spacemoth ретвитнул

Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign thehackernews.com/2026/04/bitwar…
English
spacemoth
898 posts


@_spacemoth
https://t.co/rZY4BbgWrj https://t.co/Bu97j1XONG https://t.co/ehvpjvCEXx






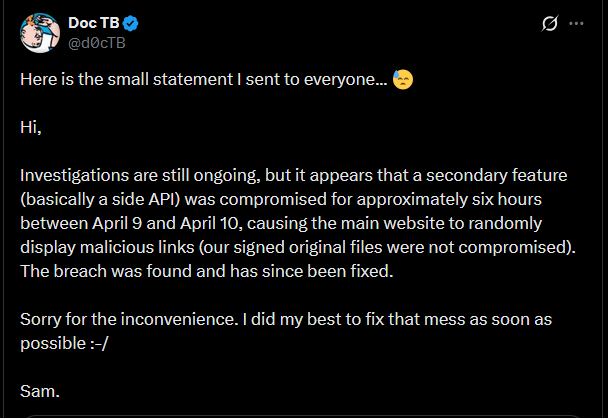






Web applications are only as trustworthy as their servers, and servers can get hacked. Introducing WEBCAT: it lets web browsers verify the origin of code before it runs. 🌞 Today, WEBCAT enters alpha testing! If you like to experiment with cutting-edge software, give it a try: