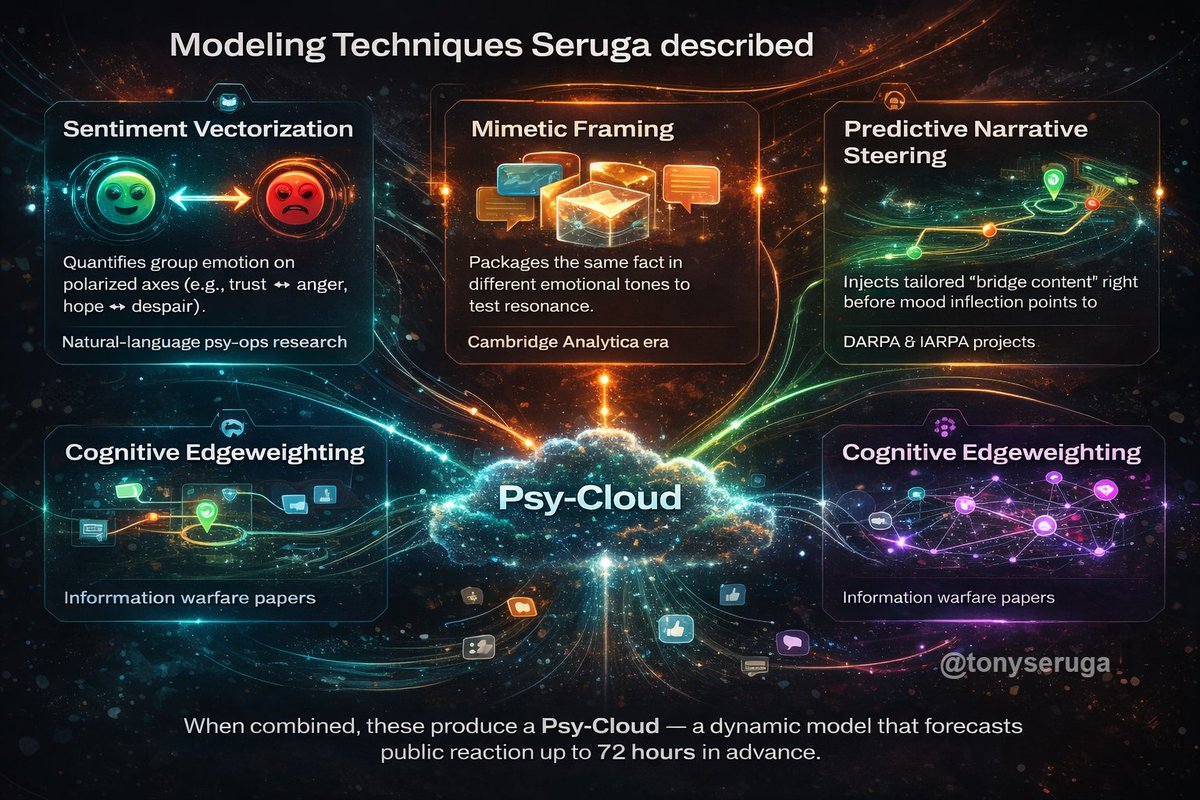
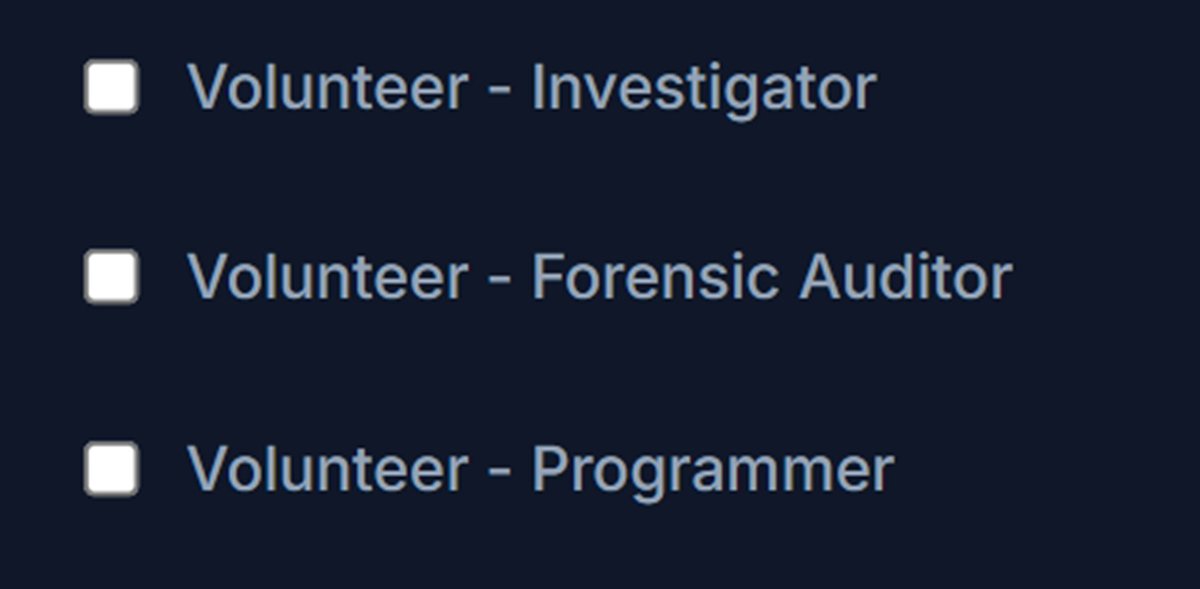
My partners and I have been lifelong data scientists. We own the digital ID of every mobile device/computer in the U.S. and have indexed and archived every IP address in the world. Our extensive experience in big and deep data, including geotracking and geolocation, makes our dozens of data companies the top authority for providing data to corporations, law enforcement, and U.S. government agencies like the CIA, NSA, DoD, DIA, NGA, NRO, FBI, as well as Interpol and foreign intelligence organizations. The Deep State and Institutions hate me for a reason. Here are a handful of my most requested resources: Voice Against Corruption Secure Whistleblower Reporting Portal Report corruption, election irregularities, financial misconduct, or foreign influence with confidence. We prioritize your safety and anonymity. Since December 2025: We have received over 30,000 whistleblower reports, 57% were insiders reporting fraud at the local, state, and federal levels, over 1,000 are legislative staff for our Congress and Senate, 11 reporting that it was their Republican employers that killed DOGE! We are also programming tools for citizen journalists, researchers, and Open-Source Intelligence (OSINT) aficionados to uncover corruption and government overreach. 🚨 Exposing the Global Arms Trade For example, we are building an app to trace hidden overlaps between arms shipments and humanitarian logistics, using open data and primary logistics nodes to identify conflicts by conflict zone or transit hub, i.e., airports, ports, and humanitarian staging grounds. Cross‑reference official flight logs and transponder logs using sites that archive ADS‑B telemetry for cargo aircraft, check donor/aid databases, including procurement contracts, identify shell contractors, analyze export data, incorporate customs and trade visualization tools, then cross‑relate NGO activities, track financial trail, and incorporate pattern recognition, identifying logistical laundering. Basically, we're building a multilayer timeline that links: ➡ Arms exports → (official trade data) ➡ Aircraft and shipping movements → (ADS‑B & AIS telemetry) ➡ NGO procurement and donor funding → (open procurement APIs) ➡ Conflict event data → (for context, like ACLED or Uppsala Conflict Data) When those patterns overlap — e.g., simultaneous spikes in “medical shipments,” procurement contracts to logistics firms, and cargo flights from airbase hubs — you’ve found a laundering signature. The antidote to hidden warfare is open data. Every satellite ping, customs code, and procurement line item is a clue — but only if people look. This tool will connect all of the dots, giving the user solid intelligence on current arms trade movements, including interceptions by bad actors and rogue nations. But to continue our work, we need volunteers, i.e., data analysts, forensic accountants, investigators, and programmers. Visit: voiceagainstcorruption.com Optin by checking the appropriate boxes toward the bottom of the form, identifying how you can help. Be sure not to check 'I wish to remain fully anonymous'. Best OSINT Resources—Tools, Websites & Intelligence Leak Aggregators exponentialthink.com/OSINT/ Unredacted Jeffrey Epstein Black Book—Full unredacted copy of Jeffrey Epstein's contact list (commonly known as the "little black book"). exponentialthink.com/privacy/epstei… Major Conspiracy Theories Overview—Curated list of prominent conspiracy theories with sources and explanations exponentialthink.com/OSINT/conspira… Private Investigator & Skip Tracer Tools—Comprehensive list of databases, surveillance equipment, digital forensics tools, and case management software for licensed investigators. exponentialthink.com/OSINT/pi.html